
Dynamic Data Masking in Elasticsearch: Secure Data Without Compromising Usability

Elasticsearch, a powerful search and analytics engine, offers various features to manage and protect sensitive information. One such feature is dynamic data masking, which helps organizations secure their data while maintaining its usability. This article explores dynamic data masking in Elasticsearch, its benefits, and how to implement it effectively.
Understanding Dynamic Data Masking
Dynamic data masking is a security technique that limits access to sensitive data in real-time. It works by replacing original values with masked or scrambled versions when unauthorized users query the data. This approach ensures that it protects sensitive information while allowing authorized users to access the unmasked data.
Elasticsearch implements dynamic data masking through its security features. When enabled, it intercepts queries and applies masking rules before returning results. This process occurs instantly, making sure that private information stays within the system unless viewed by authorized users.
Dynamic data masking in Elasticsearch adds an extra layer of security to sensitive information. It reduces the risk of data breaches by limiting exposure to unauthorized users. Many industries face strict regulations regarding data protection, and Elasticsearch dynamic data masking helps organizations meet compliance requirements by controlling access to sensitive data. Additionally, this feature enables organizations to safely share data with partners, contractors, or developers without exposing sensitive information, improving collaboration while maintaining data security.
Implementing Dynamic Data Masking in Elasticsearch
To use dynamic data masking in Elasticsearch, you must first enable the security features. This step involves configuring authentication and its mechanisms. Once you enable security, you can define masking rules for specific fields. These rules determine how Elasticsearch will mask the data for unauthorized users.
Here’s an example of creating a role that can only read public data from the “customers” index:
PUT _security/role/masked_user
"indices": [
{
"names": [ "customers" ],
"privileges": [ "read" ],
"field_security": {
"grant": [ "*" ],
"except": []
},
"query": {
"term": {
"access_level": "public"
}
}
}
]
}
Elasticsearch offers various masking techniques for different data types. You can apply these masks to specific fields in your index mappings. For instance, you can mask a credit card field to show only the last four digits:
PUT my_index
{
"mappings": {
"properties": {
"credit_card": {
"type": "keyword",
"mask": "{{xxxx-xxxx-xxxx-####}}"
}
}
}
Implementation via DataSunrise
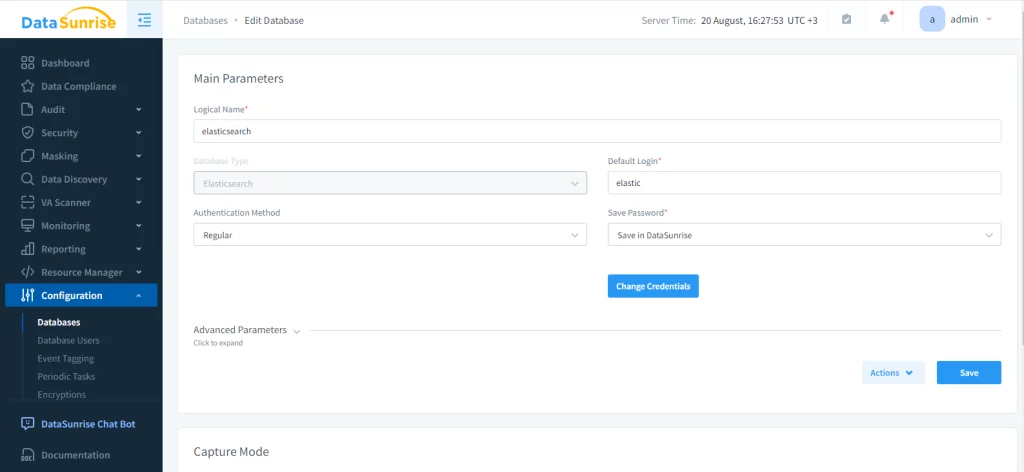
Elasticsearch has built-in tools for hiding data, but it can be challenging to use on large-scale databases. To simplify the process, experts suggest using third-party solutions like DataSunrise. First, you must add an instance of Elasticsearch database.
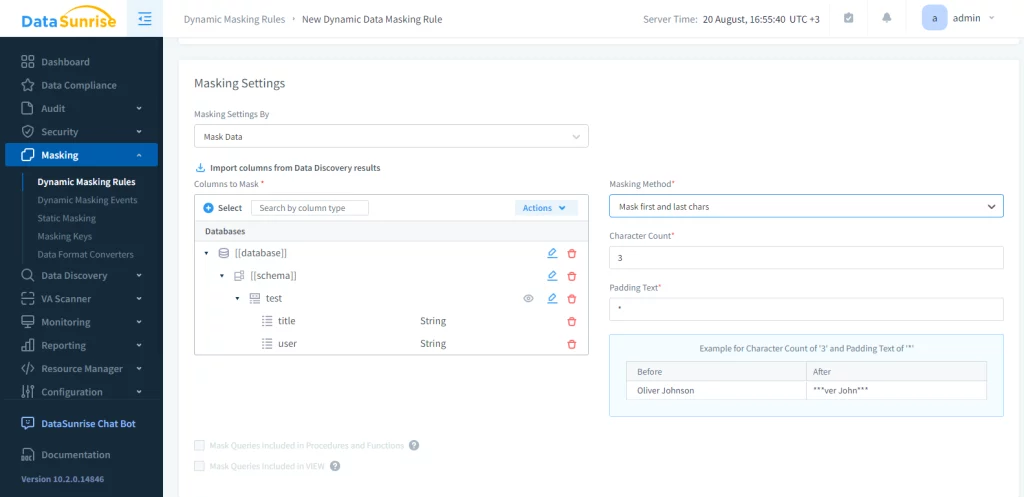
Now, masking rules and tasks can be created and applied.This can be done in the corresponding menu. In this example. we’ll mask the ‘test’ table:
Now let’s check the result of masking:
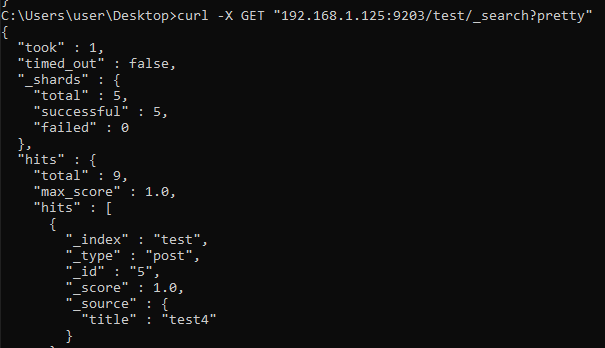
Before masking
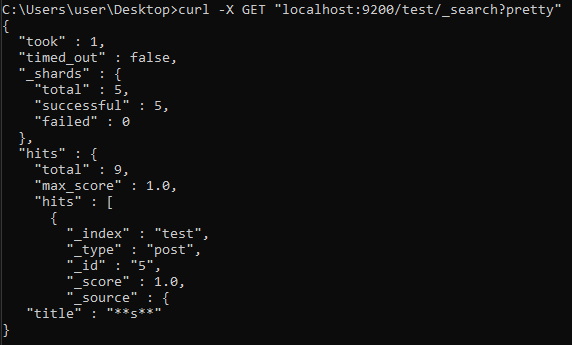
After masking
Best Practices and Challenges
To ensure the effectiveness of dynamic data masking in Elasticsearch, consider the following best practices:
- Conduct regular audits of your Elasticsearch security settings and masking rules. This helps identify potential vulnerabilities and ensures your data protection measures remain effective.
- Implement fine-grained access control in conjunction with dynamic data masking. This method customizes data access for users, adding extra security based on their roles and permissions.
- Monitor your Elasticsearch cluster’s performance and optimize masking rules as needed. While dynamic data masking enhances security, it can impact query performance. Regular monitoring helps strike a balance between security and performance.
- Thoroughly test your dynamic data masking implementation to ensure it works as expected. Validate that authorized users can access unmasked data while unauthorized users see only masked information.
- Document your masking rules and policies. Clear documentation helps maintain consistency across your organization and simplifies the onboarding process for new team members.
While implementing dynamic data masking, you may face some challenges. Finding the right balance between data protection and usability can be tricky. Regularly gather feedback from users and adjust your masking rules accordingly.
Elasticsearch dynamic data masking may also face challenges with nested objects or arrays. In such cases, consider using more advanced masking techniques or restructuring your data model.
As security threats evolve, your dynamic data masking strategy must adapt. Stay informed about the latest security best practices and update your Elasticsearch configuration regularly. Regularly review your masking rules to keep them effective against new threats and ensure they meet updated compliance requirements.
Real-World Applications
Dynamic data masking in Elasticsearch finds applications across various industries:
Healthcare facilities use technology to keep patient information safe and accessible to authorized staff for treatment purposes.
Finance: Banks and financial institutions can mask account numbers and transaction details, revealing full information only to authorized personnel.
E-commerce: Online retailers can protect customer data, showing full details only to customer service representatives when necessary.
Human Resources: Companies can mask employee salary information, revealing it only to HR personnel and managers with appropriate access levels.
Conclusion
Dynamic data masking in Elasticsearch offers a powerful solution for protecting sensitive information while maintaining data usability. By implementing this feature effectively and following best practices, organizations can enhance their data security posture and meet compliance requirements. As Elasticsearch continues to evolve, dynamic data masking will play an increasingly important role in safeguarding valuable information.
Elasticsearch dynamic data masking is a useful tool for organizations that handle sensitive information. Businesses can protect sensitive information by creating masking rules that balance data security and accessibility. This ensures that data remains secure while still allowing for legitimate use cases.
