
Enhancing Data Security with Dynamic Data Masking in Cassandra

Dynamic data masking in Cassandra offers a powerful solution for protecting sensitive information. Organizations can secure their data while maintaining the performance and scaling that Cassandra is famous for with this feature. We’ll explore how dynamic data masking works in Cassandra, its benefits, and practical implementation strategies.
Understanding Dynamic Data Masking in Cassandra
Dynamic data masking is a security technique that hides or obfuscates sensitive data in real-time. It doesn’t alter the original data but instead presents a masked version to unauthorized users. This approach ensures that it protects sensitive information without affecting the underlying data structure.
Cassandra, a popular NoSQL database, handles large volumes of data across distributed systems. Adding dynamic data masking to Cassandra enhances its security features. It allows organizations to protect sensitive information without sacrificing the database’s performance or scaling.
Cassandra’s dynamic data masking operates at the query level. When a user requests data, the system checks their permissions. If the user lacks proper logging, they receive a masked version of the sensitive fields. This process happens in real-time, ensuring that data stays protected throughout its lifecycle.
Benefits and Implementation
Dynamic data masking in Cassandra provides an additional layer of security. It prevents unauthorized access to sensitive information, reducing the risk of data breaches and compliance violations.
Many industries face strict data protection regulations. Cassandra’s dynamic data masking helps organizations meet these requirements by controlling access to sensitive data. This feature simplifies compliance with standards like GDPR, HIPAA, and PCI-DSS.
Cassandra’s native dynamic data masking offers flexible configuration options. Administrators can define masking rules based on user roles, data types, or specific columns. This granular control allows for precise data protection tailored to organizational needs.
Unlike some security measures, dynamic data masking in Cassandra has minimal impact on database performance. The masking occurs in real-time without altering the original data, ensuring that queries remain fast and efficient.
To implement dynamic data masking in Cassandra, administrators define masking rules. These rules specify which columns to mask and how to mask them. For example, you might mask a social security number by showing only the last four digits.
CREATE MASKING RULE ssn_mask
ON users.ssn
USING ‘XXX-XX-‘ + SUBSTRING(ssn, 8, 4);
This rule masks the first five digits of a social security number, displaying only the last four.
After creating masking rules, administrators assign permissions to users or roles. This step determines who can see the original data and who receives the masked version.
GRANT SELECT ON users TO analyst_role MASKED;
This command grants the analyst_role permission to view the users table, but with masked data.
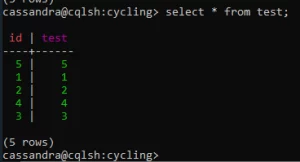
This method, however, might be difficult to perform in a large-scale storage. We suggest using third-party solutions, like DataSunrise, for an easier approach. Let’s say we want to mask the result of this query:
To apply dynamic data masking via DataSunrise, you need to take several steps.
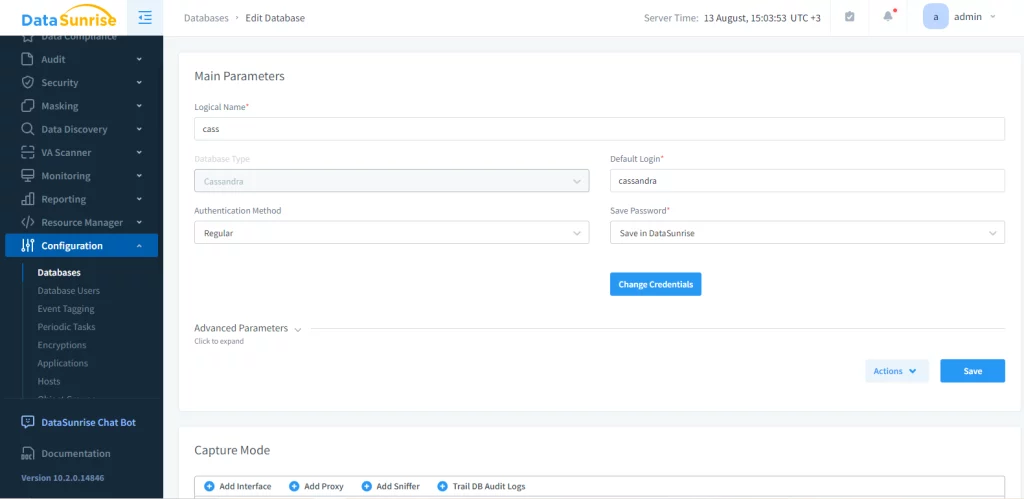
First, you need to create an instance of Cassandra database. This will help monitor, hide, and protect all actions of the source database using its proxy.
After this, you can conduct a masking rule configuration in the correlating menu section. During this stage, we choose the data to mask and the masking method. In this example we’ll mask ‘test’ table in ‘cycling’ keyspace.
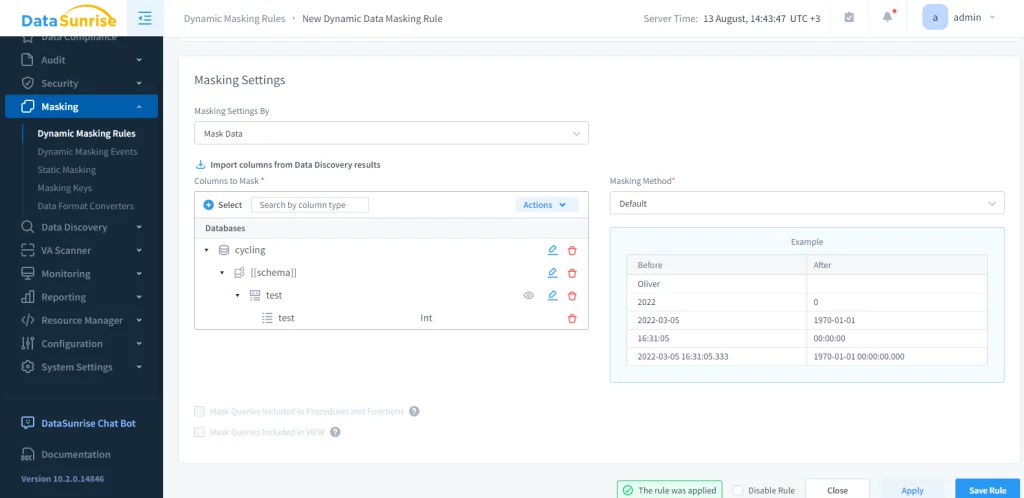
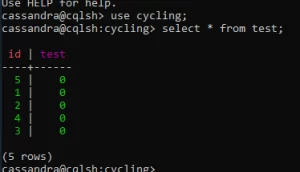
Once the rules and permissions are in place, it’s crucial to test the implementation. This process ensures that authorized users can access the original data while unauthorized users see only masked information. The result we get is as follows:
Best Practices and Considerations
Conduct regular audits of your masking rules and permissions. This practice helps identify any gaps in your security setup and ensures ongoing protection of sensitive data. Use clear and consistent naming conventions for your masking rules. This approach makes it easier to manage and update rules as your data protection needs evolve.
Maintain thorough documentation of your dynamic data masking implementation. This resource helps team members understand the security measures in place and facilitates troubleshooting when issues arise. While dynamic data masking generally has minimal impact on performance, it’s important to monitor your Cassandra cluster. Keep an eye on query response times and resource usage to ensure optimal performance.
Make sure you consistently apply masking rules across your Cassandra cluster. Inconsistent masking can lead to security weaknesses or data discrepancies. Educate your team about dynamic data masking in Cassandra. Users should understand how it works and why it’s important for data protection.
Consider how dynamic data masking integrates with your existing security infrastructure. Ensure that it complements other measures like encryption and access controls.
Conclusion
Improvements may involve better masking methods, improved machine learning for spotting issues, and enhanced performance efficiency.
Dynamic data masking in Cassandra offers a powerful tool for protecting sensitive information. By implementing this feature, organizations can enhance their data security posture without sacrificing the performance and scaling that make Cassandra a popular choice. Dynamic data masking will play a more important role in protecting data as different industries use it in Cassandra.
