
Break Glass Access Control: A Key Component of Emergency Security

In the world of IT security, there’s a constant balance between keeping systems secure and allowing necessary access. What occurs when an emergency arises and quick access is necessary? That’s where break glass access control comes into play.
What is Break Glass Access Control?
Break glass access control is a security feature. It permits users to access a system or application during emergencies, even without standard permissions. The concept originates from real-world fire alarms, where one must break a glass panel to sound the alarm.
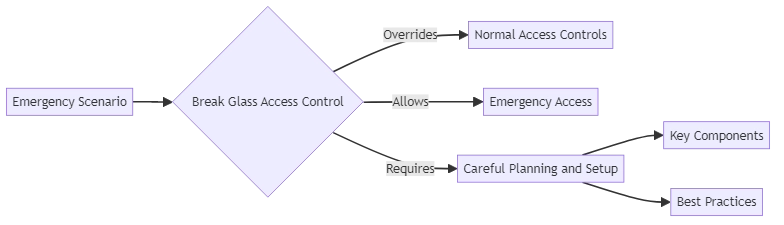
In the digital realm, emergency access control functions similarly. In a controlled manner, it overrides normal access controls to enable emergency access. This could be necessary in situations such as:
- A healthcare provider needing urgent access to patient records during a medical crisis
- An IT admin requiring immediate access to a critical system during a major outage or cyberattack
- Emergency responders needing building plans or hazardous material information during an incident
Users utilize emergency access exclusively in genuine emergencies. Users must not employ it to bypass regular security protocols for convenience. Activating emergency access typically triggers alarms and demands special privileges for deactivation, ensuring users don’t employ it frivolously.
How Does Break Glass Access Control Work?
Implementing break glass access control requires careful planning and setup. Here are the key components:
- Identifying Emergency Scenarios: Define what constitutes an emergency that would warrant emergency access. This varies by industry and organization, but typically includes situations where lives, safety, or critical operations are at risk.
- Setting Up Accounts: Create special accounts with pre-configured emergency permissions. Users only utilize these accounts, separate from regular user accounts, in an emergency.
- Securing Credentials: Users must carefully secure the login credentials for emergency access accounts. Only a few highly trusted individuals should access them. Ensure secure storage, such as in a safe or encrypted vault.
- Monitoring and Alerting: Put robust monitoring and alerting systems in place to detect any use of emergency access accounts. This allows for prompt response and investigation of the emergency.
- Deactivation Procedures: There must be clear procedures in place for deactivating access once the emergency has passed. This typically involves a thorough review of the incident and restoring normal access controls.
Real-World Examples
Various industries use break glass access control to manage emergencies. Here are some examples:
Healthcare
In a medical emergency, quick access to patient records can be life-saving. If a doctor or nurse lacks the usual permissions for accessing a patient’s file, they can use break glass access. This grants emergency access for providing necessary treatment.
IT and Cybersecurity
If a major system outage or cyberattack, IT teams may need immediate access to affected systems. This access is necessary to restore service or mitigate damage. Emergency override accounts can provide rapid response by granting emergency admin access.
Emergency Services
During a fire or other emergency, responders may need immediate access to building plans, utility shutoffs, or hazardous material information. Emergency access systems can ensure that critical information is available when seconds count.
Importance of Careful Break Glass Planning
While break glass access control is a powerful tool for emergencies, organizations must implement it with great care. Improper use of break glass accounts can actually create security risks.
To ensure successful implementation
- Tightly control access to break glass credentials
- Implement strong monitoring and alerting to detect any use of break glass accounts
- Establish and practice clear procedures for activating and deactivating access
- Provide thorough training to individuals entrusted with privileges
- Regularly test break glass procedures to ensure they will work when needed
Organizations can benefit from emergency access by using it only when necessary, which helps to reduce risks.
Best Practices for Break Glass Access Control
Here are some key best practices to follow when implementing break glass access control:
- Require Multi-Factor Authentication: Even for break glass accounts, organizations should use multi-factor authentication to prevent unauthorized access. However, the second factor should be readily available in an emergency. For example, it could be a physical token stored securely.
- Limit Break Glass Privileges: Accounts should have the minimum privileges necessary to address the emergency. They should not have blanket admin rights that they could abuse.
- Use Automatic Timeouts: Break glass access should automatically expire after a set time to prevent prolonged unauthorized use. You can extend the timeframe if the emergency persists, but it should not be indefinite.
- Conduct Regular Audits: All use of break glass access should undergo thorough auditing. Afterward, responsible parties should review it to ensure appropriateness and identify any necessary process improvements.
- Provide Instructions: Users with break glass privileges need clear, step-by-step instructions on activating emergency access. This ensures that people use it appropriately in high-stress emergencies.
Conclusion
Break glass access control is a critical tool for managing emergencies in IT environments. By controlling and auditing emergency access, organizations ensure that necessary actions are swiftly taken in a crisis without compromising overall security.
However, this type of access is not a substitute for good security practices. A last resort measure for true emergencies. Careful planning, strict controls, and regular testing are essential to successful implementation.
Organizations must understand break glass access control principles to effectively handle emergencies. They should also follow best practices to maintain strong security measures.
If you’re interested in learning more about securing your sensitive data and implementing effective break glass access control, we invite you to attend our upcoming demo session featuring DataSunrise.
