
Dynamic Data Masking in PostgreSQL: Real-Time Protection for Sensitive Information

PostgreSQL, a powerful open-source database system, offers various security features to protect sensitive data. One such feature is dynamic data masking. This technique helps organizations safeguard confidential information without modifying the original data. Let’s explore how dynamic data masking works in PostgreSQL and why it’s crucial for data protection.
What is Dynamic Data Masking?
Dynamic data masking is a security method that hides sensitive data in real-time. It transforms the data as it retrieves it from the database. The original information remains intact, but users see only masked or altered versions. This approach ensures that it protects sensitive data while still allowing authorized users to access the necessary information.
Implementing Dynamic Data Masking in PostgreSQL
PostgreSQL implements dynamic data masking through views and row-level security policies. These features allow database administrators to control what data users can see based on their roles and permissions.
To implement dynamic data masking in PostgreSQL natively, you can create views that alter sensitive columns. Here’s an example:
CREATE VIEW masked_customers AS SELECT id, CASE WHEN current_user = 'admin' THEN full_name ELSE 'REDACTED' END AS full_name, CASE WHEN current_user = 'admin' THEN email ELSE LEFT(email, 2) || '****' || RIGHT(email, 4) END AS email, city, state FROM customers;
This view masks the full_name and email columns for non-admin users. Admins have the ability to see the original data, while other users view redacted or partially masked information.
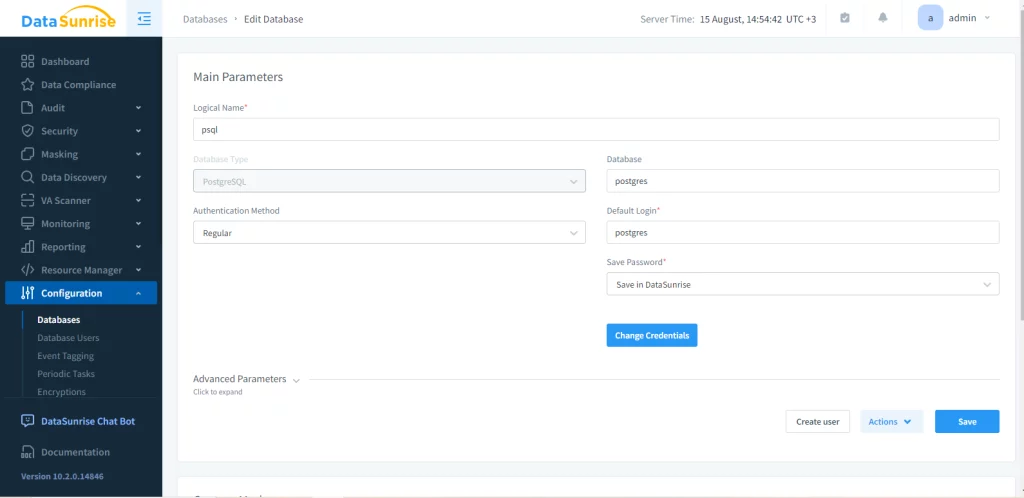
However, this might be complicated to pull off on a large-scale storage. To simplify the process, we suggest using third-party solutions. To operate in DataSunrise, you must first create an instance of the required database.
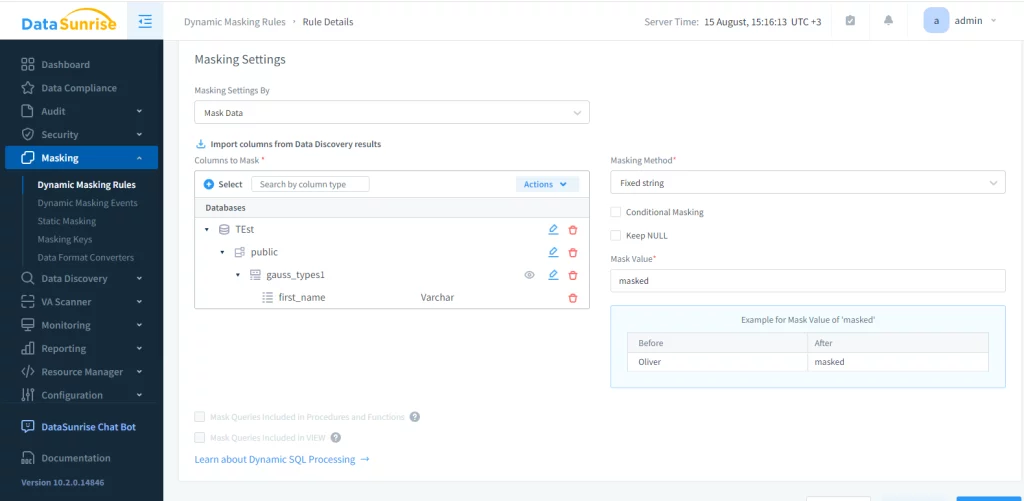
Now, you can create various kinds of rules for the proxy of the database instance. For dynamic data masking we need to proceed to the correlating menu and add a new rule. In this example we’ll mask the ‘first_name’ column of the ‘gauss_types1’ table in the ‘Test’ database.
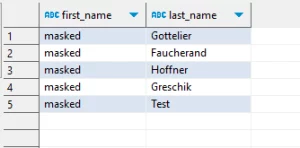
After applying the rule and executing the query, this is the result we get:
Benefits and Challenges
Dynamic data masking in PostgreSQL provides several benefits. It enhances data protection by preventing unauthorized access to sensitive information. This helps reduce the risk of data breaches and insider threats. It also aids in compliance with strict data protection regulations by limiting access to sensitive data.
For development and testing, dynamic data masking allows teams to work with realistic datasets without exposing sensitive information. Users can create custom data masking rules based on user roles, data types, and specific needs. This gives administrators flexibility in protecting data.
However, implementing dynamic data masking comes with challenges. It may impact query performance, especially for complex masking rules or large datasets. Maintaining data integrity is crucial, requiring careful planning and testing of masking rules. User education is also important, as users need to understand how dynamic data masking works and why it’s necessary.
Best Practices
To effectively implement dynamic data masking in PostgreSQL, consider these best practices:
- Identify sensitive data elements that require protection.
- Use role-based access control (RBAC) to manage user permissions effectively.
- Regularly review and update masking rules to ensure they remain effective and relevant.
- Implement logging and auditing mechanisms to track who accesses masked data and when.
- Thoroughly test masking rules and policies before deploying in production.
- Consider using encryption for extremely sensitive information in addition to dynamic data masking.
By following these practices, organizations can create a robust data protection strategy that balances security with usability.
Conclusion
Dynamic data masking in PostgreSQL is a powerful tool for protecting sensitive information. It allows organizations to balance data security with usability, ensuring that users have access to the information they need while safeguarding confidential data. PostgreSQL users can create a strong data protection plan by combining dynamic data masking with other security measures. This plan follows rules and reduces the risk of data leaks.
As data protection becomes increasingly important, dynamic data masking will continue to play a crucial role for PostgreSQL users. Organizations that use PostgreSQL should include this feature in their security plan. This will help protect sensitive data and ensure compliance with data protection laws.
