Amazon Aurora MySQL Data Audit Trail
Ensuring the security and integrity of sensitive data within databases is critical for modern organizations. Amazon Aurora MySQL provides robust auditing features to track database activity and ensure compliance with security standards. This article explores how to configure and utilize the native Data Audit Trail in Amazon Aurora MySQL, demonstrates SQL-based implementations, and briefly discusses the enhanced auditing capabilities offered by DataSunrise.
Native Data Audit Trail in Amazon Aurora MySQL
Amazon Aurora MySQL’s native audit trail functionality enables administrators to monitor and log database activities such as data access, modifications, and user actions. These features help answer key questions during audits:
- Who accessed or modified the data?
- When was the data accessed or changed?
- How did the user gain access?
Configuration Steps for Native Audit Trail
To set up native auditing in Amazon Aurora MySQL, you need to enable advanced auditing features via parameter groups. Follow these steps:
Step 1: Create a Custom DB Cluster Parameter Group Access the Amazon RDS console, navigate to the Parameter Groups section, and create a new parameter group. Select the appropriate parameter group family (e.g., aurora-mysql5.7), provide a meaningful name, and save the configuration.
Step 2: Modify Audit Parameters Find the custom parameter group you created in the console and modify its settings. Enable auditing by setting server_audit_logging to ON. Additionally, configure server_audit_events to define the specific events you want to log, such as:
CONNECT, QUERY, QUERY_DML, QUERY_DDL, QUERY_DCL, TABLE
Step 3: Apply the Parameter Group Go to the Modify option for your DB cluster and associate it with the newly created parameter group. Apply the changes immediately to restart the instance and activate the auditing settings.
Step 4: Verify Configuration Connect to the database and execute the following SQL command to ensure the settings are active:
SHOW VARIABLES LIKE '%server_audit_logging%';
Confirm that the value for server_audit_logging is set to ON.
Example: Logging DML Queries
To demonstrate how auditing works for DML queries, follow this example configuration and observe the results:
— Enable auditing for DML queries
SET GLOBAL server_audit_events = 'QUERY_DML';
— Perform database operations
CREATE DATABASE audit_test; USE audit_test; CREATE TABLE audit_log (id INT, description VARCHAR(100)); INSERT INTO audit_log VALUES (1, 'Test Audit'); UPDATE audit_log SET description = 'Updated Audit' WHERE id=1; SELECT * FROM audit_log;
Audit logs generated by these operations can be reviewed in the RDS console under the Logs section of the database instance. Open the relevant log file (e.g., audit/audit.log) to view detailed activity records.
Advanced Features with DataSunrise
While native auditing in Amazon Aurora MySQL offers essential capabilities, DataSunrise enhances these functionalities with centralized, fine-grained control over database security and compliance.
Benefits of DataSunrise
Centralized management ensures uniform control over auditing rules across multiple databases. Flexible filters allow administrators to configure rules for specific query types, objects, and user groups. Advanced threat detection identifies SQL injection attempts and other suspicious activities, while session monitoring audits key session events, such as logins and disconnections.
Setting Up DataSunrise for Aurora MySQL
Creating a DataSunrise Instance
Open the DataSunrise web interface to initiate the configuration process for your Aurora MySQL instance. During this setup, administrators are required to input accurate database credentials, specify the intended target database, and establish comprehensive auditing policies tailored to their organizational needs. The intuitive interface simplifies the setup while ensuring that critical security parameters are configured effectively.
Viewing Audited Logs
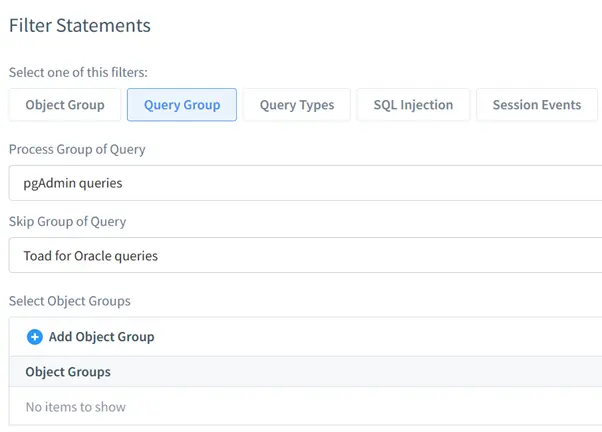
Logs generated by DataSunrise are systematically organized and accessible through its dashboard. Administrators can utilize an array of filters to refine and analyze audit logs efficiently. These filters include:
- Object Group: Enables the filtering of logs based on database objects, allowing for focused analysis of specific tables or schemas.
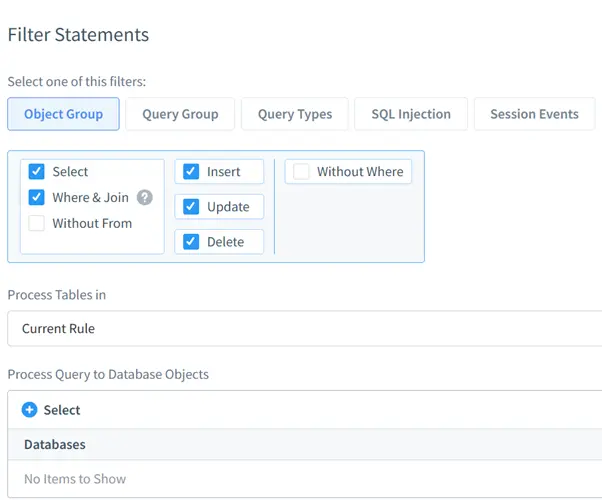
- Query Group: Facilitates the grouping of logs by query types, such as SELECT, INSERT, UPDATE, or DELETE operations, providing a clear breakdown of database activities.
- Query Type: Assists in isolating logs related to SQL injection attempts, offering a proactive means to identify and mitigate security threats.
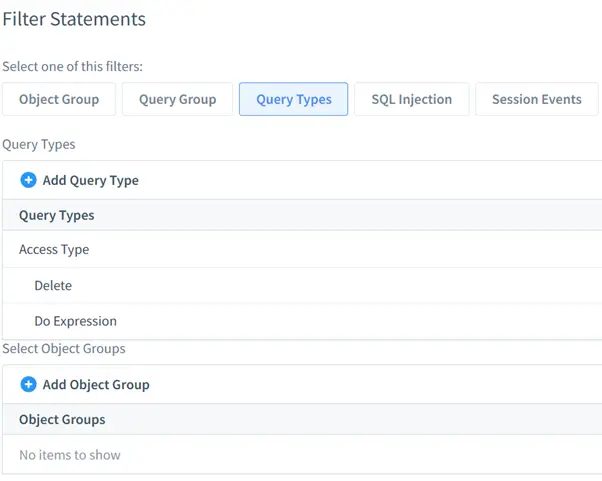
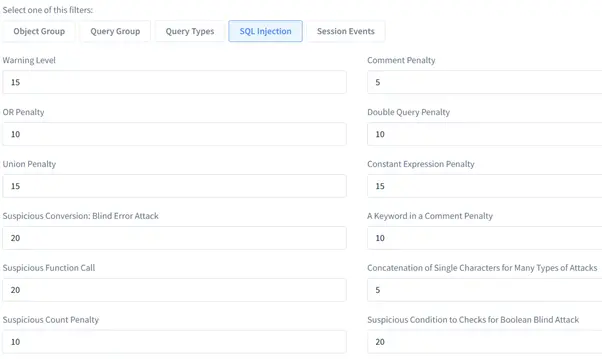
- SQL Injection: Specially designed to filter logs by the specific type of SQL injection detected, ensuring detailed insights into attempted breaches.
- Session Events: Monitors and audits user sessions, including login and logout activities, to maintain a detailed record of user interactions with the database.
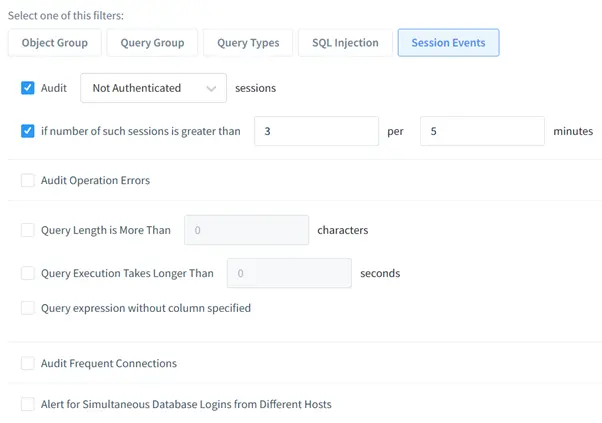
By leveraging these filters, organizations can enhance their ability to pinpoint anomalies, maintain compliance with data security standards, and respond swiftly to potential security incidents. The DataSunrise dashboard provides an invaluable tool for database administrators striving to maintain the integrity and confidentiality of the database environments.
Summary and Conclusion
Amazon Aurora MySQL’s native data audit trail empowers organizations to monitor sensitive data access and ensure compliance with security standards. By leveraging advanced auditing features, you can customize logging to fit your organization’s needs. Complementing these capabilities, DataSunrise provides a powerful, centralized platform for auditing and database security management.
To explore DataSunrise’s full range of features, including its advanced auditing tools, visit our website for an online demonstration.