
Attribute-Based Access Control (ABAC)

In today’s digital landscape, data security is of paramount importance. As organizations grapple with the ever-increasing volume of sensitive information they must protect, the need for robust access control mechanisms becomes more critical than ever. This is where attribute-based access control (ABAC) comes into play.
ABAC is a powerful and flexible approach to access control that uses attributes to determine who can access specific resources and under what conditions. By considering a wide range of factors, ABAC enables organizations to create granular access control policies that can adapt to the complex and evolving needs of modern businesses.
What is Attribute-Based Access Control (ABAC)
Attribute-based access control is a method of regulating access to resources based on attributes associated with the user, the resource, the action, and the environment. These attributes can include a variety of factors, such as the user’s role, location, time of day, and the sensitivity of the data being accessed. ABAC allows for fine-grained access control, enabling organizations to create sophisticated access control policies that can be easily adapted as business requirements change.
In contrast to traditional access control models, which often rely on static roles or access control lists, ABAC offers a more dynamic and context-aware approach. By evaluating multiple attributes in real-time, ABAC can make more informed decisions about whether to grant or deny access to a particular resource.
Example:
Let’s consider a healthcare organization that needs to protect sensitive patient data. Using ABAC, the organization can create policies that allow doctors to access patient records only during their working hours and from within the hospital network. These policies can be easily expressed using attributes such as the user’s role (e.g., doctor), the time of day (e.g., between 9 AM and 5 PM), and the network location (e.g., hospital IP range).
Here’s an example of how such a policy might be implemented in code:
Python
def check_access(user, resource, action, time, location):
if user.role == "doctor" and resource.type == "patient_record":
if action == "read" and 9 <= time.hour < 17 and location.ip_range == "hospital_network":
return True
return FalseIn this example, the check_access function evaluates the user's role, the resource type, the action being performed, the current time, and the network location to determine whether access should be granted. This simple example demonstrates the power and flexibility of ABAC in enforcing complex access control policies.
Attribute-Based Access Control (ABAC) vs. Role-Based Access Control (RBAC)
ABAC is often compared to Role-Based Access Control (RBAC), another popular access control method. While RBAC grants access based on a user's role within an organization, ABAC takes a more granular approach. With attribute-based access control, access is determined by a combination of attributes, allowing for more flexible and dynamic access control policies.
In an RBAC system, roles are typically defined using commands like CREATE ROLE. For example:
SQL
CREATE ROLE manager; GRANT SELECT, INSERT, UPDATE ON employees TO manager;
This code creates a "manager" role and grants it specific permissions on the "employees" table. However, this approach can be limiting, as it doesn't take into account other contextual factors that may be relevant to access control decisions.
With ABAC, these additional factors can be easily incorporated into access control policies. For example, a manager's access to employee records might be restricted based on attributes such as their department, location, and the sensitivity of the data they are trying to access.
Attributes in ABAC
ABAC relies on four main categories of attributes:
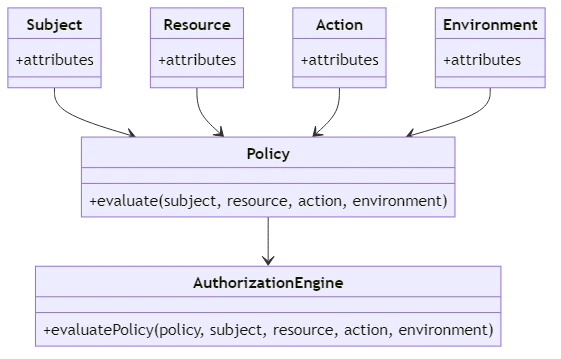
- Subject Attributes: These are characteristics of the user, such as their job title, department, security clearance, and location.
- Resource Attributes: These describe the resource being accessed, such as the type of data, sensitivity level, and owner.
- Action Attributes: These define the action being performed on the resource, such as read, write, or delete.
- Environment Attributes: These are contextual factors, such as the time of day, location, and network security level.
By considering these attributes in combination, ABAC can make more informed and context-aware access control decisions.
Example:
Let's consider a financial institution that needs to protect sensitive customer data. Using ABAC, the institution can create policies that restrict access to customer records based on a combination of attributes, such as the user's role, the sensitivity of the data, and the time of day.
Here's an example of how such a policy might be implemented in code:
Java
public boolean checkAccess(User user, Resource resource, Action action, Environment environment) {
if (user.getRole().equals("financial_advisor") && resource.getType().equals("customer_record")) {
if (action.equals(Action.READ) && resource.getSensitivity().equals("low") && environment.getTime().getHour() >= 9 && environment.getTime().getHour() < 17) {
return true;
}
}
return false;
}
In this example, the checkAccess method evaluates the user's role, the resource type and sensitivity, the action being performed, and the current time to determine whether access should be granted. This code demonstrates how ABAC can be used to enforce complex access control policies that take into account multiple attributes.
Implementing Attribute-Based Access Control (ABAC)
Implementing ABAC involves several key steps:
- Define attributes: The first step in implementing ABAC is to identify the relevant attributes for subjects, resources, actions, and the environment. This process involves working closely with business stakeholders to understand the organization's access control requirements and the factors that should be considered when making access control decisions.
- Create policies: Once the relevant attributes have been identified, the next step is to develop access control policies based on these attributes. These policies should be expressed in a clear and unambiguous manner, using a policy language that can be easily understood and maintained by both technical and non-technical stakeholders.
- Implement the policies: With the policies defined, the next step is to implement them using an authorization engine. This engine is responsible for evaluating the policies in real-time and determining whether access should be granted or denied based on the attributes provided.
- Monitor and refine: Finally, it's important to continuously monitor the system and refine policies as needed to ensure they remain effective and aligned with business needs. This may involve updating attribute values, modifying policies, or adding new policies to address changing requirements.
Benefits of ABAC
ABAC offers several key benefits over traditional access control models:
- Flexibility: ABAC allows for fine-grained access control policies that can adapt to changing business requirements. By considering a wide range of attributes, ABAC can support complex and dynamic access control scenarios that would be difficult or impossible to implement using other models.
- Scalability: As new users and resources are added to an organization, ABAC can easily accommodate them without requiring significant changes to existing policies. This makes ABAC well-suited to large and rapidly growing organizations.
- Improved security: By considering multiple attributes and making access control decisions in real-time, ABAC can help prevent unauthorized access and protect sensitive data from being compromised.
- Compliance: ABAC can help organizations meet regulatory requirements by ensuring that access control policies align with industry standards and regulations. By providing a clear and auditable record of access control decisions, ABAC can help organizations demonstrate compliance and avoid costly penalties.
Challenges of ABAC
While ABAC offers many benefits, it also comes with some challenges that organizations need to be aware of:
- Complexity: Implementing ABAC can be complex, requiring careful planning and ongoing maintenance. Organizations need to have a clear understanding of their access control requirements and the attributes that should be considered when making access control decisions.
- Attribute management: Ensuring that attributes are accurately assigned and kept up-to-date can be time-consuming and resource-intensive. Organizations need to have processes in place for managing attributes and ensuring that they remain accurate and relevant over time.
- Performance: Evaluating access control policies based on multiple attributes can impact system performance, especially in large-scale environments. Organizations need to carefully design and optimize their ABAC implementations to ensure that performance remains acceptable.
- Interoperability: Different systems may use different attribute formats and schemas, making it challenging to implement ABAC across multiple platforms. Organizations need to ensure that their ABAC implementations can integrate with existing systems and support interoperability between different platforms.
Conclusion
Attribute-Based Access Control is a powerful tool for managing access to sensitive data in today's complex digital environments. By considering a wide range of attributes and making access control decisions in real-time, ABAC offers a flexible and dynamic approach to access control that can adapt to the evolving needs of modern businesses.
While implementing ABAC can be challenging, the benefits it offers in terms of improved security, scalability, and compliance make it a valuable investment for organizations looking to protect their data and systems.
As technology continues to evolve and the number of entry points increases, ABAC provides a scalable and efficient way to manage access control and ensure that the right people have access to the right data under the right conditions.
In conclusion, ABAC is a critical component of a comprehensive security strategy in today's digital age. By embracing ABAC and implementing it effectively, organizations can enhance data security, support business objectives, and remain competitive in an increasingly complex and challenging landscape.
