
Data Audit for IBM DB2

Data Security and Compliance: A Critical Necessity in Today’s World
In today’s digital landscape, data protection is not just a best practice—it’s essential for success. Organizations across healthcare, finance, and tech sectors face mounting pressure to secure sensitive information while navigating complex regulatory frameworks like GDPR, HIPAA, and PCI DSS.
Did you know that in 2021, Capital One agreed to pay $190 million to settle a class action lawsuit related to their 2019 data breach? The data breach in question at the time affected more than 100 million customers. A properly configured database audit system could have detected the suspicious activity earlier.
IBM DB2’s native audit facility, db2audit, offers organizations the foundational tools needed for data audit for IBM DB2. While db2audit provides essential auditing capabilities out of the box, understanding its proper configuration and limitations is crucial for maintaining robust security postures.
Step-by-Step Guide to Enable Basic Data Audit for IBM DB2
- Start the db2audit Tool:
Open a terminal and run the following command to start the audit tool:
db2audit start - Set the Audit Scope to Log All Queries:
Enable the recording of
db2auditactivities by setting the scope toboth, which will capture bothdb2auditstatus events and auditing activities. Usedatapathandarchivepathto specify the active and archive log locations:db2audit configure scope audit status both db2audit configure datapath C:\Users\user\Desktop\db2audit db2audit configure archivepath C:\Users\user\Desktop\db2audit\archive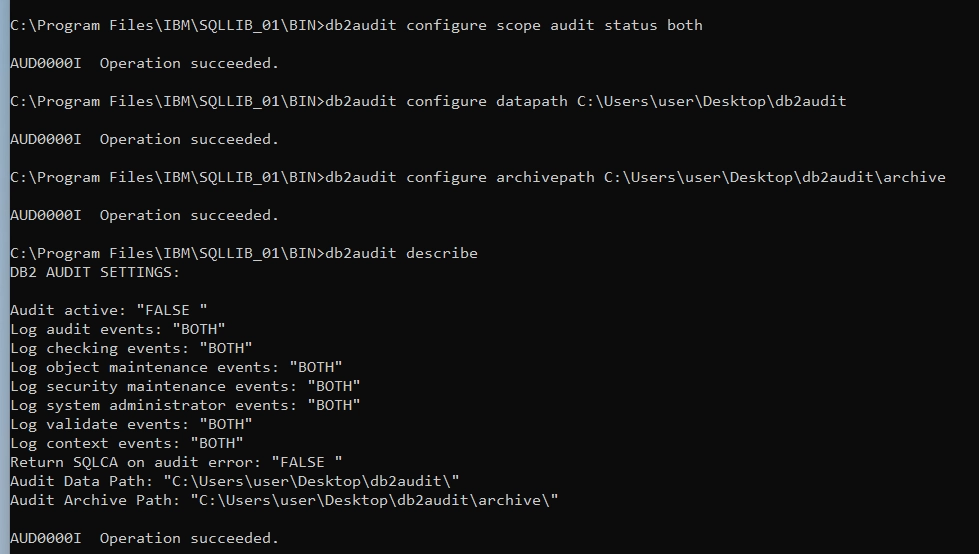
Configuration of db2audit (The Built-In DB2 Audit Facility) - Extract Audit Logs:
First, flush and archive the audit logs, then extract them:
db2audit flush db2audit archiveIn the extract command below, replace
<outputfile>with a name for the extracted log file (e.g.,audit.out) and<logfile>with the file name displayed in thedb2audit archivecommand output. Note that the specified output file will be created in the current directory, so before executing the command you could navigate to the specific desired folder.db2audit extract file <outputfile> from files <logfile>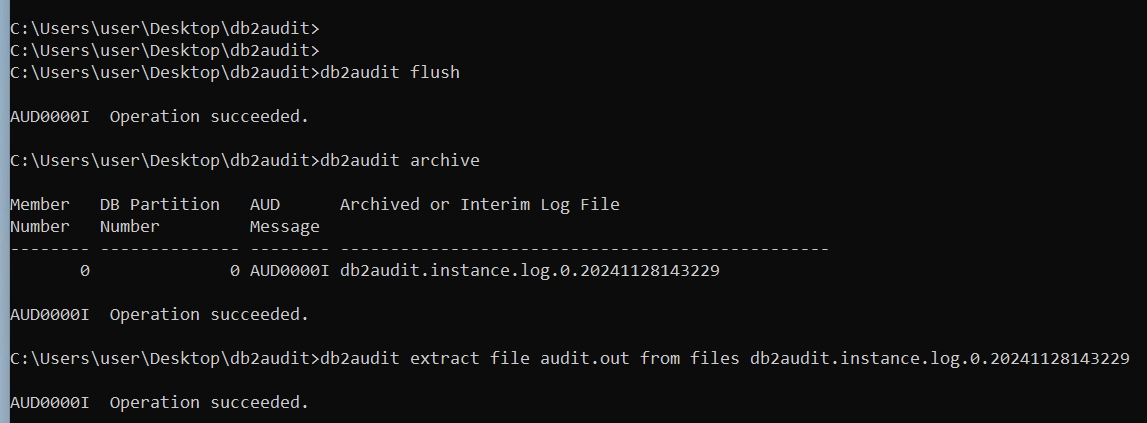
Extracting Audit Logs in db2audit (The Built-In DB2 Audit Facility) - Check the Logs:
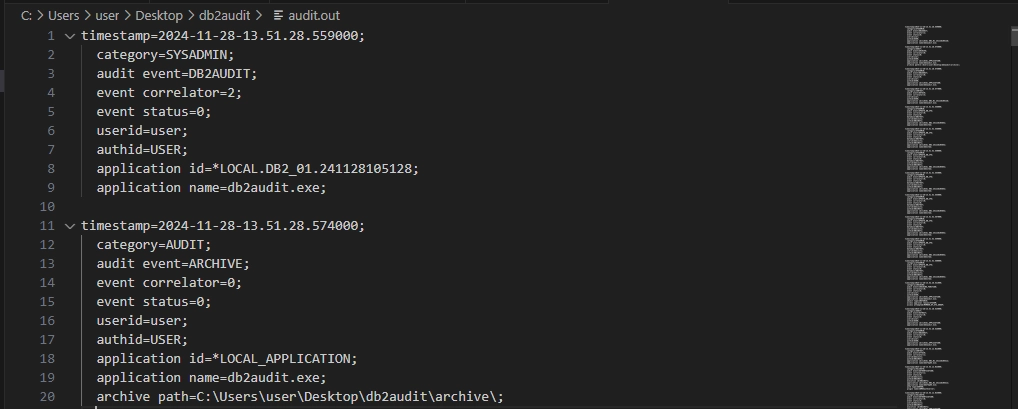
The audit log file (e.g.,
audit.out) should now contain information about executed commands, connections, and more. You can open this file with a text editor to verify thatdb2auditis logging events as expected.
This basic db2audit configuration will now allow you to log the following activities:
- Authentication attempts
- Instance startup/shutdown
- Authorization failures
- Object creation/deletion
- Security changes
Data Audit for IBM DB2 Using Built-In Tools: Challenges and Limitations
While this setup provides valuable basic logging, it does not capture regular SQL queries by default. To log SQL activity, you will need to take additional steps. You can either:
Configure Audit Policies: Set up specific audit policies to log statement/query activity, which will then appear in the
db2auditlogs. However, this requires careful configuration and ongoing maintenance to ensure it meets your needs.Implement Custom Audit Tables: Create custom audit tables and triggers to capture SQL queries in more detail. This approach offers greater flexibility but involves significant development effort and ongoing management to ensure performance is not impacted.
Both options require time, expertise, and resources to implement and maintain effectively.
Advantages of Specialized Database Auditing Tools
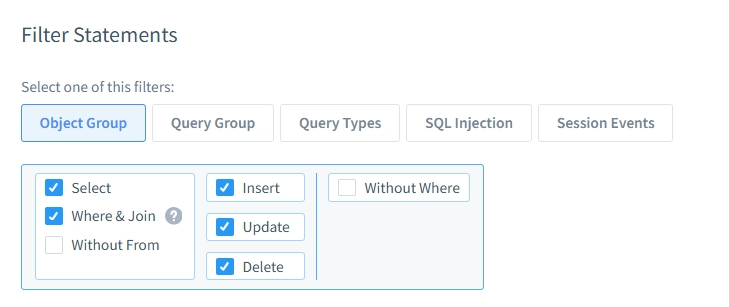
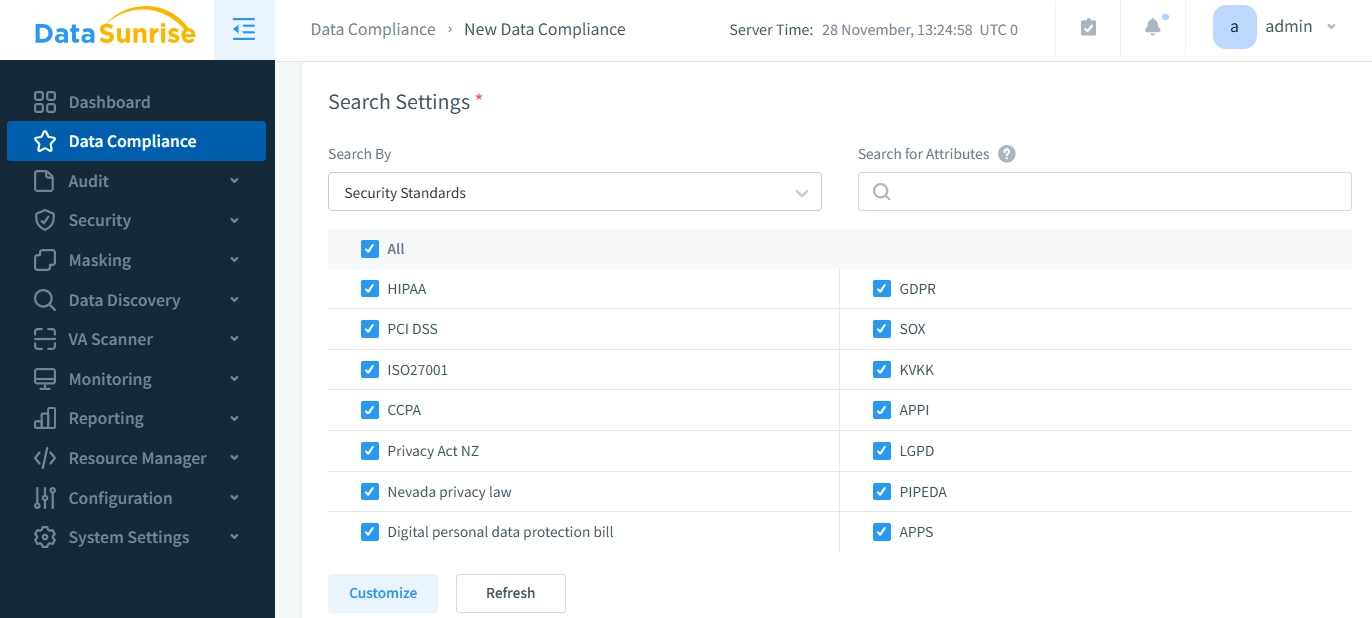
Ensuring compliance with regulations like HIPAA, GDPR, and others can be complex and time-consuming. Organizations often find that native database tools, while useful, are not enough to meet the full range of auditing and compliance needs. This is where solutions like DataSunrise stand out, offering powerful tools that simplify the auditing process with various filter statement options, while greatly reducing the time and effort required for setup, configuration, and ongoing maintenance.
Why Third-Party Solutions could be More Efficient
While native database auditing tools, such as IBM DB2’s built-in features, offer basic functionality, they typically require extensive customization and ongoing management to cover all compliance and security needs. Third-party tools like DataSunrise make this process much more efficient, offering:
- Quick Setup and Ease of Configuration: DataSunrise is designed to be quick and simple to deploy, with minimal required setup compared to native solutions that often require in-depth configuration and fine-tuning.
- Less Maintenance: With third-party tools, you can reduce the administrative burden by automating key tasks such as compliance reporting and alerting, which would otherwise require manual intervention using native auditing tools.
- Feature-Rich Solutions: Unlike basic native auditing, DataSunrise offers a wide array of auditing and security features, including real-time activity monitoring, automated compliance reporting, and advanced threat detection.
DataSunrise: The Security and Compliance Coverage You Need
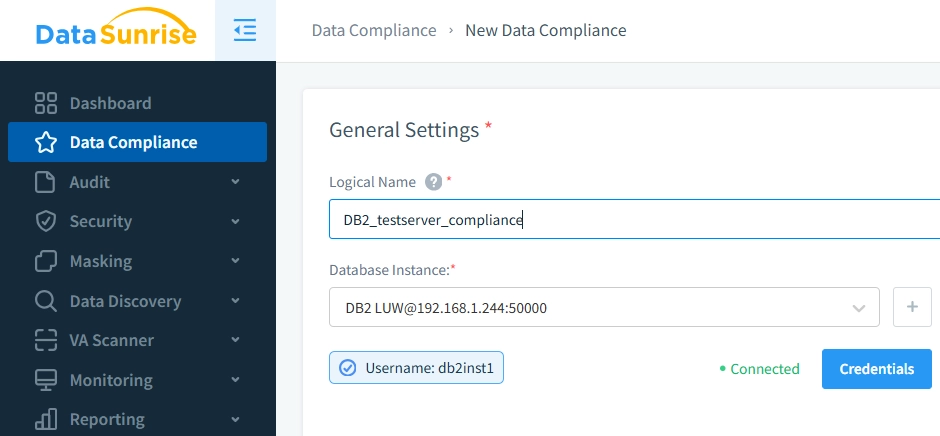
DataSunrise excels at covering a vast array of auditing and compliance needs, enabling organizations to meet industry regulations without the heavy lifting. Key benefits include:
- Real-Time Monitoring and Alerts: DataSunrise tracks database activities in real-time, giving immediate visibility into security events and enabling swift responses to potential threats.
- Automated Compliance Reporting: Pre-configured compliance templates and automated reporting capabilities make it easy to generate the necessary documentation for audits and regulatory reviews.
- Advanced Threat Detection: Using machine learning and behavioral analytics, DataSunrise detects anomalies and potential threats, ensuring proactive security measures.
- Customizable Audit Rules: You can define specific auditing rules based on your unique security needs, giving you more control over what gets monitored and how alerts are triggered.
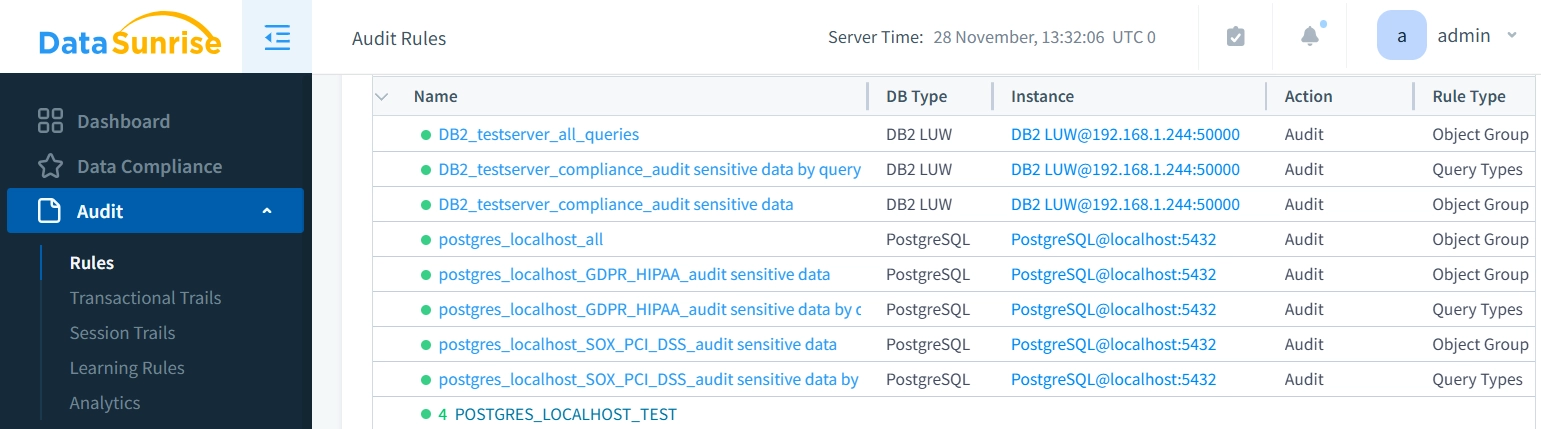
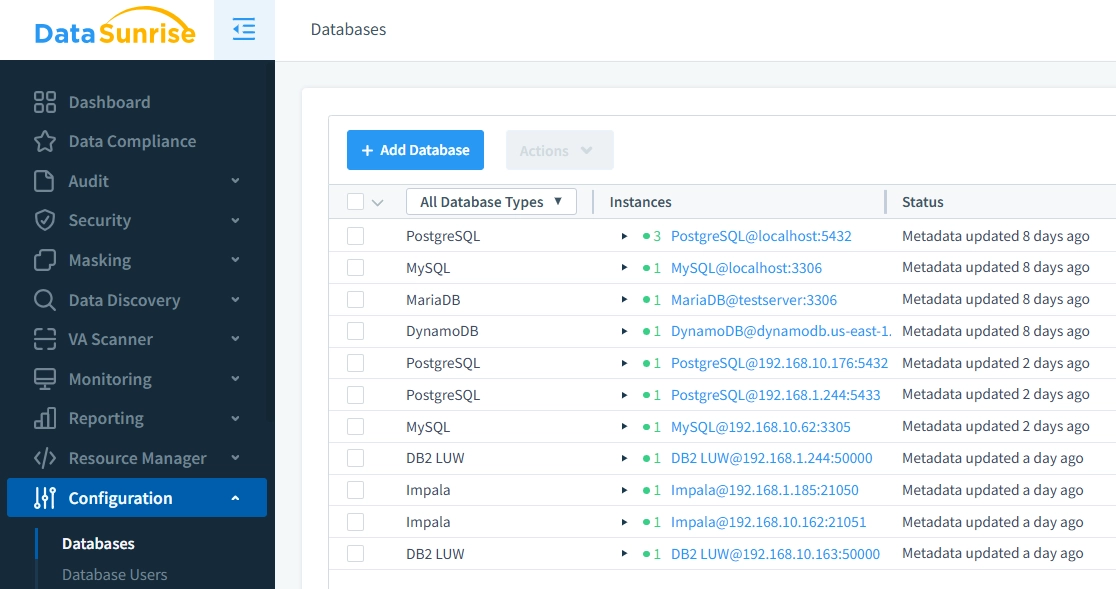
- Covering More Than Just DB2: One of the standout features of DataSunrise is its versatility. It supports not only IBM DB2 but also over 40 other database engines, including PostgreSQL, MySQL, SQL Server, Oracle and others. This makes it an ideal solution for organizations that operate a mixed database environment, providing consistent and comprehensive auditing across multiple platforms without the need to rely on separate tools for each system.
Conclusion: Effortless, Comprehensive Auditing with DataSunrise
Using DataSunrise for database auditing and compliance offers numerous advantages when it comes to data audit for IBM DB2: faster setup, less ongoing maintenance, and a much more comprehensive feature set than native tools. With DataSunrise, organizations can manage their auditing and compliance needs efficiently while ensuring that critical database security and regulatory requirements are met with minimal effort.
By supporting a wide range of databases and offering a robust suite of security and auditing features, DataSunrise provides an all-in-one solution that can scale with your organization’s needs, making it the smart choice for database security and compliance.
Our platform provides versatile deployment options, robust audit capabilities, and enhanced security features. Schedule an online demo now to experience the advantages of data audit for IBM DB2 with a feature-rich, easy-to-implement database auditing solution and see how it could benefit your organization.
