
Continuous Data Protection: Tips & Strategies

In today’s digital landscape, continuous data protection has become a top priority for individuals and organizations alike. As technology dependence grows and organizations store and transmit more sensitive information electronically, they must implement strong data protection measures.
This article will delve into the significance of data protection, emphasizing essential elements like data auditing, security, masking, and solutions for sensitive data.
The Significance of Continuous Data Protection
Data protection is the measures organizations take to keep sensitive information safe from unauthorized access, use, or disclosure. Essential for several reasons:
Legal Compliance
Many industries are subject to strict data protection regulations, such as GDPR, HIPAA, and PCI-DSS. Failing to comply with these regulations can result in hefty fines and reputational damage.
Privacy Preservation
Protecting personal and confidential information is a fundamental human right. Organizations must ensure that they respect individuals’ privacy and handle their data securely.
Business Continuity
Data breaches and security incidents can disrupt business operations, leading to financial losses and damaged customer trust. Effective data protection measures help minimize the risk of such incidents and ensure business continuity.
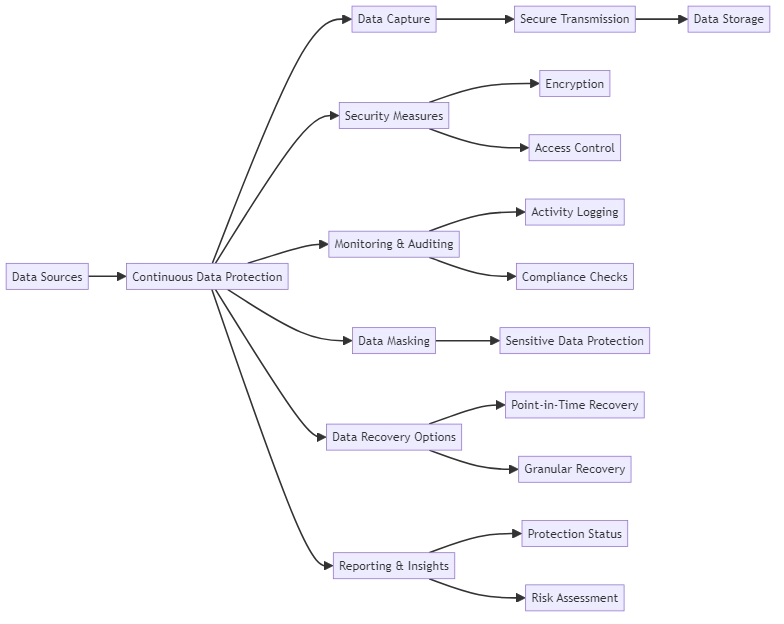
Key components of Continuous Data Protection
Data Auditing: Assessing Your Data Landscape
Data auditing is crucial for data protection. It involves thoroughly examining an organization’s data landscape to identify vulnerabilities and assess compliance with data protection regulations. Additionally, it ensures appropriate security controls are in place. Regular data audits help organizations:
Identify Sensitive Data
By conducting a comprehensive data audit, organizations can locate and classify sensitive information, such as personally identifiable information (PII), financial data, and intellectual property.
Assess Risk
Data audits help organizations assess the risks related to their data. This includes understanding the impact of a data breach or security problem. Organizations can use data audits to identify vulnerabilities and take steps to mitigate them. By conducting regular data audits, organizations can proactively protect their data and prevent potential issues.
Implement Controls
Organizations can use data audits to identify risks. They can then implement security measures such as access controls, encryption, and monitoring systems to mitigate these risks.
Data Security: Protecting Your Valuable Assets
Data security encompasses the technical, administrative, and physical measures organizations employ to protect sensitive information from unauthorized access, use, disclosure, disruption, modification, or destruction. Some key aspects of data security include:
Access Controls
Implementing strong authentication mechanisms, such as multi-factor authentication, and enforcing role-based access controls ensure that only authorized individuals can access sensitive data.
Encryption
Encrypting data protects it from unauthorized access, rendering it unreadable even if unauthorized individuals obtain it.
Monitoring and Detection
Implementing monitoring systems and intrusion detection tools helps organizations detect and respond to security incidents promptly, minimizing the potential impact of a data breach.
Data Masking: Safeguarding Sensitive Information
Data masking is a technique used to protect sensitive information by replacing it with fictitious but realistic data. Organizations can use and share data for different purposes, like testing and development, without revealing sensitive information.
This helps protect the confidentiality of sensitive data. It also allows for collaboration and innovation within the organization. Sharing data in this way can improve efficiency and productivity. Common data masking techniques include:
- Substitution: Replacing sensitive data with randomly generated values that maintain the same format and data type.
- Shuffling: Rearranging the values within a dataset to break the connection between the sensitive data and its original context.
- Encryption: Encrypting sensitive data and providing access to authorized parties through secure key management.
Sensitive Data Solutions: Continuous Data Protection
Continuous Data Protection (CDP) constantly backs up and protects critical data in real-time. Unlike traditional backup solutions, which capture data at set intervals, CDP systems continuously monitor and record data changes. This enables near-instantaneous recovery in case of data loss or security incidents.
CDP solutions offer several benefits, including:
Minimize Data Loss
CDP systems constantly save data changes to reduce the risk of losing important information between backups. This helps organizations recover from incidents with as little data loss as possible.
Faster Recovery
CDP solutions assist organizations in quickly recovering individual files or data points, rather than entire systems. This helps to decrease downtime and minimize the impact of data loss.
Improved Compliance
With CDP, companies can show they can keep important data safe and get it back if needed. This helps them follow rules and keep customers’ trust.
Your Comprehensive Solution for Continuous Data Protection
In the ever-evolving landscape of data protection, organizations need a reliable and comprehensive solution to safeguard their sensitive information. DataSunrise provides a set of strong tools to protect your data and keep it safe and compliant.
With DataSunrise, you can leverage advanced features such as data auditing, robust security measures, flexible masking rules, and vulnerability assessment scanning. Our data auditing capabilities allow you to gain deep insights into your data landscape, identifying potential risks and vulnerabilities. By implementing strong security controls, including access management and encryption, DataSunrise helps you protect your sensitive data from unauthorized access and breaches.
Come to our demo session to see how DataSunrise can protect your data and enhance your security strategy. You’ll see firsthand how our tools work to keep your sensitive information safe.
