
Data Masking for Amazon DynamoDB

Introduction
Protecting sensitive information is more critical than ever. With the rise of cloud computing, businesses are increasingly turning to services like Amazon DynamoDB to store and manage their data. However, this shift also brings new challenges in data security. Enter data masking for Amazon DynamoDB – a powerful technique that helps organizations safeguard their sensitive data while maintaining its usability for testing and development purposes.
Over 80% of U.S. adults believe they have minimal control over their personal data shared with government agencies or private companies. This alarming statistic underscores the importance of implementing robust data protection measures, such as data masking, in your database management strategy.
Understanding Amazon DynamoDB and Data Masking
What is Amazon DynamoDB?
Amazon DynamoDB is a fully managed NoSQL database service provided by AWS. It offers seamless scalability, high performance, and automatic data replication across multiple availability zones. Many organizations use DynamoDB to store and retrieve large amounts of structured data quickly and efficiently.
A key distinction between DynamoDB and relational databases like PostgreSQL is DynamoDB’s inability to verify attribute presence in items. This means only partition and sort keys are guaranteed to exist. Exercise caution when masking data, including with third-party tools, as other attributes may be absent.
The Importance of Data Masking
Data masking is a technique used to create a structurally similar but inauthentic version of an organization’s data. This process helps protect sensitive information by replacing it with realistic but fake data. For DynamoDB users, data masking is crucial for:
- Compliance with data protection regulations
- Securing sensitive data during development and testing
- Preventing unauthorized access to confidential information
Accessing and Masking Data in Amazon DynamoDB
Amazon DynamoDB offers multiple methods for data access and manipulation. Understanding these options is crucial for implementing effective data masking strategies. Let’s explore the available access methods and their implications for data masking:
Primary Access Methods for DynamoDB
- API (Application Programming Interface)
- CLI (Command Line Interface)
- Web-based User Interface
Additionally, DynamoDB supports PartiQL, a SQL-compatible query language. This feature allows users to make SQL-like calls within the three primary access methods mentioned above.
Limitations for Data Masking in DynamoDB
While DynamoDB is powerful and flexible, it has some limitations when it comes to data masking:
- No user-defined functions
- Lack of view support
- Limited query language capabilities for complex transformations
These constraints shape our approach to data masking in DynamoDB.
Our Data Masking Approach
Given these limitations, we’ll focus on two main strategies for data masking in DynamoDB:
- Dynamic Masking: We’ll implement masking after querying the data. This approach allows for real-time protection of sensitive information.
- Static Masking: For this method, we’ll create a separate table and populate it with masked data. This technique is particularly useful for creating safe, non-production environments.
In this article, we’ll primarily focus on dynamic masking techniques. For a detailed exploration of dynamic and static masking in DynamoDB, please refer to our companion articles on the topic.
By understanding these access methods and masking strategies, you can better protect sensitive data in your DynamoDB tables while maintaining functionality for testing and development purposes.
Limitations of PartiQL for Data Masking
PartiQL, the SQL-compatible query language for DynamoDB, lacks the flexibility required for dynamic or static masking. Its limitations include:
- Inability to modify data on-the-fly
- Limited support for complex transformations
- Lack of built-in masking functions
Implementing Data Masking for DynamoDB
import boto3
from boto3.dynamodb.conditions import Key
import re
# Initialize DynamoDB client
dynamodb = boto3.resource('dynamodb')
table = dynamodb.Table('danielArticleTable')
# Function to mask email
def mask_email(email):
return re.sub(r'(^[^@]{3}|(?<=@)[^.]+)', lambda m: '*' * len(m.group()), email)
# Function to mask IP address
def mask_ip(ip):
return re.sub(r'\d+', 'xxx', ip)
# Scan the table
response = table.scan()
# Process and mask the data
masked_items = []
for item in response['Items']:
masked_item = {
'id': item['id'],
'first_name': item['first_name'],
'last_name': item['last_name'],
'email': mask_email(item['email']),
'gender': item['gender'],
'ip_address': mask_ip(item['ip_address'])
}
masked_items.append(masked_item)
# Print masked items (or you could write to a new table)
for item in masked_items:
print(item)
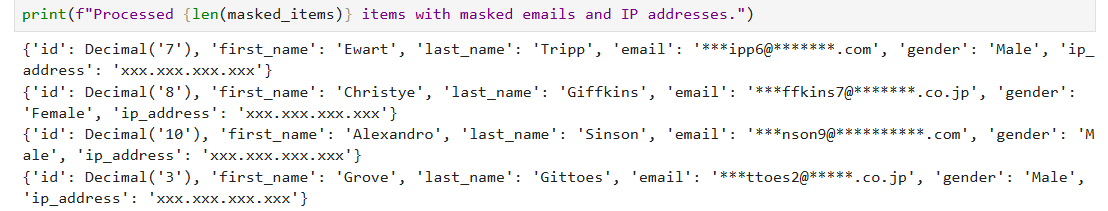
print(f"Processed {len(masked_items)} items with masked emails and IP addresses.")The output of this code is as follows:
Dynamic Data Masking with DataSunrise
Setting Up DataSunrise for DynamoDB
DataSunrise is a powerful tool that offers dynamic data masking capabilities for various databases, including Amazon DynamoDB. To see dynamically masked data using DataSunrise:
- Connect DataSunrise to your DynamoDB (create Instance)
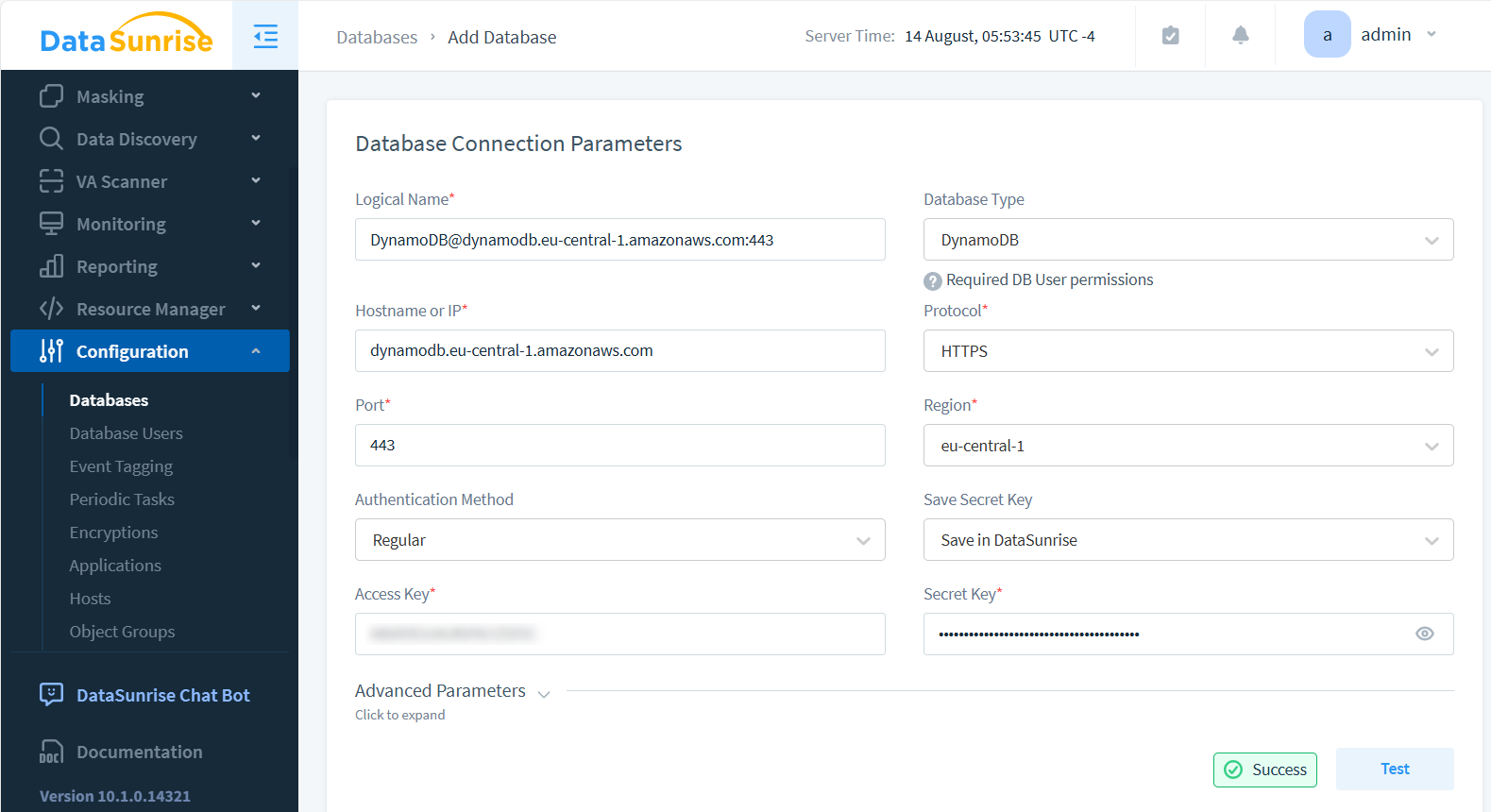
- Define masking rules for sensitive data fields
- Access your data through DataSunrise proxy (see below for CLI example)
Masking Methods in DataSunrise
DataSunrise provides numerous masking techniques to safeguard sensitive information. We’ve highlighted just a few examples below:
- Format-preserved encryption: Maintains the original data format while encrypting the content
- Fixed string value: Replaces sensitive data with a predefined string
- Null value: Replaces sensitive data with a null value
Here’s an example of how DataSunrise might mask data:
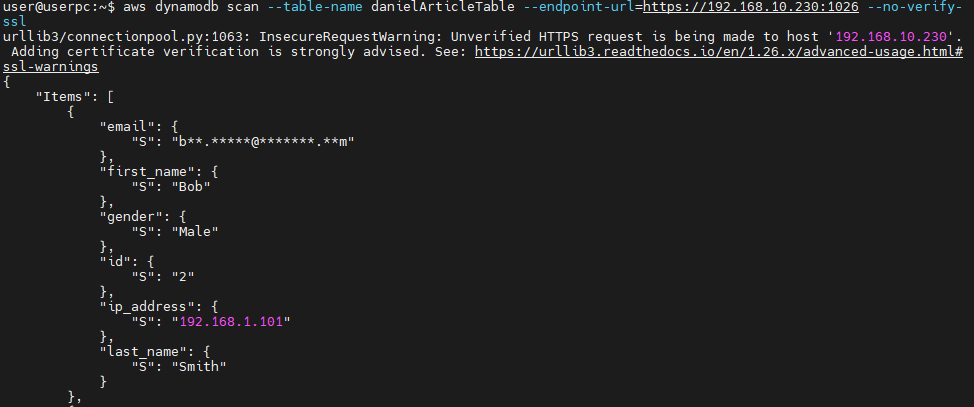
The AWS CLI outputs this when users access the DataSunrise Proxy (at 192.168.10.230:1026), which masks emails in the table. Disabling SSL verification (–no-verify) can be a security risk. Only do this in controlled environments where you trust the network and the proxy.
Benefits of Data Masking for DynamoDB
Implementing data masking for your DynamoDB tables offers several advantages:
- Enhanced data security: Protect sensitive information from unauthorized access
- Compliance: Meet regulatory requirements for data protection
- Improved testing: Use realistic but safe data for development and testing
- Risk mitigation: Reduce the impact of potential data breaches
Best Practices for Data Masking in DynamoDB
To maximize the effectiveness of your data masking strategy:
- Identify sensitive data fields that require masking
- Choose appropriate masking techniques for each data type
- Maintain referential integrity across related tables
- Regularly audit and update your masking rules
- Use a combination of static and dynamic masking as needed
Conclusion
Data masking for Amazon DynamoDB is a crucial practice for organizations looking to protect their sensitive data while leveraging the power of cloud databases. By implementing robust masking techniques, either through custom scripts or specialized tools like DataSunrise, you can significantly enhance your data security posture and comply with data protection regulations.
As data breaches continue to pose a significant threat to businesses worldwide, investing in comprehensive data masking solutions is no longer optional – it’s a necessity for responsible data management in the digital age.
DataSunrise offers user-friendly and cutting-edge tools for database security, including audit and vulnerabilities assessment among other features. Its dynamic and static data masking capabilities for Amazon DynamoDB provide an extra layer of protection for your sensitive data. To experience the power of DataSunrise firsthand, we invite you to visit our website for an online demo and discover how we can help secure your database environment.
