
Greenplum Data Audit Trail

In today’s data-driven landscape, maintaining comprehensive data audit trails is crucial for database security and compliance. As organizations face increasingly sophisticated cyber threats, implementing proper audit mechanisms in Greenplum Database environments is essential for protecting sensitive data and maintaining regulatory compliance.
According to IBM’s Cost of a Data Breach Report 2023, the average cost of a data breach reached $4.45 million globally, with inadequate monitoring and audit systems being significant contributing factors.
For businesses managing sensitive information, Greenplum Database offers systematic tracking and verification of database activities through its native auditing features. This methodical approach supports the implementation of data security controls and compliance measures.
Understanding Greenplum Data Audit Trail
Greenplum’s audit system consists of several interconnected components:
- Server Log Files: Each database instance maintains its own server log containing detailed activity records
- Audit Catalogs: System tables storing audit-related metadata
- Segment-Level Logging: Distributed audit capture across all segments
- Coordinator Node Aggregation: Centralized collection of audit data
Configuring Greenplum Data Audit Trail
Basic Configuration
To enable comprehensive audit trailing in Greenplum, apply these essential settings:
-- Enable basic audit logging ALTER SYSTEM SET logging_collector = on; ALTER SYSTEM SET log_destination = 'csvlog'; -- Configure detailed logging parameters ALTER SYSTEM SET log_statement = 'all'; ALTER SYSTEM SET log_min_duration_statement = 1000; ALTER SYSTEM SET log_connections = on; ALTER SYSTEM SET log_disconnections = on;
Advanced Audit Configuration
For enhanced audit capabilities, implement these additional settings:
-- Enable extended logging details ALTER SYSTEM SET log_error_verbosity = 'verbose'; ALTER SYSTEM SET log_line_prefix = '%t [%p]: [%l-1] user=%u,db=%d,app=%a,client=%h '; -- Configure audit file management ALTER SYSTEM SET log_rotation_age = '1d'; ALTER SYSTEM SET log_rotation_size = '100MB'; ALTER SYSTEM SET log_truncate_on_rotation = on;
Practical Implementation Examples
Monitoring Data Access Patterns
SELECT
usename,
date_trunc('hour', query_start) as access_time,
count(*) as access_count,
string_agg(DISTINCT client_addr::text, ', ') as source_ips
FROM
pg_stat_activity
WHERE
datname = 'testdb'
AND query ILIKE '%public.clients%'
AND query_start >= current_timestamp - interval '24 hours'
GROUP BY
usename,
date_trunc('hour', query_start)
ORDER BY
access_time DESC;Example output:
| usename | access_time | access_count | source_ips |
|---|---|---|---|
| admin | 2024-02-12 15:00:00 | 45 | 192.168.1.100, 192.168.1.101 |
| analyst | 2024-02-12 14:00:00 | 28 | 192.168.1.102 |
| etl_user | 2024-02-12 14:00:00 | 15 | 192.168.1.103 |
| support | 2024-02-12 13:00:00 | 8 | 192.168.1.104 |
Tracking Schema Modifications
SELECT
event_timestamp,
usename,
command_tag,
object_type,
object_identity,
command
FROM
pg_audit_log
WHERE
command_tag IN ('ALTER TABLE', 'CREATE TABLE', 'DROP TABLE')
AND object_identity LIKE '%public.clients%'
ORDER BY
event_timestamp DESC;Example output:
| event_timestamp | usename | command_tag | object_type | object_identity | command |
|---|---|---|---|---|---|
| 2024-02-12 15:30:00 | admin | ALTER TABLE | TABLE | public.clients | ALTER TABLE public.clients ADD COLUMN email VARCHAR(255) |
| 2024-02-12 14:45:00 | admin | ALTER TABLE | TABLE | public.clients | ALTER TABLE public.clients ADD PRIMARY KEY (id) |
| 2024-02-12 14:00:00 | etl_user | CREATE TABLE | TABLE | public.clients | CREATE TABLE public.clients (id serial, …) |
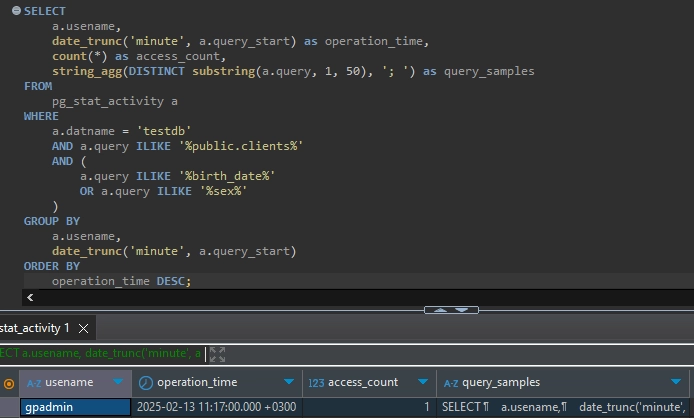
Monitoring Sensitive Data Access
SELECT
a.usename,
date_trunc('minute', a.query_start) as operation_time,
count(*) as access_count,
string_agg(DISTINCT substring(a.query, 1, 50), '; ') as query_samples
FROM
pg_stat_activity a
WHERE
a.datname = 'testdb'
AND a.query ILIKE '%public.clients%'
AND (
a.query ILIKE '%birth_date%'
OR a.query ILIKE '%sex%'
)
GROUP BY
a.usename,
date_trunc('minute', a.query_start)
ORDER BY
operation_time DESC;Example output:
Enhancing Audit Capabilities with DataSunrise
While Greenplum’s native audit trail features provide essential monitoring capabilities, organizations often require additional functionality. DataSunrise extends these capabilities with:
- Real-time activity monitoring
- Advanced security analytics
- Automated compliance reporting
- Centralized audit management
- Custom audit rule creation
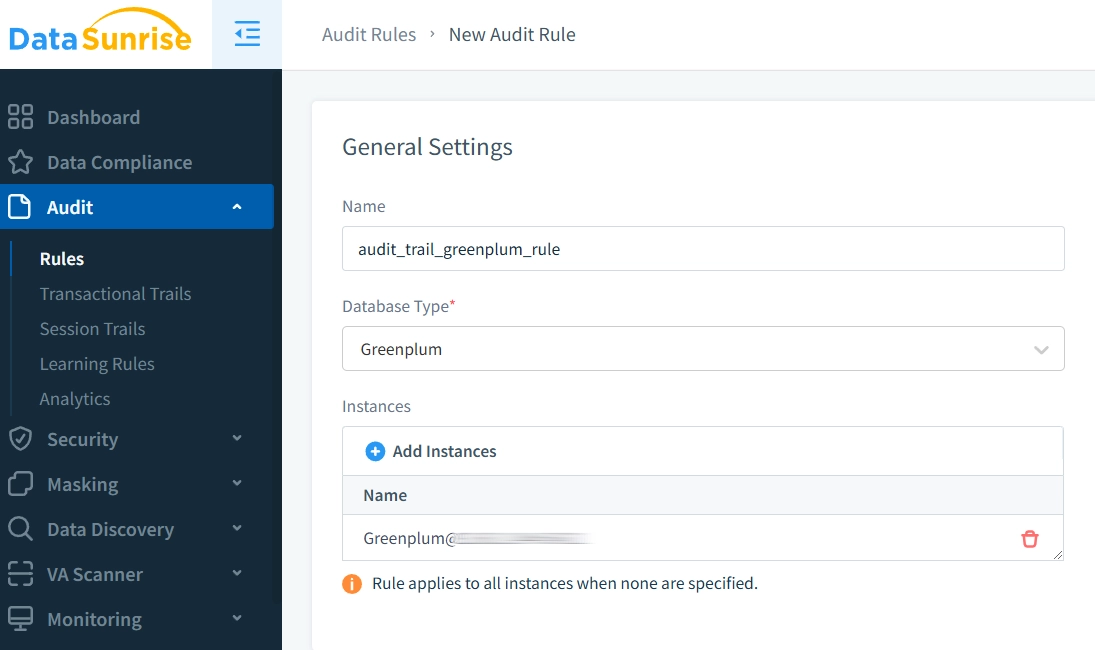
Creating Custom Audit Rules
DataSunrise provides an intuitive interface for creating and managing audit rules, allowing precise control over what database activities are monitored.
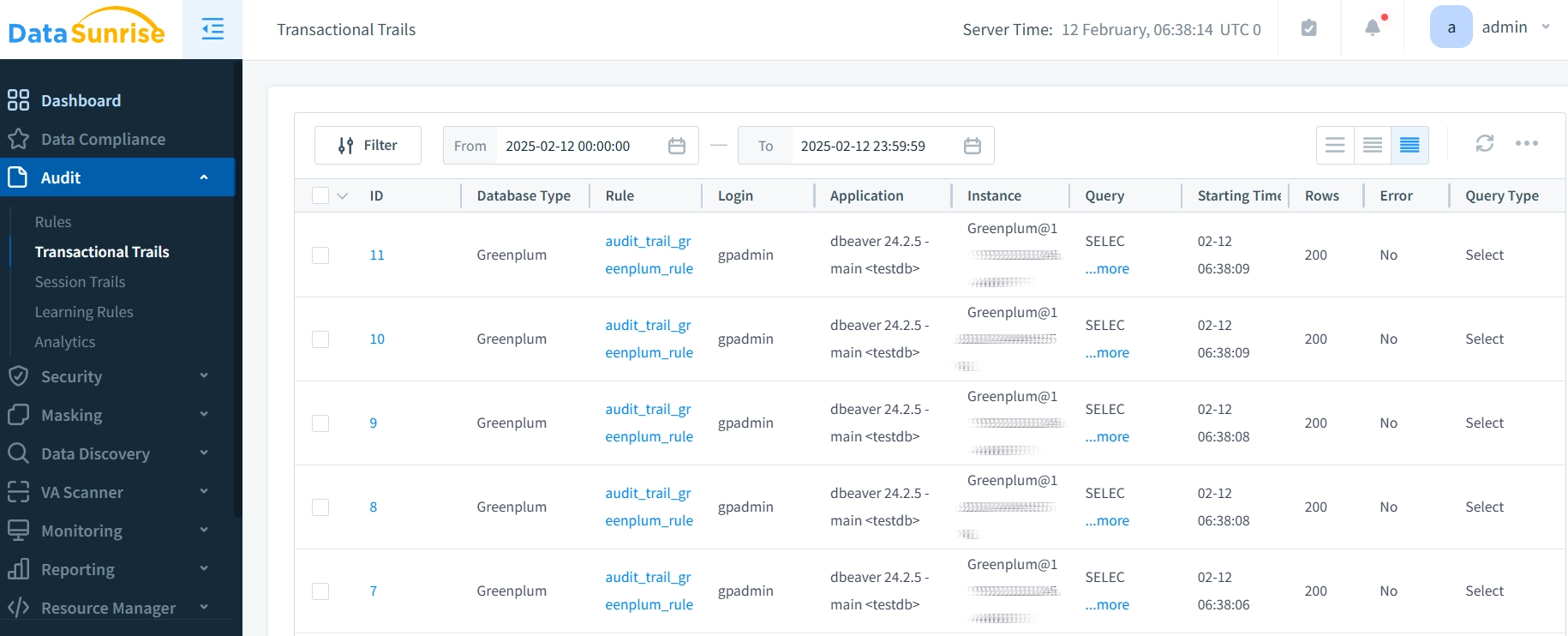
Analyzing Audit Results
The platform offers comprehensive visualization of audit trails, making it easy to track and analyze database activities in real-time.
Integration Benefits
- Enhanced Visibility: Comprehensive view of all database activities
- Automated Compliance: Streamlined regulatory reporting
- Advanced Security: Real-time threat detection
- Centralized Management: Unified audit trail monitoring
Best Practices for Audit Trail Management
Performance Optimization
- Implement selective logging based on operation criticality
- Use appropriate log rotation policies
- Archive older audit records regularly
- Monitor audit trail storage impact
Security Considerations
- Encrypt sensitive audit data using role-based access controls
- Implement strict access controls for audit logs
- Regular backup of audit trails
- Maintain audit trail integrity checks
Third-Party Solutions
- Implement advanced data masking and monitoring capabilities
- Set up centralized audit management systems
- Maintain consistent policies across all monitoring tools
- Schedule regular security assessments
Compliance Requirements
- Establish clear retention policies aligned with GDPR
- Document all audit configurations comprehensively
- Perform regular compliance checks through vulnerability assessment
- Implement automated reporting mechanisms
Conclusion
Implementing a robust data audit trail in Greenplum requires a comprehensive approach combining native capabilities with advanced security tools. DataSunrise provides flexible, cutting-edge solutions that enhance your database security through advanced audit trail management, real-time monitoring, and automated compliance reporting.
Experience DataSunrise’s powerful database security and audit capabilities firsthand by scheduling an online demo today. Let our experts show you how to strengthen your Greenplum database security while streamlining compliance processes.
