
Enhancing Data Security with Data Masking in Amazon Aurora

Introduction
On Friday, July 19, 2024, a CrowdStrike security system update caused significant disruption in the cybersecurity community. Notably, numerous airports affected by this incident were forced to revert to manual check-in operations. This event underscores the critical nature of infrastructure security and the potential consequences of cyberattacks or system failures. It highlights a crucial point: data processing must continue, regardless of circumstances. In this article, we explore data masking for Amazon Aurora, a key strategy in maintaining data security and operational continuity.
For Amazon Aurora users, implementing robust data masking techniques is essential to safeguard sensitive data and maintain regulatory compliance.
This article will explore the basics of data masking for Amazon Aurora, including AWS Aurora’s native capabilities and third-party solutions like DataSunrise. We’ll dive into the concept of dynamic masking and provide practical steps to create a DataSunrise instance for enhanced data protection.
Understanding Data Masking in Amazon Aurora
What is Data Masking?
Data masking is a security technique that replaces sensitive data with realistic but fake information. This process ensures that confidential details remain protected while maintaining the data’s usability for testing, development, or analytics purposes.
Amazon Aurora’s Native Data Masking Capabilities
Amazon Aurora, a powerful relational database service, offers built-in data masking features. These tools help users protect sensitive information effectively. Here’s a brief overview of Aurora’s data masking capabilities:
- Column-level encryption: Aurora allows you to encrypt specific columns containing sensitive data.
- Dynamic data masking: Aurora supports real-time masking of data based on user roles and permissions.
Native Masking Example
To create dynamic masking in Aurora PostgreSQL with custom functions let’s create a sample table, user, grant permissions and the custom function:
CREATE DATABASE mytestdb;
CREATE USER user1 WITH PASSWORD 'pass';
GRANT ALL PRIVILEGES ON DATABASE mytestdb TO user1;
CREATE TABLE MOCK_DATA (
id INT,
first_name VARCHAR(50),
last_name VARCHAR(50),
email VARCHAR(50),
phone VARCHAR(50),
ip_address VARCHAR(20)
);
GRANT ALL PRIVILEGES ON TABLE MOCK_DATA TO user1;
INSERT INTO MOCK_DATA (id, first_name, last_name, email, phone, ip_address)
VALUES
(1, 'Roana', 'Houseley', 'rhouseley0@ustream.tv', '600-318-8403', '134.236.96.231'),
(2, 'Joni', 'Renbold', 'jrenbold1@ovh.net', '217-158-4073', '232.255.48.239'),
(3, 'Anna-diane', 'Blackader', 'ablackader2@blogspot.com', '778-730-4651', '108.25.102.249'),
(4, 'Leonore', 'Sharpling', 'lsharpling3@mit.edu', '634-506-0483', '10.202.61.242'),
(5, 'Bobbee', 'Steven', 'bsteven4@upenn.edu', '336-531-1034', '161.168.66.101'),
(6, 'Siegfried', 'Alexandrou', 'salexandrou5@scientificamerican.com', '636-273-5011', '83.198.21.252'),
(7, 'Reena', 'Penas', 'rpenas6@ted.com', '928-513-0275', '194.25.234.254'),
(8, 'Genevieve', 'Heisman', 'gheisman7@ustream.tv', '862-883-4168', '186.159.54.135'),
(9, 'Leshia', 'Mitchall', 'lmitchall8@smh.com.au', '475-791-3864', '58.237.134.245'),
(10, 'Shandy', 'Haxley', 'shaxley9@amazonaws.com', '741-167-8958', '205.143.56.68');
-- Create a function to mask data
CREATE OR REPLACE FUNCTION mask_phone_number(phone_number text)
RETURNS text AS $$
BEGIN
RETURN CONCAT('XXX-XXX-', RIGHT(phone_number, 4));
END;
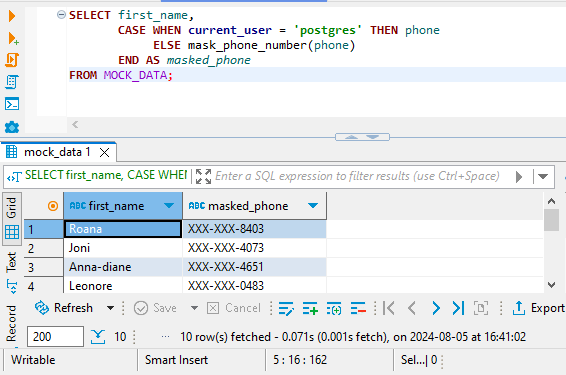
$$ LANGUAGE plpgsql;When connecting to the database as either the postgres superuser or the user1 account, you’ll notice a significant difference in how the data appears. This difference stems from the applied masking rules. For instance, when accessing Aurora PostgreSQL through a client like DBeaver, the postgres user will see the unmasked phone numbers in their original format. Here’s an example of how an unmasked phone number appears:
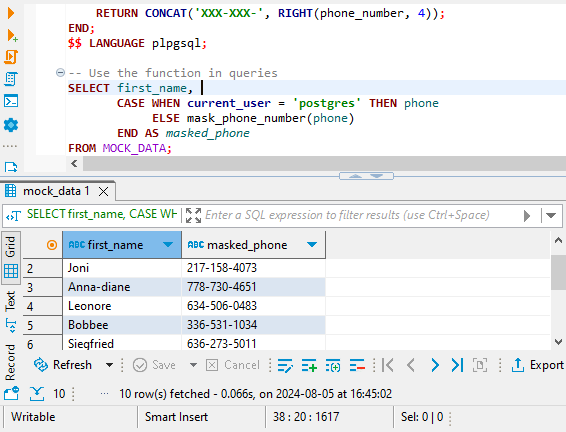
And masked data for unprivileged user1 user looks as follows:
Enhancing Data Protection with DataSunrise
While Aurora’s native capabilities are useful, third-party solutions like DataSunrise offer more advanced features for comprehensive data masking.
What is DataSunrise?
DataSunrise is a powerful database security platform that provides advanced data protection features, including dynamic data masking, for various database systems, including Amazon Aurora.
Creating a DataSunrise Instance for Dynamic Masking
To implement dynamic masking using DataSunrise, follow these steps:
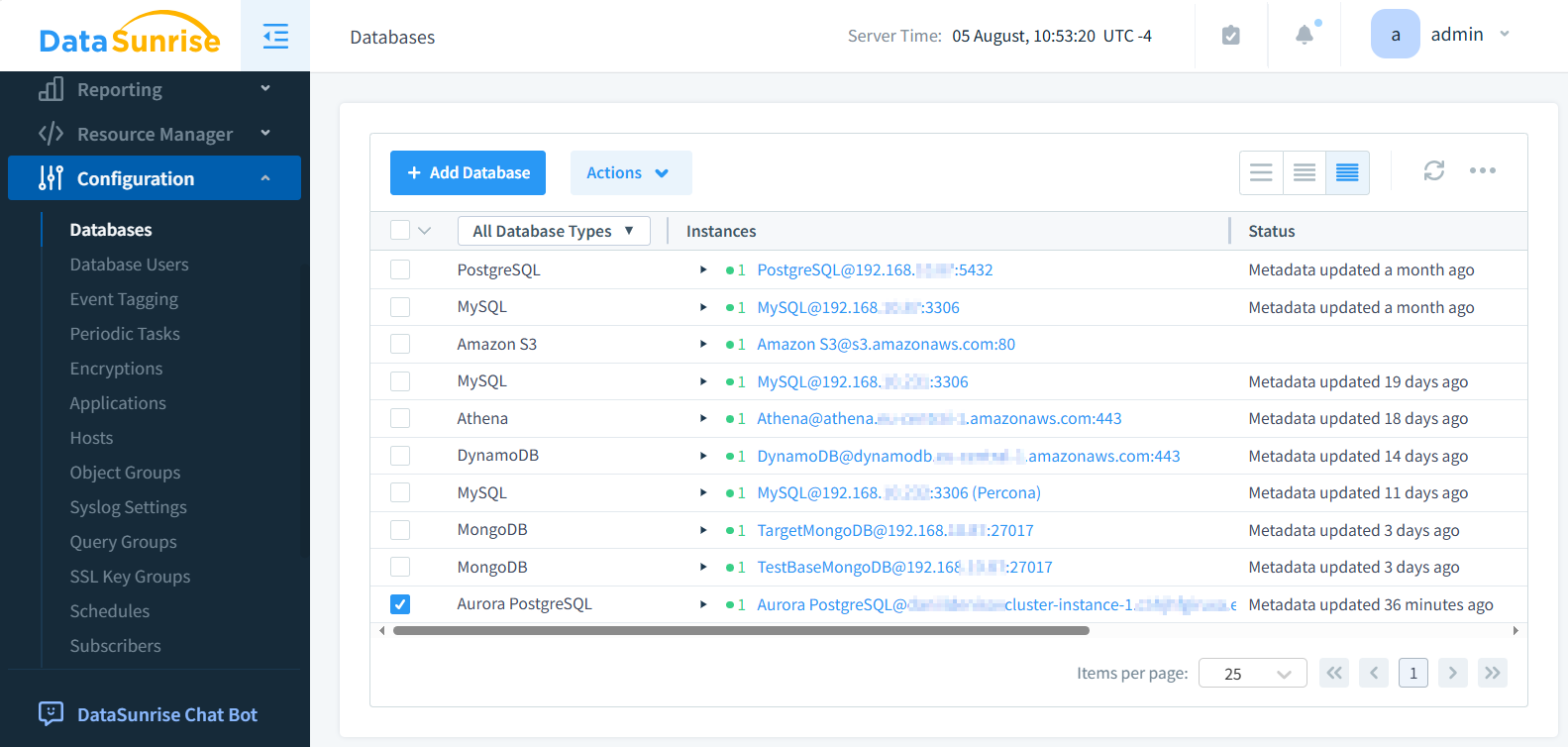
- Connect to Aurora: Set up a connection between DataSunrise and your Aurora database.
The following image illustrates the Aurora PostgreSQL database instance in DataSunrise.
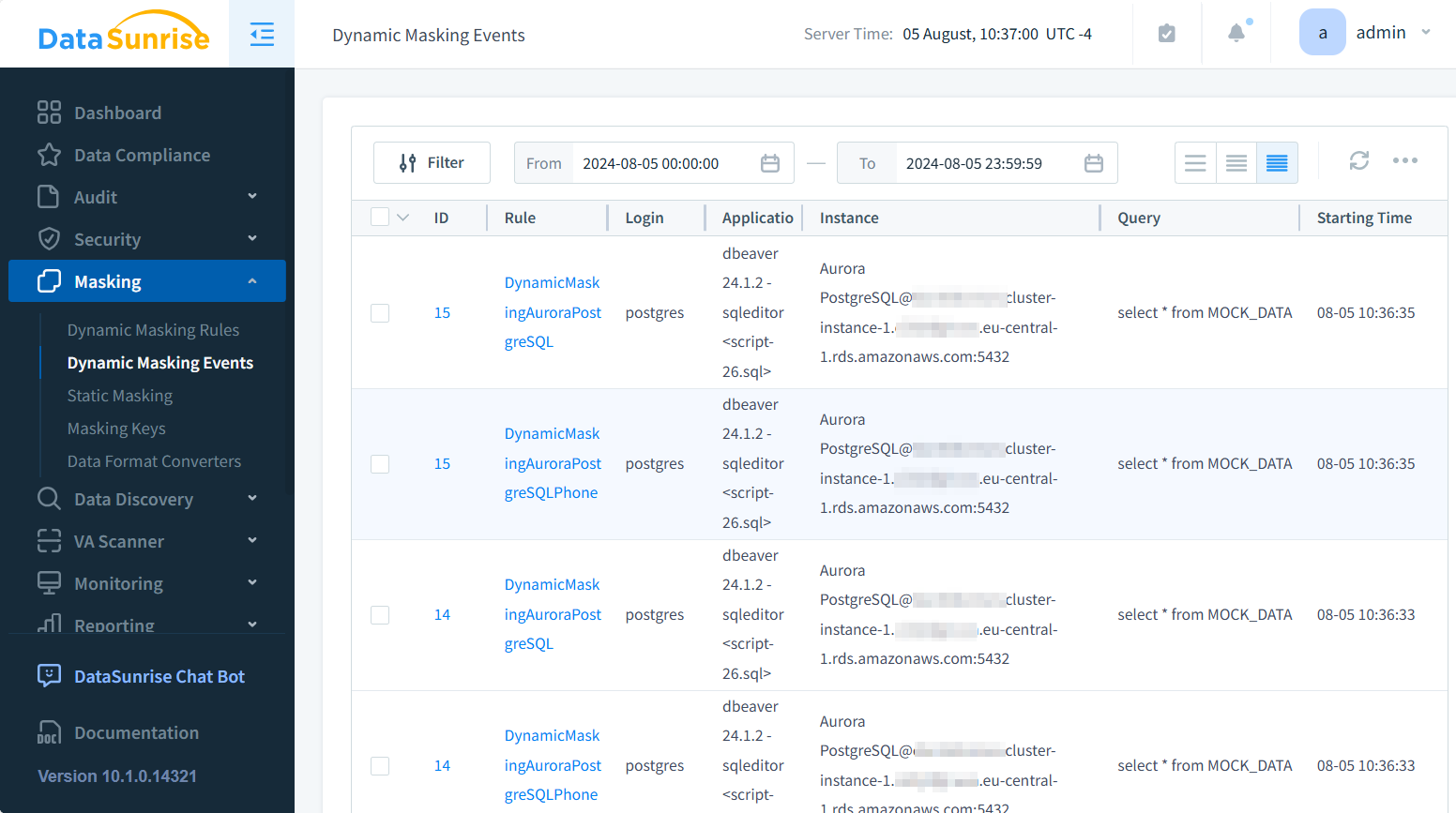
- Define masking rules: Create rules specifying which data should be masked and how.
- Apply masking: Activate the masking rules for your target database.
- Verify results: Query the database to confirm that sensitive data is properly masked.
Understanding Dynamic Masking
Dynamic masking is a real-time data protection technique that masks sensitive information on-the-fly as it’s being queried. Unlike static masking, which permanently alters the data, dynamic masking preserves the original data while presenting masked results to unauthorized users.
Benefits of dynamic masking include:
- Flexibility in applying different masking rules based on user roles
- No need to create separate copies of the database for different access levels
- Ability to quickly modify masking rules without altering the underlying data
Best Practices for Data Masking in Amazon Aurora
To ensure effective data masking for Amazon Aurora, consider these best practices:
- Identify sensitive data: Regularly audit your database to identify and classify sensitive information.
- Use appropriate masking techniques: Choose masking methods that suit your data types and security requirements.
- Implement role-based access control: Combine data masking with robust access controls for enhanced security.
- Regularly test and update: Periodically review and update your masking rules to address new security threats.
- Maintain data consistency: Ensure that masked data remains consistent across related tables and databases.
Regulatory Compliance and Data Masking
Data masking plays a crucial role in meeting various regulatory requirements. Some key regulations that emphasize data protection include:
- General Data Protection Regulation (GDPR)
- Health Insurance Portability and Accountability Act (HIPAA)
- Payment Card Industry Data Security Standard (PCI DSS)
By implementing robust data masking techniques in Amazon Aurora, organizations can significantly reduce the risk of non-compliance and potential penalties.
Conclusion
Data masking for Amazon Aurora is an essential practice for protecting sensitive information and ensuring regulatory compliance. While Aurora offers native masking capabilities, advanced solutions like DataSunrise provide more comprehensive protection through dynamic masking and other security features.
By implementing effective data masking strategies, organizations can safeguard their sensitive data, maintain compliance, and mitigate the risks associated with data breaches.
DataSunrise offers user-friendly and cutting-edge tools for database security, including audit and data discovery features. To experience the power of DataSunrise firsthand, visit our website for an online demo and discover how we can enhance your Amazon Aurora data protection strategy.
