How to Automate Data Compliance for Apache Impala
Introduction
Apache Impala provides high-performance, low-latency SQL analytics for data stored in Hadoop environments. However, ensuring compliance with regulations like GDPR, HIPAA, PCI DSS, and SOX requires robust automation and security controls. Without proper tools to automate data compliance, organizations face significant risks including data breaches, regulatory penalties, and audit failures.
This guide explains how to automate compliance in Apache Impala using both built-in capabilities and enterprise-grade solutions like DataSunrise to implement comprehensive access control, auditing, data masking, and compliance reporting.
Compliance Automation with Apache Impala Native Tools
Impala includes several native features and integrations with the Hadoop ecosystem that form the foundation of compliance automation:
Step 1: Implement Policy-Based Data Classification
Data classification is the cornerstone of any compliance strategy, ensuring sensitive data is properly identified and protected.
Integration with Apache Atlas
Impala can integrate with Apache Atlas for metadata management and data governance:
<!-- atlas-application.properties -->
<property>
<name>atlas.hook.impala.enabled</name>
<value>true</value>
</property>
<property>
<name>atlas.cluster.name</name>
<value>ImpalaCluster</value>
</property>
This configuration enables automated tagging and classification of sensitive data elements within Impala tables, creating a foundation for compliance controls based on data categories.
Step 2: Enforce Access Controls and Security Policies
Impala supports role-based access control (RBAC) through integration with Apache Ranger:
SQL for RBAC Implementation
-- Create a role for compliance officers
CREATE ROLE compliance_officer;
-- Grant selective access to sensitive tables
GRANT SELECT ON DATABASE compliance_db TO ROLE compliance_officer;
GRANT SELECT ON TABLE customer_data(id, name, region) TO ROLE compliance_officer;
-- Assign role to specific users
GRANT ROLE compliance_officer TO USER auditor1;
This approach ensures that only authorized users can access sensitive data, with permissions that can be granularly controlled at the database, table, or column level.
Step 3: Automate Audit Logging and Monitoring
Comprehensive audit trails are essential for compliance verification. Enable Impala's native audit logging:
# Impala daemon configuration
--audit_event_log_dir=/var/log/impala/audit
--audit_log_level=full
--audit_log_format=json
These settings ensure all database operations are logged, including:
- Query execution details
- Authentication events
- Metadata operations
- Data access patterns
The audit logs can be analyzed to verify compliance with regulatory requirements and detect potential security incidents.
Step 4: Automate Compliance Reporting
Regular compliance reports are required by most regulatory frameworks. While Impala doesn't include built-in reporting tools, you can implement automated solutions:
Custom Reporting Scripts
#!/usr/bin/python
import json
import datetime
# Parse Impala audit logs
def generate_compliance_report():
with open('/var/log/impala/audit/impala_audit_log.json', 'r') as f:
logs = [json.loads(line) for line in f]
# Filter for sensitive data access
sensitive_access = [log for log in logs if 'pii_data' in log['query'].lower()]
# Generate report
report = {
'date': datetime.datetime.now().isoformat(),
'sensitive_data_access_count': len(sensitive_access),
'access_by_user': {}
}
# Output to file
with open(f'compliance_report_{datetime.date.today()}.json', 'w') as f:
json.dump(report, f, indent=2)
# Execute daily
if __name__ == "__main__":
generate_compliance_report()
This script example demonstrates how organizations can develop custom reporting solutions based on Impala audit logs.
Step 5: Implement Data Masking for Compliance
Data masking is crucial for protecting sensitive information while maintaining its utility for analysis:
Creating Masked Views in Impala
-- Create a view with masked sensitive data
CREATE VIEW masked_customer_data AS
SELECT
customer_id,
REGEXP_REPLACE(email, '(.{2})(.*)(@.*)', '$1***$3') AS email,
CONCAT(SUBSTR(phone_number, 1, 3), '-XXX-XXXX') AS phone,
CASE
WHEN credit_score < 600 THEN 'Below 600'
WHEN credit_score BETWEEN 600 AND 750 THEN '600-750'
ELSE 'Above 750'
END AS credit_range
FROM customer_data;
This approach allows non-privileged users to access data for analytics while obscuring the actual sensitive values, helping maintain compliance with data privacy regulations.
How to Automate Data Compliance for Apache Impala in 3 Easy Steps with DataSunrise
While Impala's native capabilities provide a foundation for compliance, DataSunrise offers a comprehensive, automated approach that simplifies implementation and management.
Step 1: Connect Your Impala Database
Begin by connecting DataSunrise to your Impala environment. The platform supports various deployment models including cloud, on-premises, and hybrid architectures.

The connection wizard guides you through specifying host, port, authentication methods, and database details.
Step 2: Configure Compliance Settings
From the Compliance Manager dashboard, select your Impala database connection, choose the relevant compliance regulations (GDPR, HIPAA, PCI DSS, SOX), and set your preferred reporting schedule.
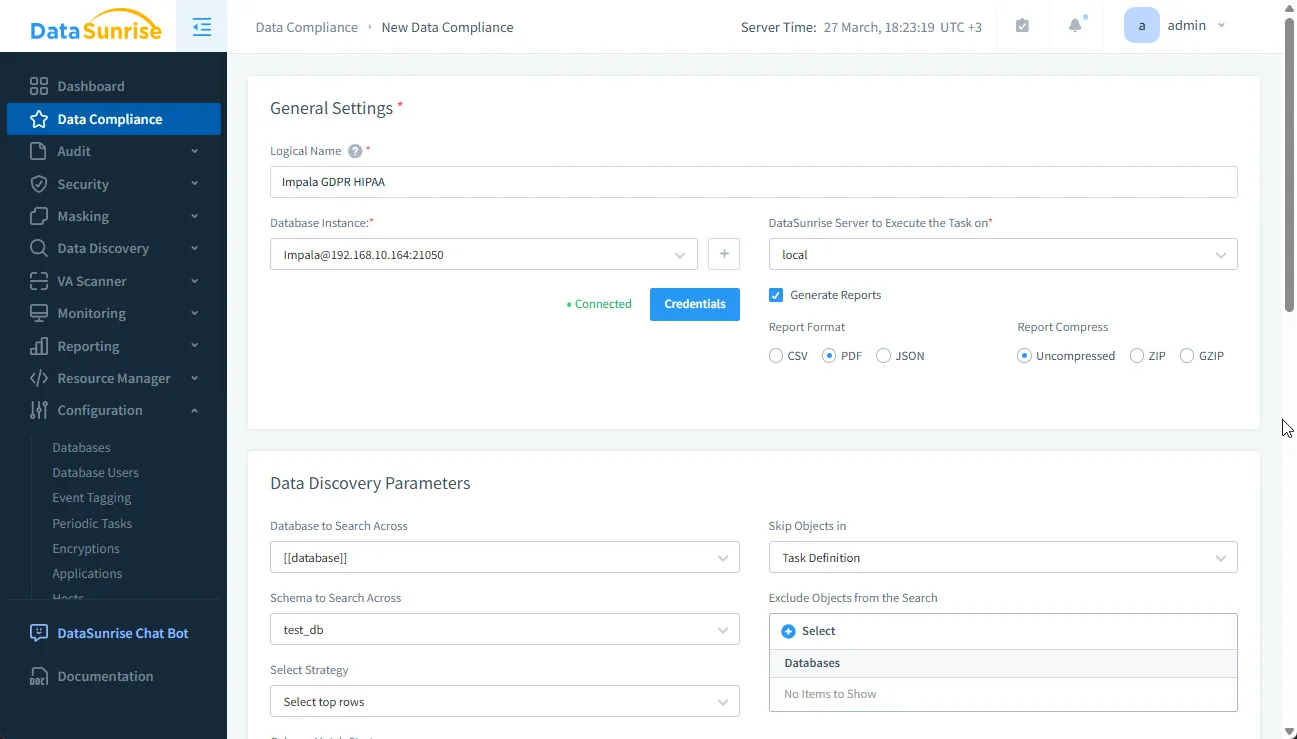
The platform allows you to specify which types of sensitive data to scan for, including PII, financial information, and healthcare data.
Step 3: Click Save – DataSunrise Does the Rest
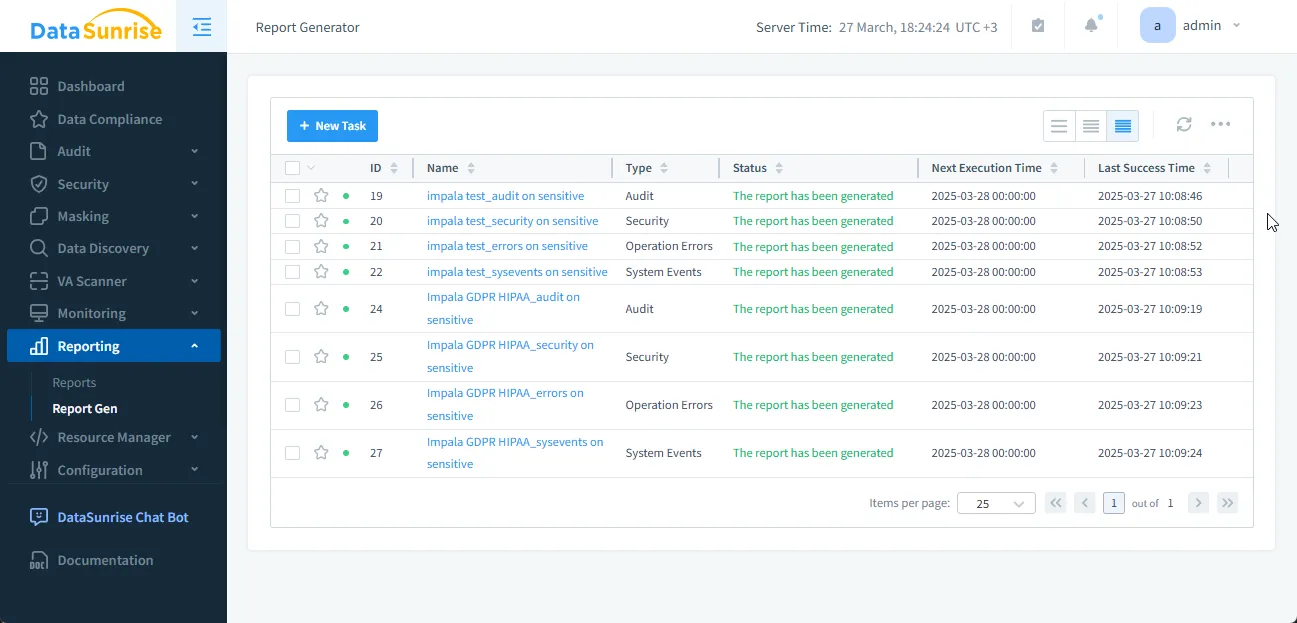
Once configured, DataSunrise automatically:
- Runs intelligent data discovery to identify and classify sensitive data in Impala tables
- Applies comprehensive audit rules for complete visibility into database activity
- Enforces security policies to prevent compliance violations
- Deploys dynamic data masking to protect personally identifiable information
- Generates detailed compliance reports according to your schedule
This zero-touch implementation transforms compliance from a manual, resource-intensive process into a streamlined, automated workflow.
Key Features of DataSunrise for Apache Impala
DataSunrise enhances Impala's security capabilities with advanced automation and monitoring:
- Automated Data Auditing – Records all database activities in a tamper-proof audit trail
- Real-Time Access Control – Enforces dynamic security policies based on user, time, location, and data content
- Dynamic Data Masking – Protects sensitive information without modifying original data
- Threat Detection – Identifies SQL injection attempts and anomalous query patterns
- Automated Compliance Reports – Generates pre-built reports for GDPR, HIPAA, PCI DSS, and SOX
- Enterprise Integration – Connects with SIEM solutions and security platforms via standardized APIs
Conclusion
Automating data compliance in Apache Impala requires a combination of native security features and enterprise-grade automation tools. While Impala provides essential capabilities like audit logging and access controls, these native features often lack the comprehensive automation required for complex compliance environments.
DataSunrise enhances Impala's compliance capabilities with:
- Real-time security policy enforcement
- Advanced audit logging and behavioral analytics
- Automated compliance reporting and documentation
- Dynamic data masking and access controls
For organizations seeking to streamline Impala compliance and reduce security risks, DataSunrise offers a comprehensive solution that transforms manual compliance processes into automated workflows.
Schedule a live demo to see how DataSunrise can automate compliance for your Apache Impala environment.
