
Implementing a Robust Data Deletion Policy
Introduction
As businesses have moved online and data analysis automation has become more affordable and easier to use, data has become a crucial resource for companies of all sizes. That’s why managing information effectively is crucial for businesses and organizations. One often overlooked aspect of data management is the implementation of a robust deletion policy. This article will explore the fundamentals of sensitive information deletion, how to implement an effective deletion policy, and the statutory requirements for compliant enterprises.
What is a Data Deletion Procedure?
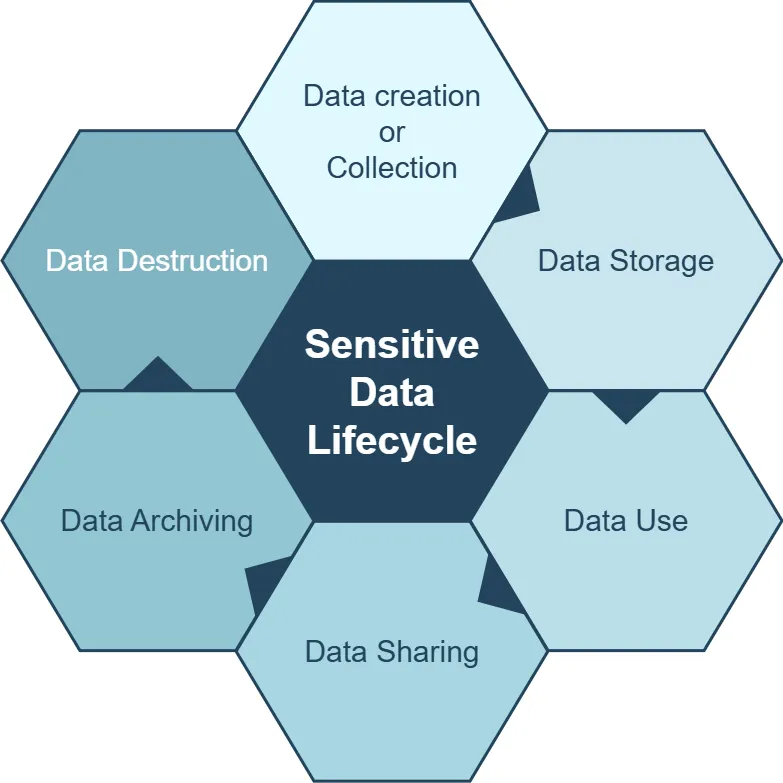
The Internet continues to grow rapidly, and businesses use it to provide their customers with better services. However, this often requires gathering and processing sensitive data.
A sensitive data deletion procedure is a systematic approach to removing unnecessary or outdated information from an organization’s systems. A critical component of data management ensures data privacy, reduces storage costs, and maintains data accuracy.
Key Components of a Data Deletion Procedure
- Identification of unnecessary data
- Classification of data types
- Secure deletion methods
- Documentation and auditing
Implementing an Effective Deletion Policy
Creating a comprehensive deletion policy requires careful planning and execution. Here are the steps to implement an effective policy:
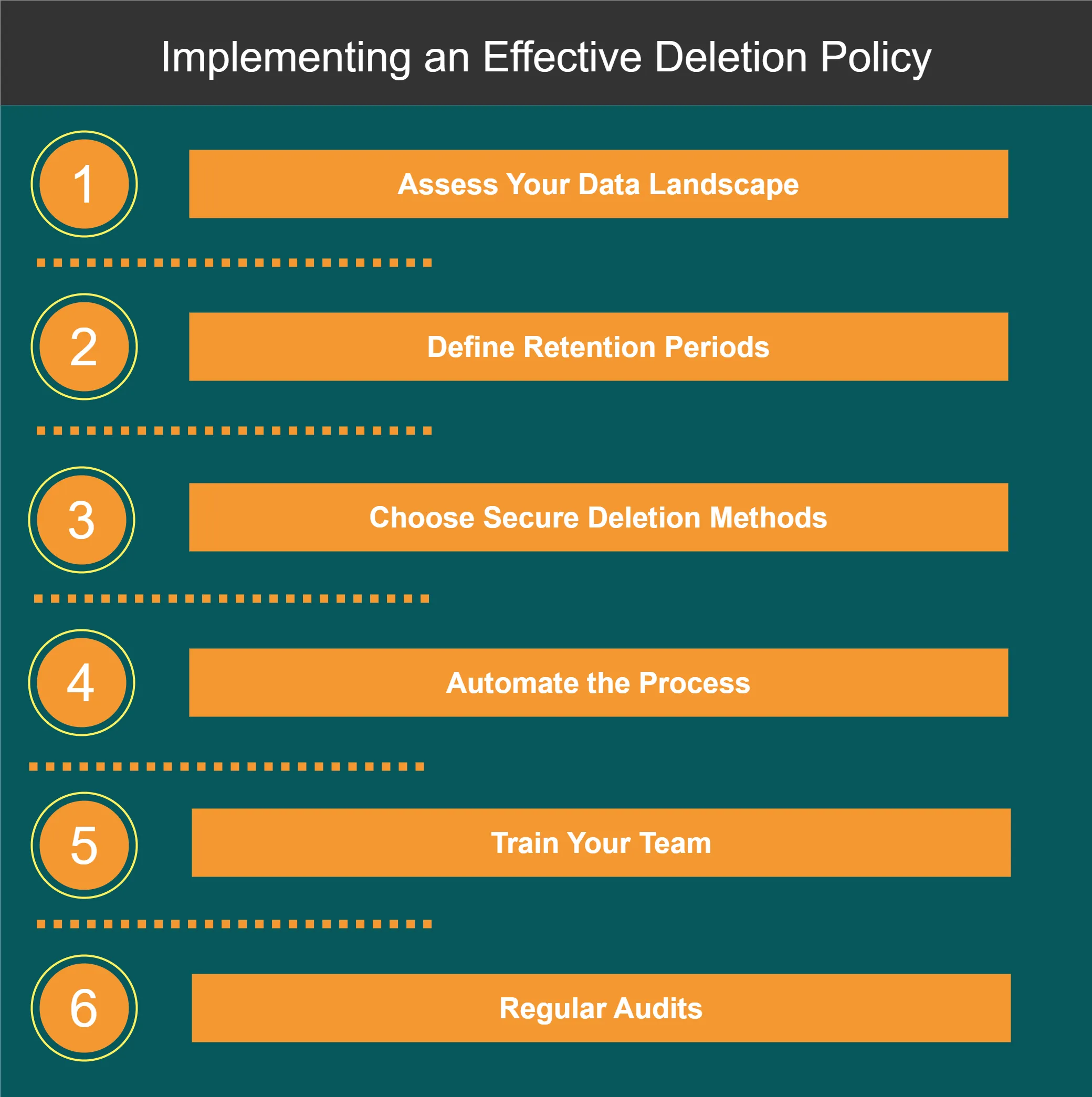
1. Assess Your Data Landscape
Before implementing a deletion policy, you need to understand your data:
- What types of data do you collect?
- Where do you store the sensitive data?
- How long do you need to keep this data?
2. Define Retention Periods
Establish clear retention periods for different types of data. For example:
- Customer data: 7 years after last interaction
- Financial records: 10 years
- Employee records: 3 years after employment ends
3. Choose Secure Deletion Methods
Select appropriate deletion methods based on data sensitivity:
- Standard deletion for non-sensitive data
- Secure erasure for confidential information
- Physical destruction for highly sensitive data
4. Automate the Process
Implement automated tools to streamline the deletion process:
import os
from datetime import datetime, timedelta
def delete_old_files(directory, days_threshold):
current_time = datetime.now()
for filename in os.listdir(directory):
file_path = os.path.join(directory, filename)
file_modified = datetime.fromtimestamp(os.path.getmtime(file_path))
if current_time - file_modified > timedelta(days=days_threshold):
os.remove(file_path)
print(f"Deleted: {filename}")
# Usage
delete_old_files("/path/to/directory", 30)This script deletes files older than a specified number of days in a given directory.
5. Train Your Team
Educate employees on the importance of data deletion and their role in maintaining the policy.
6. Regular Audits
Conduct periodic audits to ensure compliance with your deletion policy.
Statutory Requirements for Compliant Enterprises
Enterprises must adhere to various regulations when implementing deletion policies:
GDPR (General Data Protection Regulation)
The GDPR requires organizations to:
- Delete personal data when it’s no longer necessary
- Respond to user requests for data deletion (Right to be Forgotten).
CCPA (California Consumer Privacy Act)
Under the CCPA, businesses must:
- Delete consumer personal information upon request
- Disclose data deletion practices in their privacy policy
HIPAA (Health Insurance Portability and Accountability Act)
HIPAA-covered entities must:
- Implement policies for the disposal of electronic protected health information
- Ensure that no one can recover disposed data.
Best Practices for Unnecessary Data Management
Managing unnecessary data is crucial for maintaining an efficient and compliant data environment:
- Regular data audits
- Data minimization strategies
- Clear data classification guidelines
- Employee training on data management
Erased Data Privacy: Ensuring Complete Removal
When you delete sensitive data, you must ensure that no one can recover it.
Secure Erasure Methods
- Overwriting: Replace data with random patterns multiple times
- Degaussing: Use magnetic fields to erase data from magnetic storage
- Cryptographic erasure: Encrypt data and then destroy the encryption key
Example of secure file overwriting in Python:
import os
def secure_delete(filename, passes=3):
with open(filename, "ba+") as f:
length = f.tell()
with open(filename, "br+") as f:
for i in range(passes):
f.seek(0)
f.write(os.urandom(length))
os.remove(filename)
print(f"File {filename} securely deleted.")
# Usage
secure_delete("sensitive_file.txt")This script overwrites the file with random data multiple times before deleting it.
On the Software for Secure Erasure
Developers design specialized software tools for secure data erasure. These tools surpass simple deletion to guarantee that no one can recover the data.
Here’s a list of some popular secure erase software tools:
CCleaner:
- Offers a secure drive wiper feature
- Can overwrite free space and entire drives
Eraser:
- Open-source tool for Windows
- Allows scheduling of secure deletions
- Supports various erasure methods
DBAN (Darik’s Boot and Nuke):
- Bootable program that securely wipes entire hard drives
- Often used for decommissioning computers
Disk Wipe:
- Free tool for Windows
- Supports multiple overwriting algorithms
Secure Eraser:
- User-friendly interface
- Offers file, folder, and drive wiping
BleachBit:
- Open-source cleaner for Windows and Linux
- Includes secure deletion features
HDDErase:
- Uses the ATA Secure Erase command
- Particularly effective for SSDs
Apple’s Disk Utility (for macOS):
- Built-in tool for securely erasing drives on Mac systems
Linux shred command:
- Built-in Unix/Linux command-line tool
- Overwrites files to make them harder to recover
BitRaser:
- Professional-grade erasure software
- Complies with various data protection standards
These tools use methods like overwriting data multiple times with random patterns to make sure the data cannot be retrieved. Consider the sensitivity of your data when choosing a tool. Also, think about whether you use a hard drive or solid-state drive. Additionally, consider any industry regulations that you need to adhere to.
Note that for SSDs, secure erasure can be more complex. This is because of wear leveling and other SSD-specific features. In such cases, tools that support ATA Secure Erase or manufacturer-specific secure erase commands are often more effective.
Case Study: Implementing a Deletion Policy in a Healthcare Organization
A large healthcare provider implemented a comprehensive deletion policy to comply with HIPAA regulations:
- They categorized data into patient records, administrative data, and research data.
- Retention periods: 10 years for patient records, 7 years for administrative data, and 5 years for research data.
- They implemented an automated system to flag data for review when retention periods expired.
- Staff uses secure deletion methods for all patient data.
- Regular audits ensured compliance with the policy.
Result: The organization reduced storage costs by 30% and significantly improved their compliance posture.
Challenges in Implementing Deletion Policies
While essential, implementing deletion policies can present challenges:
- Legacy systems with limited deletion capabilities
- Balancing data retention for business needs vs. privacy concerns
- Ensuring consistent policy application across all data storage locations
- Managing deletion in distributed and cloud environments
The Future of Data Deletion Policies
As data privacy concerns grow, we can expect:
- More stringent regulatory requirements
- Advanced AI-driven data management tools
- Increased focus on privacy-enhancing technologies
- Greater emphasis on data minimization from the outset
Summary and Conclusion
A well-implemented data deletion policy is crucial for modern enterprises. It ensures compliance with regulations, protects user privacy, and optimizes data storage. Organizations can keep their data management strong by following best practices and staying up-to-date on regulations.
Remember, an effective deletion policy is not just about erasing data; it’s about fostering a culture of responsible data management throughout your organization.
For user-friendly and flexible tools for database security and compliance, consider exploring DataSunrise’s offerings. Visit our website for an online demo and discover how we can help streamline your data management processes.
