
Impala Audit Trail

Introduction
As organizations grapple with an unprecedented tsunami of data – reaching 181 zettabytes projected by 2025 – the security stakes have never been higher. According to recent research from Accenture, 68% of business leaders report the cybersecurity risks are increasing, with data-intensive operations facing the greatest exposure. For organizations using Apache Impala, which has been a cornerstone of big data analytics since its introduction by Cloudera in 2012, implementing robust audit trails has evolved from a recommended practice to a fundamental business necessity.
For security analysts and IT compliance teams, Impala audit trails provide crucial visibility into user actions and database events, helping detect anomalies and identify potential risks. This capability becomes even more critical given that data breaches and unauthorized access are becoming increasingly sophisticated. With the growing volume and complexity of data, organizations need robust tools to monitor and secure their data environments. Impala audit trails are essential not only for compliance with regulations like GDPR or HIPAA, but also for maintaining data integrity and protecting sensitive information from malicious actors.
Understanding Impala Audit Trail Capabilities
An Impala audit trail records a comprehensive log of activities and changes within an Impala environment. These logs capture user actions, including query executions, schema changes, and data modifications. Impala provides built-in audit logging features that focus on the following:
- User Activity Monitoring: Identifies which users accessed the system, what data they queried, and when.
- Query Logging: Tracks the execution of SQL queries, including their success or failure.
- Data Change Logging: Monitors operations like insertions, updates, and deletions.
Impala's native audit capabilities are crucial for identifying potential security breaches and ensuring compliance with internal and external regulations. These logs are instrumental in anomaly detection and risk management, allowing security analysts to spot unusual patterns or unauthorized access.
Setting Up Impala Audit Trail: A Practical Example
To enable an audit trail in Impala, you must configure native audit logging and validate that the settings are correctly applied. Follow these steps to set up and test the audit trail:
1. Configure Impala for Audit Logging
Audit logging is enabled by setting up parameters in the impalad configuration. Update the following settings to specify where the logs are stored and which events to capture:
--audit_event_log_dir=${DATA_DIR}/audit
--max_audit_event_log_file_size=5000
--max_audit_event_log_files=10
In a containerized setup, you enable audit logging by passing the necessary configuration parameters to the Impala daemon (impalad) at runtime. look for a function launching impala daemon and make changes to it similarly to the example below:
function start_impalad() {
# Create audit directory if it doesn't exist
mkdir -p ${DATA_DIR}/audit
daemon_entrypoint.sh impalad -log_dir=${DATA_DIR}/logs \
-abort_on_config_error=false -mem_limit_includes_jvm=true \
-use_local_catalog=true -rpc_use_loopback=true \
-kudu_master_hosts=${KUDU_MASTERS} \
--audit_event_log_dir=${DATA_DIR}/audit \
--max_audit_event_log_file_size=5000 \
--max_audit_event_log_files=10 &
}
Place these configurations in the startup file or as environment variables when launching the Impala daemon. This ensures all user actions and queries are logged.
For more detailed guidance on configuring audit logs, refer to the official Impala auditing documentation.
2. Validate the Configuration
After configuring the parameters, check if the logging setup is active:
- Confirm the audit log directory exists:
ls -l /var/lib/impala/audit
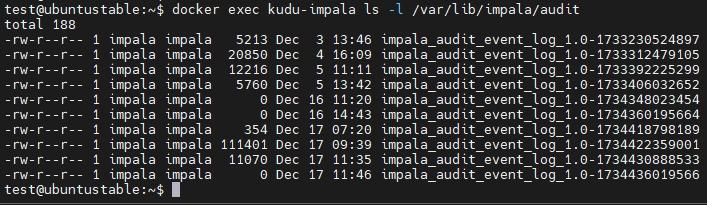
- Check if new audit log files are being generated as Impala processes queries:
tail -f $(ls -t /var/lib/impala/audit/impala_audit_event_log_1.0-* | head -1) | jq '.'
This command continuously monitors and formats the latest Impala audit log in real time, displaying its JSON content in a readable format using jq.
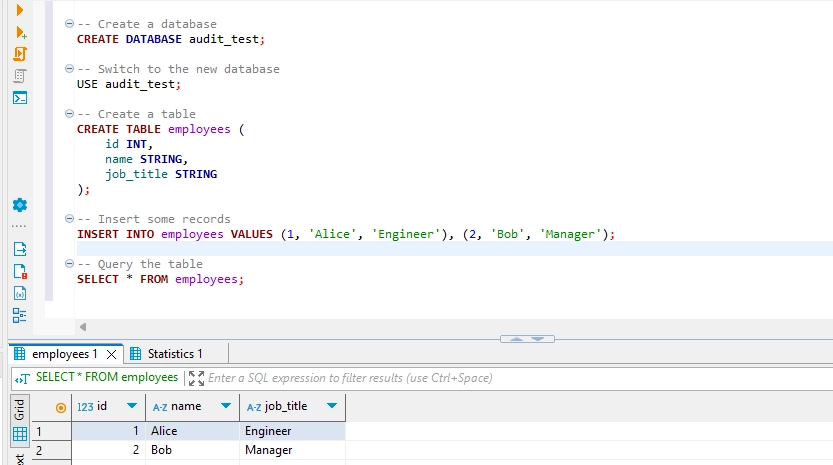
3. Execute Sample Queries
Run a series of SQL commands to ensure the audit trail is capturing activity. You could use the following commands as a test case:
-- Create a database
CREATE DATABASE audit_test;
-- Switch to the new database
USE audit_test;
-- Create a table
CREATE TABLE employees (
id INT,
name STRING,
job_title STRING
);
-- Insert some records
INSERT INTO employees VALUES (1, 'Alice', 'Engineer'), (2, 'Bob', 'Manager');
-- Query the table
SELECT * FROM employees;`
4. Verify the Audit Logs
Examine the audit log entries generated for the above queries. Logs are typically stored in JSON format and include information like user, timestamp, SQL query, and execution status. Use a tool like jq for easier reading:
cat /var/lib/impala/audit/* | jq `.`
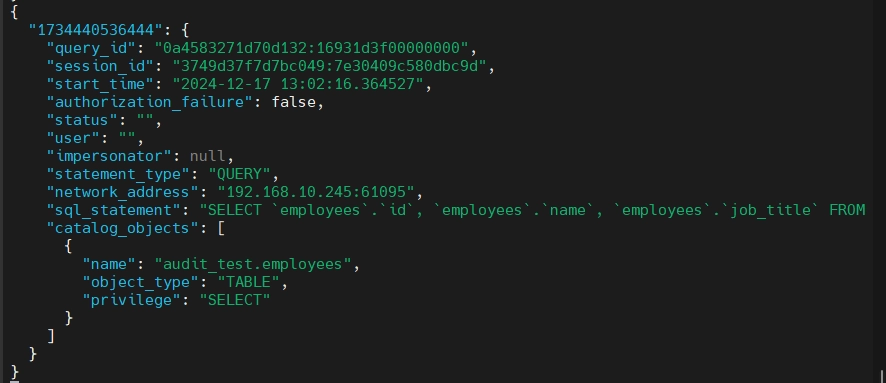
Verify that all executed commands are recorded in the logs, confirming the audit trail is functioning correctly.
Impala Audit Trail in DataSunrise
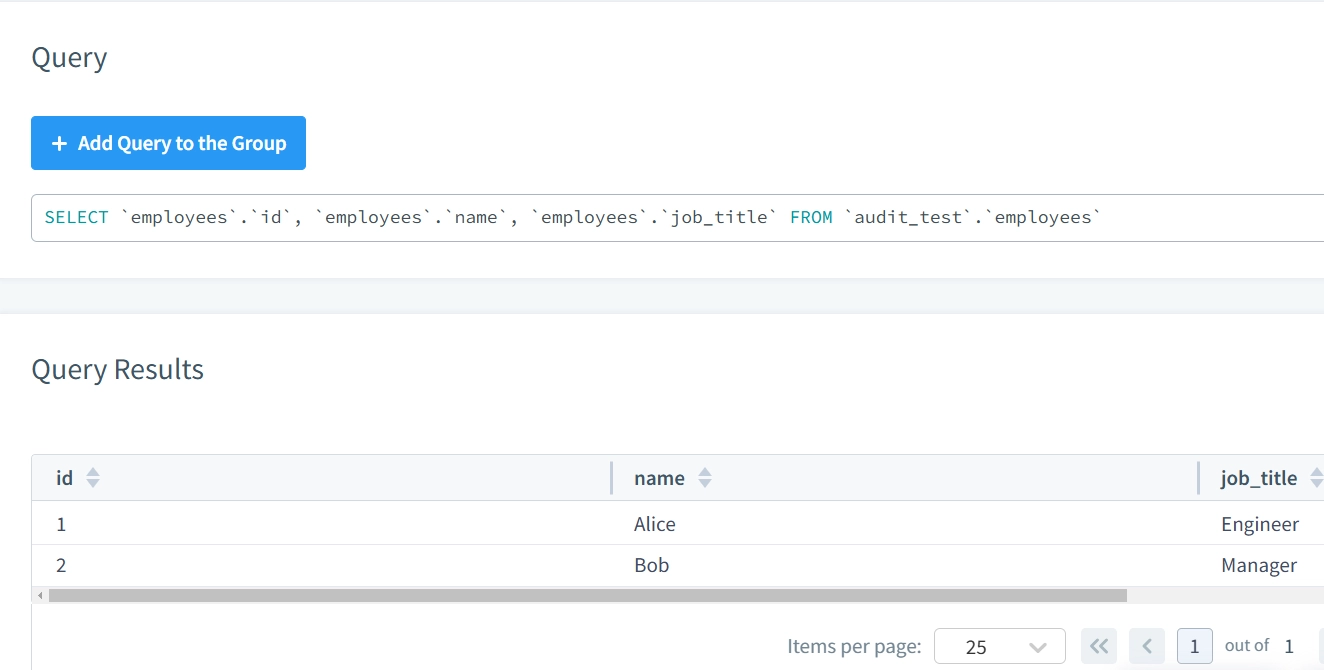
When it comes to audit trails, DataSunrise offers a far more user-friendly, flexible, and convenient approach, providing an extensive and detailed view of every action performed on the database. Below is an example of the same query execution captured by DataSunrise.
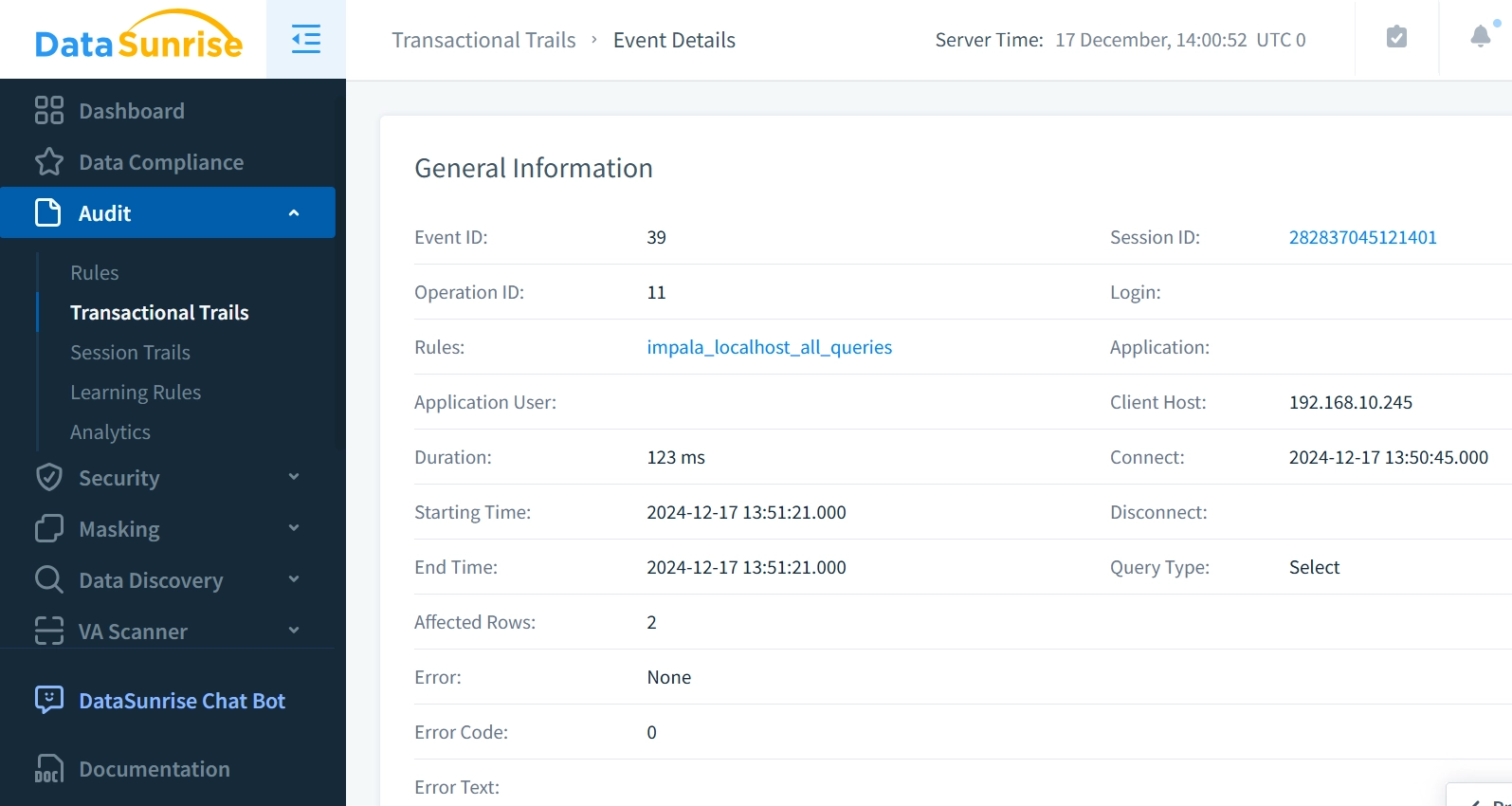
With DataSunrise, you can effortlessly view the result of each executed query, including the number of affected rows or any error codes/messages that may have been triggered.
In addition, DataSunrise captures detailed session trails for each connection to a running Impala instance, making it easier to trace the full activity of each session.
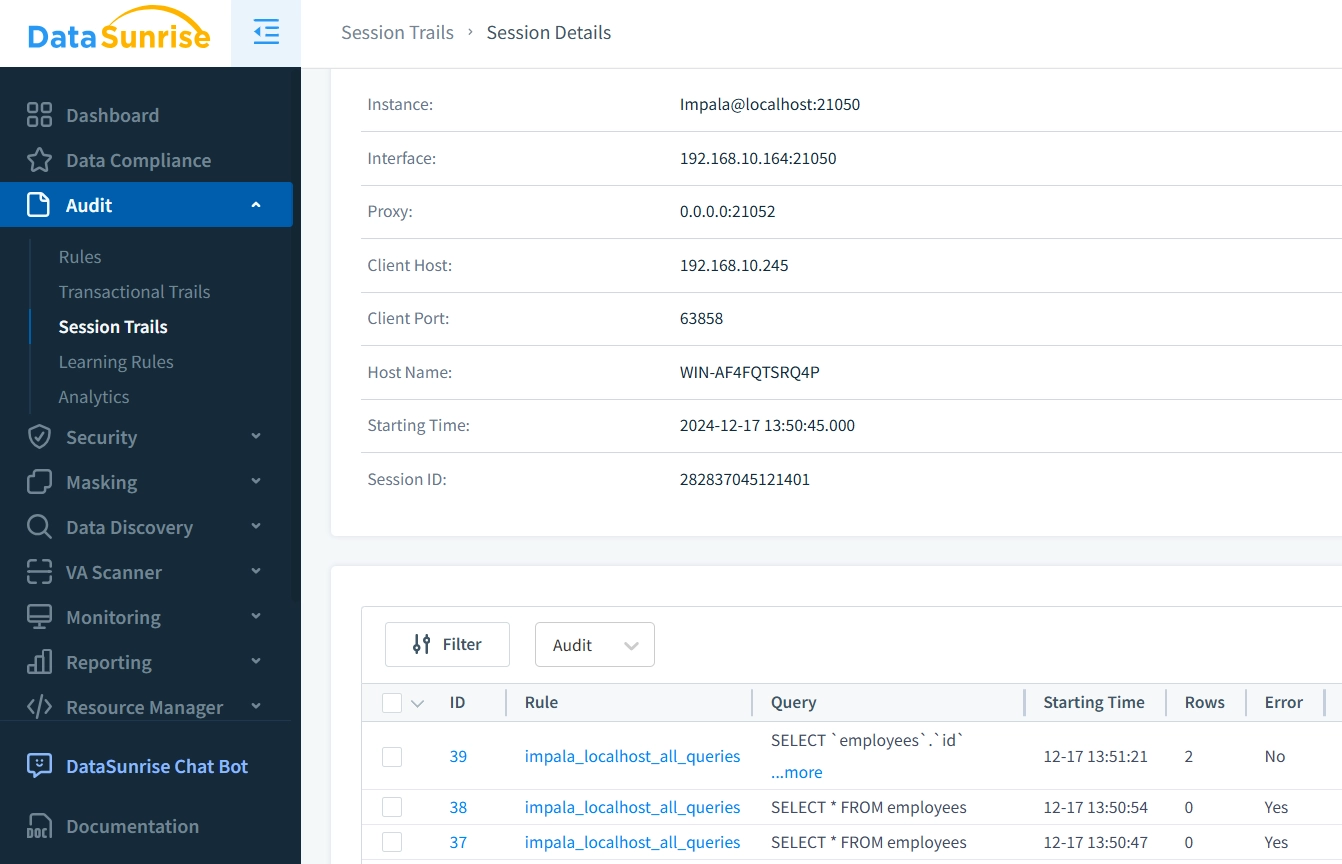
This level of granularity and clarity ensures that all activities are fully auditable, empowering administrators and security teams to maintain tight control over database operations.
Advantages of DataSunrise Audit Trails Over Impala’s Native Logging
Impala’s built-in audit log focuses mainly on technical details like session IDs, query types, and metadata, offering a snapshot of query execution without including key information like query outcomes, affected rows, or execution duration.
In contrast, DataSunrise provides a more comprehensive and user-friendly audit trail with several advantages:
- Complete Execution Overview: Captures session details and precise timestamps for connection, start, and completion, tracking the full query lifecycle.
- Query Outcome: Records the number of affected rows and displays query results and errors, which is essential for accurate auditing.
- Error Handling: Clearly indicates any errors, aiding in quick troubleshooting.
- Execution Duration: Logs the query's execution time (123 ms), valuable for performance analysis.
DataSunrise’s audit trail offers a richer, more actionable record compared to Impala’s native logging.
Enhancing Impala Audit Trail with DataSunrise
Impala's built-in audit log provides essential technical details about query activity, but integrating DataSunrise offers a far more comprehensive and actionable audit trail. With DataSunrise, you gain deeper insights into query execution, results, and performance while benefiting from enhanced security and compliance features. These include:
- Real-Time Monitoring: Tracks database activity instantly to identify threats as they occur.
- Advanced Reporting: Automatically generates compliance reports tailored to regulations like GDPR and HIPAA.
- Dynamic Data Masking: Safeguards sensitive data by masking it in real-time, preventing exposure in logs.
- Behavior Analytics: Analyzes user patterns to detect anomalies and potential security threats. DataSunrise not only enriches Impala's audit capabilities but also adds proactive security measures, such as real-time blocking of unauthorized actions, enhancing the overall security posture.
Conclusion
DataSunrise offers a superior database audit process for Impala, with advanced tools for monitoring, security, and compliance. By integrating DataSunrise, organizations can enhance their Impala environments with cross-platform support, an extensive feature set, and flexible deployment options. These capabilities empower businesses to stay ahead in an evolving regulatory landscape while ensuring robust database security. Experience the difference by scheduling an online demo today and discover how DataSunrise can transform your Impala auditing and security processes.
