
Comprehensive Guide to Database Audit for Amazon Redshift: Security, Compliance, and Best Practices

Introduction
Amazon Redshift, a popular cloud data warehouse, handles vast amounts of sensitive information. Database breaches aren’t just about malware; they often involve human error or insider threats. A robust database audit for Amazon Redshift, like the one offered by DataSunrise, equips database administrators with the tools to detect, prevent, and respond to a wide range of potential data breaches.
By monitoring user behavior and database activity, DataSunrise’s solution helps safeguard your valuable data against both external attacks and internal risks. Let’s explore how database audit can protect your valuable data and ensure regulatory compliance.
Understanding Amazon Redshift’s Native Audit Capabilities
Amazon Redshift offers built-in audit logging features. These tools help track user behavior and monitor database activity. Let’s examine some key aspects:
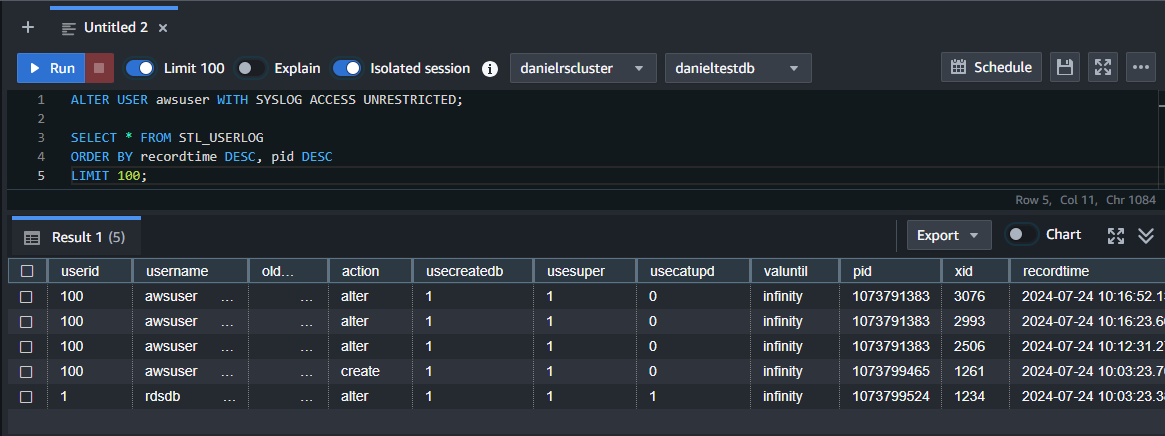
Enable Logging
Redshift can log all queries executed against your database. To enable this:
ALTER USER username WITH SYSLOG ACCESS UNRESTRICTED;
This command grants unrestricted access to system logs for a specific user (‘awsuser’ in the picture below).
Connection Logging
Redshift also logs connection attempts. To view these logs:
SELECT * FROM stl_connection_log;
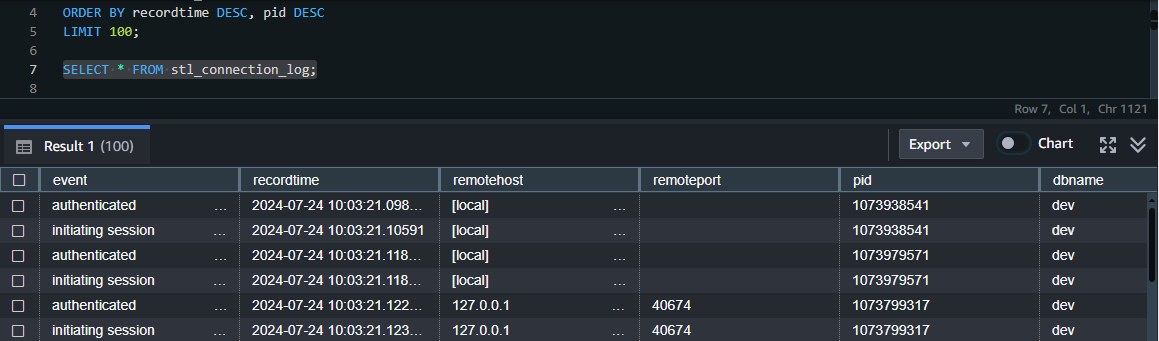
This query retrieves all connection log entries.
User Activity Tracking
To monitor user actions:
SELECT * FROM stl_userlog;
This command displays a log of user activities within the database.
While these native capabilities are useful, they have limitations. This brings us to third-party audit solutions.
Why Consider Third-Party Audit Solutions for Redshift?
Third-party audit tools offer several advantages over native Redshift logging:
- Enhanced granularity: They provide more detailed insights into database activity.
- Real-time alerts: Immediate notifications for suspicious activities.
- Customizable rules: Tailor auditing to your specific security needs.
- Compliance reporting: Easily generate reports for regulatory requirements.
- Historical data analysis: Retain and analyze audit logs for extended periods.
These features make third-party solutions attractive for organizations with stringent security requirements.
Introducing DataSunrise: A Comprehensive Audit Solution
DataSunrise offers a powerful audit tool for Amazon Redshift. Let’s explore how to set it up and create audit rules.
Creating a DataSunrise Instance
To begin with DataSunrise, create a Redshift database instance in the platform. Simply click the “Add Database” button and enter your credentials. This straightforward process quickly connects DataSunrise to your Redshift environment, enabling robust audit capabilities.
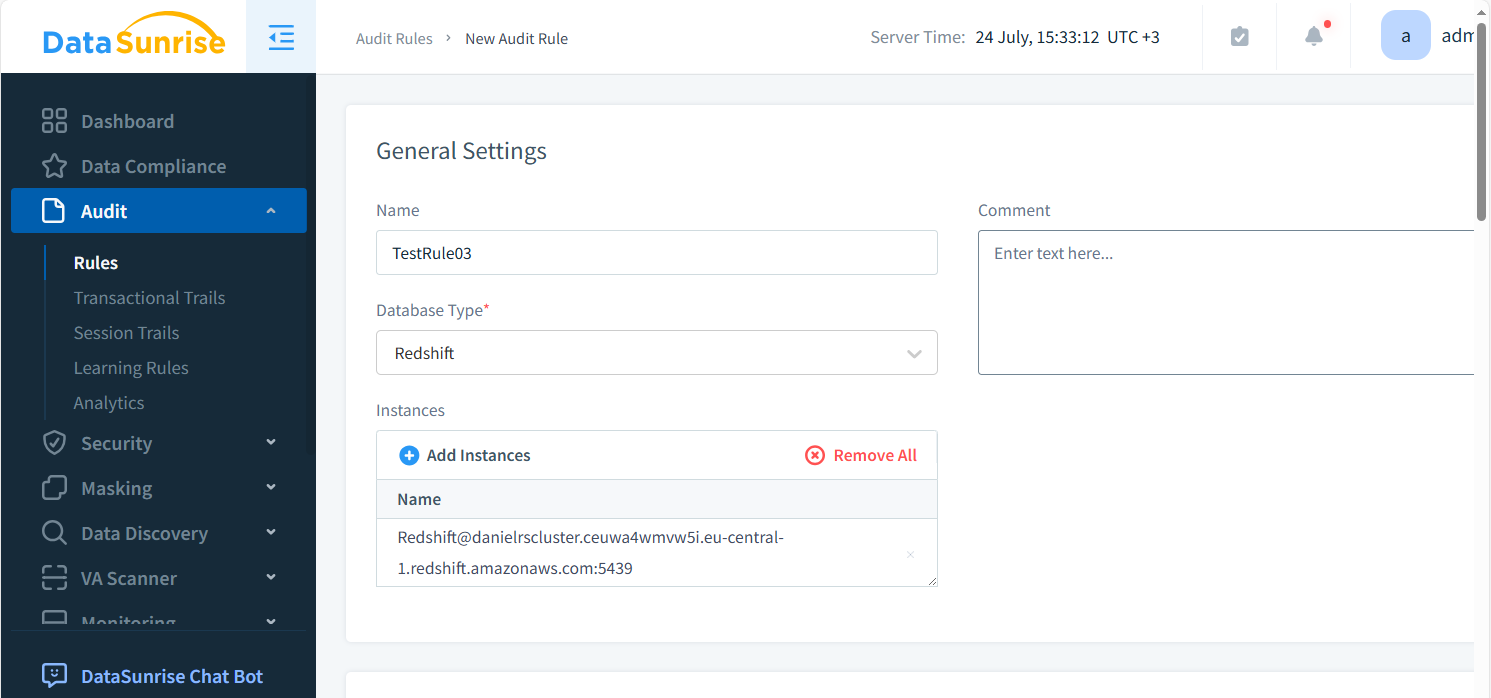
Creating an Audit Rule for Redshift
Follow these steps to create an audit rule:
- Navigate to the “Audit” section.
- Click “Add New Rule.”
- Specify the rule name and description.
- Define the audit scope (e.g., specific tables, users, or query types – see figure below).
- Set the audit action (e.g., log, alert, or block).
- Configure any additional parameters (e.g., time-based conditions).
- Save and activate the rule.
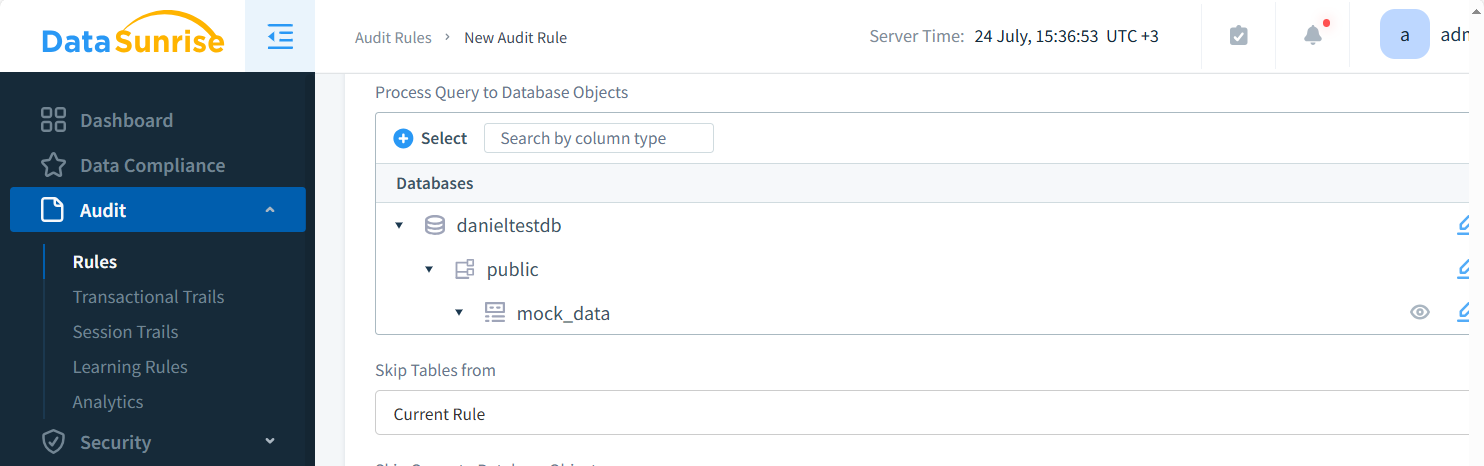
DataSunrise will now monitor your Redshift database according to the defined rule.
Key Benefits of Database Audit for Amazon Redshift
Implementing robust auditing for Redshift offers numerous advantages:
- Improved security posture
- Regulatory compliance adherence
- Insider threat detection
- Operational efficiency insights
- Forensic analysis capabilities
These benefits contribute to a more secure and efficient data environment.
Future Trends in Database Auditing
The landscape of database auditing and database activity monitoring is evolving. Some emerging trends include:
The landscape of database auditing and database activity monitoring is rapidly evolving. As cyber threats become more sophisticated, auditing tools must adapt. Let’s explore some emerging trends:
1. AI-powered Anomaly Detection
Artificial Intelligence (AI) is revolutionizing anomaly detection in database auditing:
- Machine Learning algorithms analyze patterns of user behavior over time.
- These systems can identify subtle deviations that might indicate a security threat.
- AI-driven tools can predict potential issues before they occur, enabling proactive security measures.
- Natural Language Processing (NLP) helps in analyzing query patterns to detect unusual or potentially malicious requests.
2. Integration with Broader Security Ecosystems
Database auditing is no longer an isolated process:
- Modern tools integrate with Security Information and Event Management (SIEM) systems.
- This integration provides a holistic view of an organization’s security landscape.
- Correlation of database audit data with network logs, application logs, and other security metrics offers deeper insights.
- Real-time data sharing between systems enables faster threat detection and response.
3. Automated Compliance Reporting
Compliance requirements are becoming more stringent and complex:
- Automated tools now generate compliance reports tailored to specific regulations (e.g., GDPR, HIPAA, PCI DSS).
- These reports can be scheduled and distributed automatically to relevant stakeholders.
- Dynamic dashboards offer real-time compliance status updates.
- AI-assisted tools can predict potential compliance issues and suggest remediation steps.
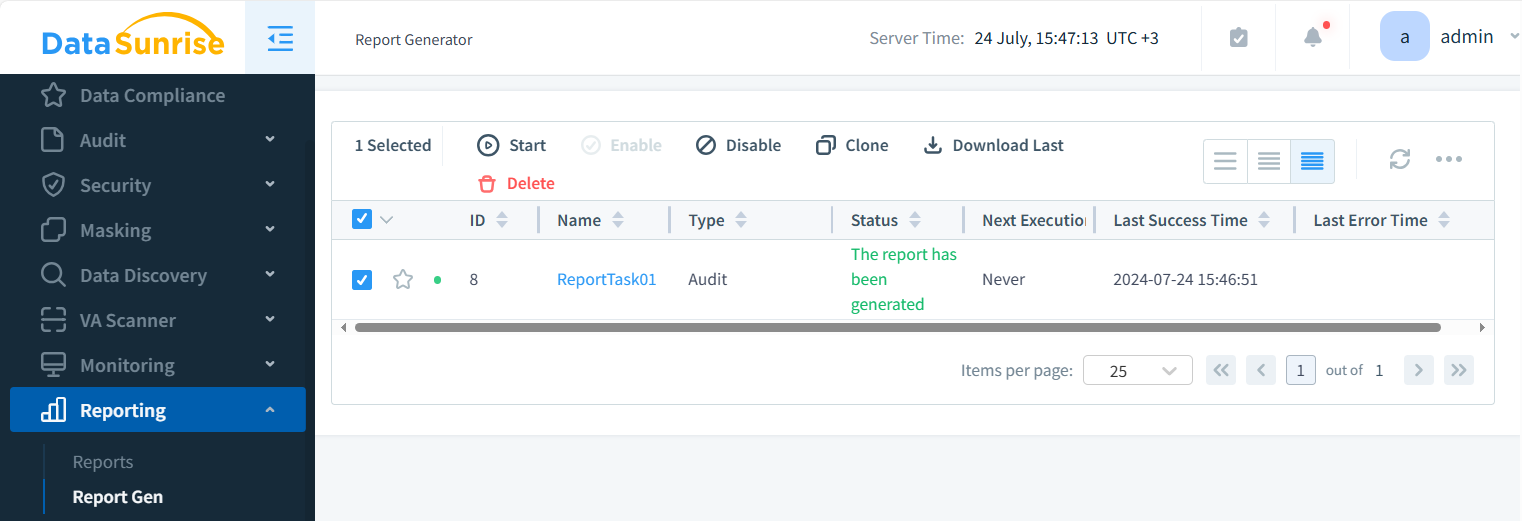
DataSunrise includes outstanding reporting capabilities for database audit and for implementing your own AI-assisted tools:
4. Cloud-based Auditing Solutions
As more databases move to the cloud, auditing solutions are adapting:
- Cloud-based tools offer seamless integration with cloud databases like Amazon Redshift.
- These solutions can scale dynamically based on database activity levels.
- They provide advanced features like cross-cloud auditing for multi-cloud environments.
- Cloud-based tools often offer better performance and cost-efficiency compared to traditional on-premises solutions.
5. Blockchain for Immutable Audit Trails
Emerging blockchain technologies offer new possibilities:
- Blockchain can create tamper-proof audit logs, ensuring the integrity of audit data.
- This technology is particularly useful for highly regulated industries requiring foolproof audit trails.
- Smart contracts can automate certain audit processes and enforce compliance rules.
Staying abreast of these trends is crucial for future-proofing your audit strategy. By embracing these innovations, organizations can enhance their security posture, streamline compliance processes, and gain deeper insights into their database activities. As the threat landscape continues to evolve, so too must our approach to database auditing and activity monitoring.
Conclusion
Database audit for Amazon Redshift is a critical component of a comprehensive security strategy. While Redshift offers native auditing capabilities, third-party solutions like DataSunrise provide enhanced features for robust monitoring and compliance. By implementing best practices and leveraging advanced tools, organizations can protect their valuable data assets and maintain regulatory compliance.
Remember, effective auditing is not just about ticking boxes. It’s about gaining deep insights into user behavior and database activity. This knowledge empowers you to make informed decisions and maintain a secure data environment.
DataSunrise offers user-friendly and flexible tools for database security, including audit, masking, and data generation among other features. Visit our website for an online demo and explore how we can enhance your database security posture. Alternatively, download our software’s trial version and explore its features. Our integrated AI assistant is ready to answer any questions you may have about DataSunrise’s capabilities and usage.
