
Cloudberry Audit Trail

Cloudberry audit trail functionality enables organizations to maintain precise records of database activities and access patterns. ENISA’s Threat Landscape report shows that organizations with good audit trails detect security incidents 68% faster. We compare this to those without systematic logging. Through native audit capabilities, Cloudberry helps organizations track and analyze database operations while maintaining performance and security standards.
What is an Audit Trail in Cloudberry?
An audit trail for Cloudberry is a record of events and activities within your Cloudberry system. It tracks user actions, data changes, and system access. This creates a detailed log that helps you monitor your data’s integrity. It also helps you find any issues or suspicious activity. Cloudberry provides built-in audit trail functionality that allows businesses to:
- Track file accesses and modifications
- Monitor user actions
- Ensure regulatory compliance (e.g., GDPR, HIPAA)
- Detect potential security threats or unauthorized access
This audit trail feature is particularly important for businesses handling sensitive data, as it ensures transparency and accountability in data management.
Setting Up Basic Audit Trail
To begin tracking database activities, connect to your Cloudberry instance through the CLI. Here’s how to enable basic auditing:
-- Enable audit policy for sensitive data CREATE AUDIT POLICY sensitive_data_policy ON customer_data FOR SELECT, UPDATE, DELETE BY SESSION;
Example output after enabling the audit policy:
| Policy Name | Status | Target Table | Operations | Audit Level |
|---|---|---|---|---|
| sensitive_pii_audit | ENABLED | customer_pii | SELECT,UPDATE,DELETE | SESSION |
| payment_data_audit | ENABLED | transactions | SELECT,INSERT,UPDATE | DATABASE |
| employee_audit | ENABLED | hr_records | ALL | DATABASE |
Creating Custom Audit Views
For better visibility into audit data, you can create custom views:
CREATE VIEW audit_summary AS
SELECT
operation_type,
user_id,
table_name,
timestamp
FROM audit_log
WHERE operation_type IN ('SELECT', 'UPDATE', 'DELETE')
ORDER BY timestamp DESC;
Example output when querying the audit_summary view:
| Operation Type | User ID | Table Name | Timestamp |
|---|---|---|---|
| UPDATE | john.smith | customer_pii | 2024-02-05 09:15:22 |
| SELECT | data.analyst | transactions | 2024-02-05 09:12:45 |
| INSERT | sales.admin | customer_pii | 2024-02-05 09:10:33 |
| DELETE | system.admin | hr_records | 2024-02-05 09:08:17 |
Command Line Interface for Audit Management
Cloudberry’s CLI provides essential commands for managing audit trails:
# Configure audit settings cloudberry audit-config --enable cloudberry audit-policy create --name "sensitive_data_audit" --level "detailed" cloudberry audit-report generate --start-date "2024-01-01" --end-date "2024-02-01"
Example CLI command output:
Audit Configuration Status: ------------------------- Audit System: Enabled Log Directory: /var/log/cloudberry/audit Retention Period: 90 days Storage Usage: 242MB Active Policies: 3
Querying Audit Logs
You can retrieve audit information directly using SQL queries:
SELECT al.timestamp,
al.operation_type,
al.object_name,
al.user_name,
al.client_ip
FROM audit_log al
WHERE al.timestamp >= CURRENT_DATE - INTERVAL '7 days'
ORDER BY al.timestamp DESC;
Example audit log query results:
| Timestamp | Operation Type | Object Name | User Name | Client IP |
|---|---|---|---|---|
| 2024-02-05 15:45:12 | SELECT | customer_pii | sarah.jones | 10.0.15.100 |
| 2024-02-05 15:42:33 | UPDATE | transactions | payment.proc | 10.0.15.121 |
| 2024-02-05 15:40:18 | INSERT | transactions | payment.proc | 10.0.15.121 |
| 2024-02-05 15:38:55 | SELECT | hr_records | hr.manager | 10.0.15.145 |
Enhancing Cloudberry Security with DataSunrise
Cloudberry has good native audit trail features. You can add more security layers to improve protection. This is important when dealing with sensitive data. This is where DataSunrise comes into play.
How to Set Up DataSunrise for Cloudberry
To start using DataSunrise with Cloudberry, follow these steps:
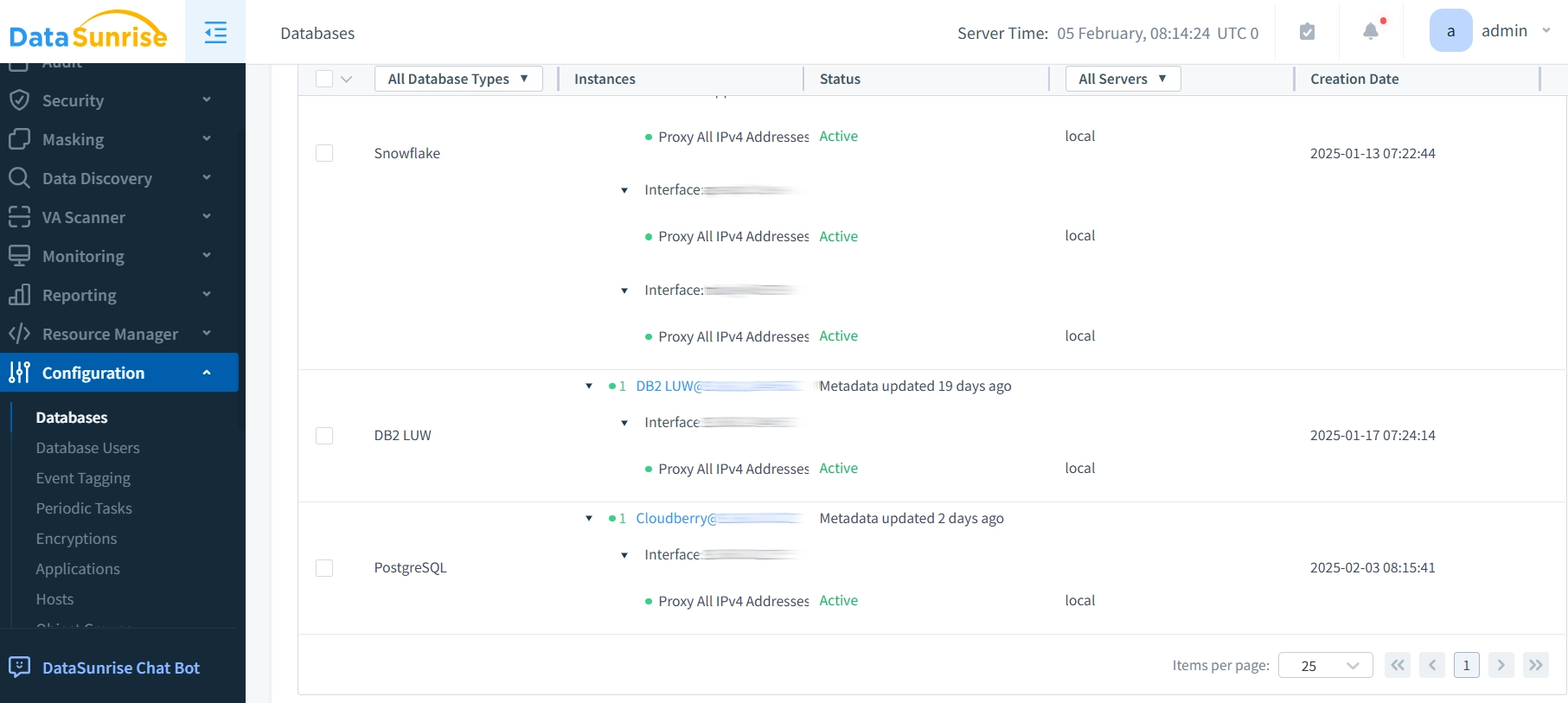
- Install DataSunrise: First, ensure that DataSunrise is installed on your server or cloud environment.
- Connect DataSunrise to Cloudberry Database: DataSunrise needs to connect to the database used by Cloudberry to monitor and apply masking rules.
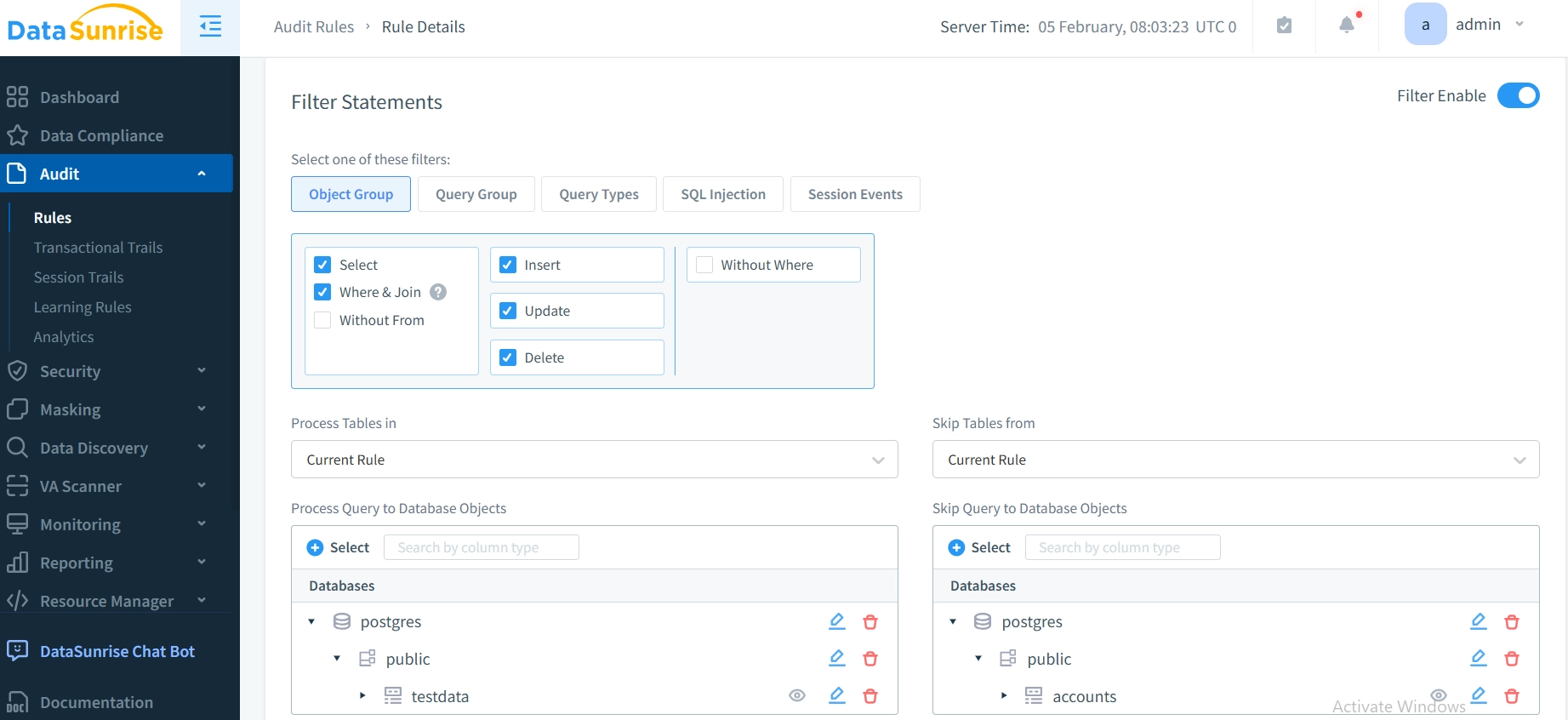
- Define Audit Rules: Set up the audit rules based on your requirements.
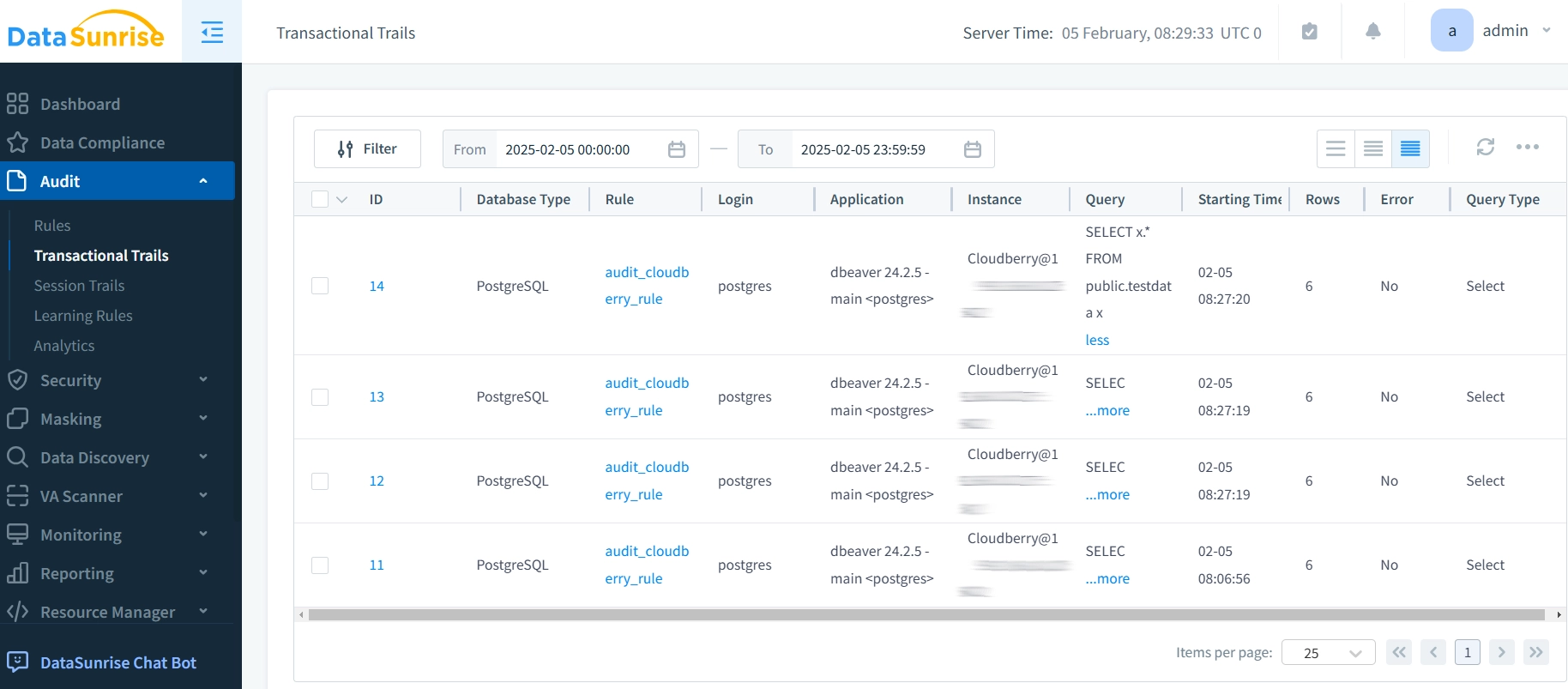
- Monitor and Report: Use DataSunrise to monitor any unauthorized access to sensitive data and generate reports for compliance audits.
Benefits of Using DataSunrise with Cloudberry
- Centralized Security Management: DataSunrise provides centralized control over all masking and auditing rules, ensuring consistent and uniform application across your cloud infrastructure.
- Compliance: DataSunrise helps meet compliance requirements such as GDPR and HIPAA by ensuring sensitive data is properly protected through masking.
- Real-time Monitoring: The platform offers real-time monitoring, alerting you to any potential data breaches or unauthorized access.
Effective Approaches to Database Auditing
Policy Development and Alignment forms the foundation of effective database auditing. Organizations implementing audit trails in Cloudberry environments must establish clear objectives that align with specific compliance requirements. These objectives should specify which data requires monitoring and how to track different types of access.
Access Management Strategy determines the success of audit implementation. By using role-based controls, organizations can manage who can see and change audit logs. This helps stop unauthorized changes to audit records. It also makes sure the right team members can access important information.
Systematic Review Process keeps audit systems relevant and effective. Organizations should establish quarterly assessments of their audit configurations, updating them based on new security requirements or changes in data handling processes. This includes reviewing log retention periods and storage requirements to balance compliance needs with system performance.
Third-Party Integration enhances native capabilities significantly. DataSunrise offers solutions that improve audit capabilities beyond what Cloudberry provides. It enables unified monitoring across different database platforms. It also makes compliance reporting easier. Additionally, it adds advanced security features that fit well with current audit processes.
Conclusion
Effective implementation of audit trails is crucial for maintaining data security and compliance in Cloudberry databases. Native features offer strong tools through command-line options and SQL interfaces. However, organizations with complex security needs may benefit from advanced solutions.
DataSunrise offers cutting-edge database security tools that complement Cloudberry’s native audit capabilities. With features like dynamic data masking, real-time activity monitoring, and comprehensive compliance reporting, DataSunrise provides the flexibility and control modern organizations need. The platform’s enterprise-grade solutions ensure thorough database protection, simplified audit processes, and streamlined compliance management.
Experience these capabilities firsthand by visiting the DataSunrise website and schedule an online demo. Learn how our strong security features can improve your Cloudberry database protection.
