
Comprehensive Guide to Database Audit in Elasticsearch for Security and Compliance

Enhancing Security and Compliance
Elasticsearch is a strong tool for searching and analyzing large amounts of data efficiently. As Elasticsearch grows in popularity, the need for robust database auditing becomes crucial. Database audit in Elasticsearch helps track user activities, monitor data access, and ensure compliance with security policies.
Elasticsearch database audit is the process of recording and analyzing activities within an Elasticsearch cluster. It involves tracking user actions, data editing, and system changes. This auditing process helps maintain data integrity, detect security breaches, and meet regulatory requirements.
The Importance of Elasticsearch Database Audit
Security is a primary concern for any organization using Elasticsearch. Database audit strengthens security by monitoring user activities. It helps identify unauthorized access attempts and potential security threats.
If someone tries to access important customer data, the audit log will record it. Administrators can then review the log and take appropriate action.
Many industries must comply with regulations like GDPR, HIPAA, or PCI DSS. Elasticsearch database audit helps organizations meet these compliance standards by providing detailed records of data access and changes. A healthcare provider using Elasticsearch to store patient records can use auditing to prove HIPAA compliance.
Audit logs can also help identify performance issues or unusual patterns in Elasticsearch usage. By analyzing these logs, administrators can optimize queries, improve resource allocation, and enhance overall system performance.
Key Features and Implementation
Elasticsearch offers several key features for database auditing. User activity tracking records logins, logouts, and login failures. This helps identify suspicious activities and potential security breaches. For instance, multiple failed login attempts from a single IP address might indicate a brute-force attack.
Document access monitoring allows administrators to track who accesses specific documents or indices. This capability is crucial for protecting sensitive data and ensuring proper access controls. A financial institution using Elasticsearch to store transaction data can monitor who views or modifies this information.
To implement database audit in Elasticsearch, you need to enable the feature in the elasticsearch.yml configuration file. Add the following lines to enable basic auditing:
xpack.security.audit.enabled: true
You can also configure which events to audit:
xpack.security.audit.logfile.events.include: ["authentication_success", "authentication_failure", "access_denied", "index_access_granted"]
Elasticsearch can output audit logs to files or to a separate index. To log to a file, add the following configuration:
xpack.security.audit.logfile.path: /path/to/audit/log/file.json
DataSunrise offers an easier way of implementing data audit. Its intuitive interface provides straightforward control over every aspect of database auditing.
Additionally, DataSunrise leverages cutting-edge AI tools for in-depth audit trail analyzing, enhancing security and compliance efforts.
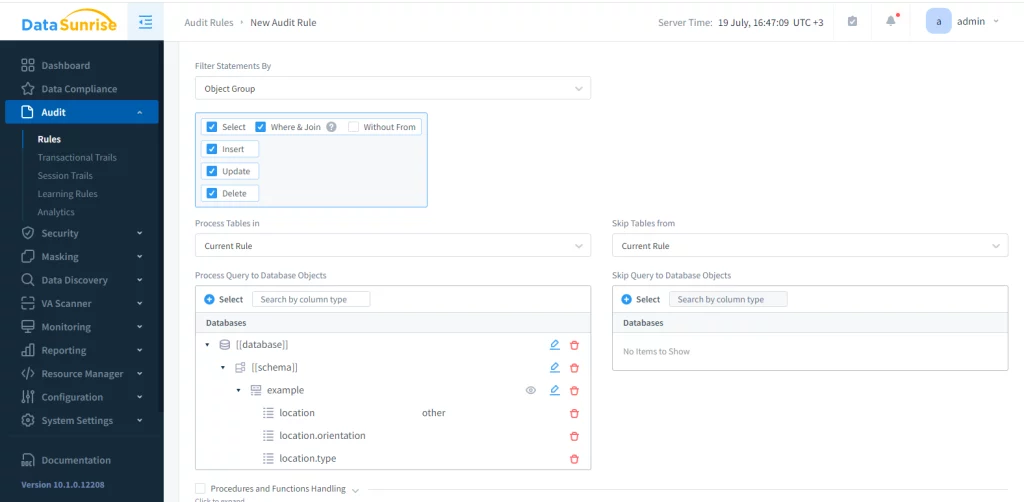
Managing Elasticsearch auditing with DataSunrise is as simple as it gets. Create your instance and select it in the Audit rule configuration. Then specify the objects you want to monitor. This process lets you quickly implement robust auditing tailored to your specific database needs. The image below depicts the configuration process of an audit rule for Elasticsearch storage.
DataSunrise catches queries and session events in both Transactional and Session Trails. An informative description follows each event. The Reporting Tool makes custom reports, providing insights on your activity and improving security.
Best Practices and Challenges
While comprehensive auditing provides detailed information, it can impact system performance. Focus on auditing critical data and high-risk activities. For example, prioritize auditing access to sensitive customer information over routine search queries.
Establish a routine for reviewing audit logs. This practice helps identify potential issues early and ensures the audit system functions correctly. Set up automated alerts for suspicious activities, such as multiple failed login attempts or unusual data access patterns.
Protect audit logs from unauthorized access or tampering. Use encryption and access controls to maintain the integrity of audit data. Consider storing audit logs in a separate, secure Elasticsearch cluster to prevent potential attackers from modifying the logs.
Implement automated tools to analyze audit logs. This approach assists in identifying patterns and anomalies that manual reviews might miss. Use Elasticsearch’s powerful aggregation and visualization capabilities to create dashboards for audit log analysis.
Establish a retention policy for audit records that complies with regulatory requirements and internal policies. Use Elasticsearch’s ILM to automatically move old audit data to cheaper storage options.
Implementing Elasticsearch database audit does come with challenges. Extensive auditing can affect performance, so striking a balance between comprehensive auditing and system efficiency is crucial. Monitor your cluster’s performance closely after enabling auditing and adjust your configuration as needed.
Audit logs can consume significant storage space over time. Plan for adequate storage capacity and implement efficient archiving strategies. Use Elasticsearch’s rollover and ILM features to manage audit indices effectively.
Setting up and managing a comprehensive audit system can be complex. It requires in-depth knowledge of Elasticsearch and careful planning. Invest in training for your team or consider working with Elasticsearch experts to implement auditing effectively.
Real-World Applications
Many industries benefit from Elasticsearch database audit. Online retailers use it to track access to customer data, monitor search patterns, and detect potential fraud. For instance, an online store could use auditing to find sudden increases in product views, which might show someone is scraping the website.
Hospitals and healthcare providers ensure HIPAA compliance by tracking who accesses patient information and when. A hospital can use Elasticsearch auditing to track which staff members accessed specific patient records and when.
This feature allows the hospital to generate reports based on this information. The reports can provide insights into who viewed the records and at what time. This helps the hospital monitor and manage access to patient information effectively.
Banks and financial institutions monitor access to sensitive financial data and track unusual transaction patterns. A bank can use Elasticsearch auditing to track searches for important accounts. This can help identify possible insider risks.
Government organizations use database auditing to maintain security and comply with regulations. A government agency might use Elasticsearch auditing to track access to classified documents and generate reports for security audits.
Future Trends
As Elasticsearch continues to evolve, we can expect to see more integration of machine learning capabilities with database auditing. This could lead to more sophisticated anomaly detection and predictive analytics for security threats.
Advanced auditing systems are moving towards real-time monitoring and alerting. This trend will likely continue in Elasticsearch, enabling faster response to potential security threats.
With the increasing adoption of cloud-based Elasticsearch deployments, auditing solutions will likely become more cloud-native. This could lead to more scalable and flexible auditing options for organizations using Elasticsearch in the cloud.
Conclusion
Database audit in Elasticsearch is a critical component of a robust security and compliance strategy. It helps organizations protect sensitive data, meet regulatory requirements, and maintain the integrity of their information systems. By implementing best practices and leveraging Elasticsearch’s powerful features, organizations can enhance their security posture and gain valuable insights into database operations.
As data in Elasticsearch increases, organizations need to audit their databases. This is important for protecting data and ensuring transparency in IT systems.
