
MongoDB Data Audit Trails

Introduction
As organizations increasingly leverage NoSQL databases, safeguarding the security and compliance of document-oriented systems becomes paramount. MongoDB, a popular choice for many enterprises, offers robust features for managing and storing data. Enter the concept of data audit trails – a vital tool for maintaining data integrity, tracking changes, and meeting regulatory requirements.
This year’s study reveals that lost business and post-breach response activities account for 75% of the rise in average breach costs. This startling statistic underscores the importance of implementing strong audit trail mechanisms in database systems like MongoDB.
Let’s explore MongoDB data audit trails. We will look at native tools, third-party solutions, and their benefits for businesses.
Understanding MongoDB Data Audit Trails
What is a Data Audit Trail?
A data audit trail is a chronological record of database activities. It captures who did what, when, and how, providing a comprehensive view of data interactions. For MongoDB, this is especially important given its flexible, document-oriented structure.
Native MongoDB Audit Capabilities
MongoDB offers built-in auditing features for enterprise configurations. These tools allow administrators to track database events, including:
- Schema changes
- Authentication attempts
- CRUD operations
- User management activities
Example 1 MongoDB Activity History: create database
The query is a database creation command:
use audit_test_2
For both replica set (rs) and standalone configurations, MongoDB’s audit log might look something like this (examples from real log):
{
"atype": "createDatabase",
"ts": {
"$date": "2024-09-19T09:37:06.659+00:00"
},
"uuid": {
"$binary": "VfFHqRSsQ0KPxEt2a0IhGg==",
"$type": "04"
},
"local": {
"ip": "192.168.10.45",
"port": 27017
},
"remote": {
"ip": "192.168.10.87",
"port": 25090
},
"users": [],
"roles": [],
"param": {
"ns": "audit_test_2"
},
"result": 0
}This JSON represents an audit log entry for a MongoDB database operation. Let’s break down its key components:
- “atype”: “createDatabase” – This indicates the type of action performed, which in this case is creating a new database.
- “ts”: The timestamp of when this action occurred (September 19, 2024, at 09:37:06 UTC).
- “uuid”: A unique identifier for this audit event.
- “local”: Information about the MongoDB server:
- “remote”: Information about the client that initiated the action:
- “users” and “roles”: These are empty arrays, suggesting the action was performed by an unauthenticated user or system process.
- “param”: Contains the parameter for the action:
- “ns”: “audit_test_2” – This is the name of the database being created.
- “result”: 0 – Operation was successful.
IP: 192.168.10.45 Port: 27017
IP: 192.168.10.87 Port: 25090
This log entry captures the creation of a new database named “audit_test_2” on September 19, 2024. It provides details about the server and client involved, as well as the outcome of the operation. Such audit logs are crucial for monitoring database activities, ensuring security, and maintaining compliance in MongoDB deployments.
Example 2 MongoDB Activity History: create collection
The query is as follows:
db.createCollection("test_data")The log entry:
{
"atype": "createCollection",
"ts": {
"$date": "2024-09-19T09:37:06.659+00:00"
},
"uuid": {
"$binary": "VfFHqRSsQ0KPxEt2a0IhGg==",
"$type": "04"
},
"local": {
"ip": "192.168.10.45",
"port": 27017
},
"remote": {
"ip": "192.168.10.87",
"port": 25090
},
"users": [],
"roles": [],
"param": {
"ns": "audit_test_2.test_data"
},
"result": 0
}This JSON represents another audit log entry for a MongoDB operation. Here’s a breakdown of its key components:
- “atype”: “createCollection” – This indicates the type of action performed, which in this case is creating a new collection.
- “ts”: The timestamp of when this action occurred (September 19, 2024, at 09:37:06 UTC).
- “uuid”: A unique identifier for this audit event.
- “local”: Information about the MongoDB server:
- “remote”: Information about the client that initiated the action:
- “users” and “roles”: These are empty arrays, suggesting the action was performed by an unauthenticated user or system process.
- “param”: Contains the parameter for the action:
- “ns”: “audit_test_2.test_data” – This indicates the namespace of the collection being created. It’s in the format “database.collection”, so a collection named “test_data” is being created in the “audit_test_2” database.
- “result”: 0 – Operation was successful.
IP: 192.168.10.45 Port: 27017
IP: 192.168.10.87 Port: 25090
This log entry captures the creation of a new collection named “test_data” within the “audit_test_2” database on September 19, 2024. It provides details about the server and client involved, as well as the outcome of the operation. Audit logs are important for tracking changes in database structure. They help keep data organized and maintain a complete audit trail in MongoDB systems.
Third-Party Audit Solutions: Spotlight on DataSunrise
While native tools are useful, third-party solutions like DataSunrise offer enhanced capabilities for MongoDB data audit trails.
DataSunrise Audit Trail Features
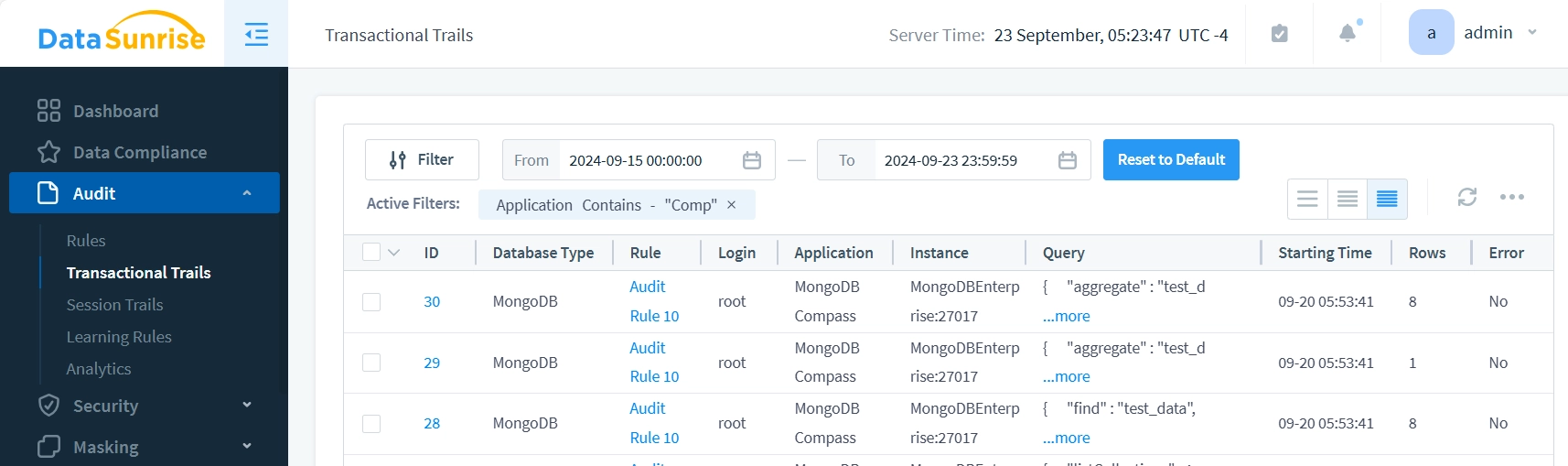
DataSunrise provides a comprehensive audit trail that captures:
- Detailed query information and bind variables
- User session data
- Application context (application user)
- Data before and after changes (both query and result)
- Failed queries and error messages
Benefits of Using DataSunrise for MongoDB Auditing
DataSunrise offers several advantages for enterprise MongoDB setups:
- Centralized control over audit rules
- Uniform approach for cloud and on-premise solutions
- Advanced filtering and reporting capabilities
- Real-time alerting for suspicious activities
- Compliance with various regulatory standards (GDPR, HIPAA, etc.)
Implementing Effective MongoDB Data Audit Trails
Best Practices for Audit Trail Implementation
- Define clear auditing objectives. DataSunrise offers advanced filtering capabilities, allowing users to precisely sift through events based on a wide range of attributes:
- Determine which events to capture.
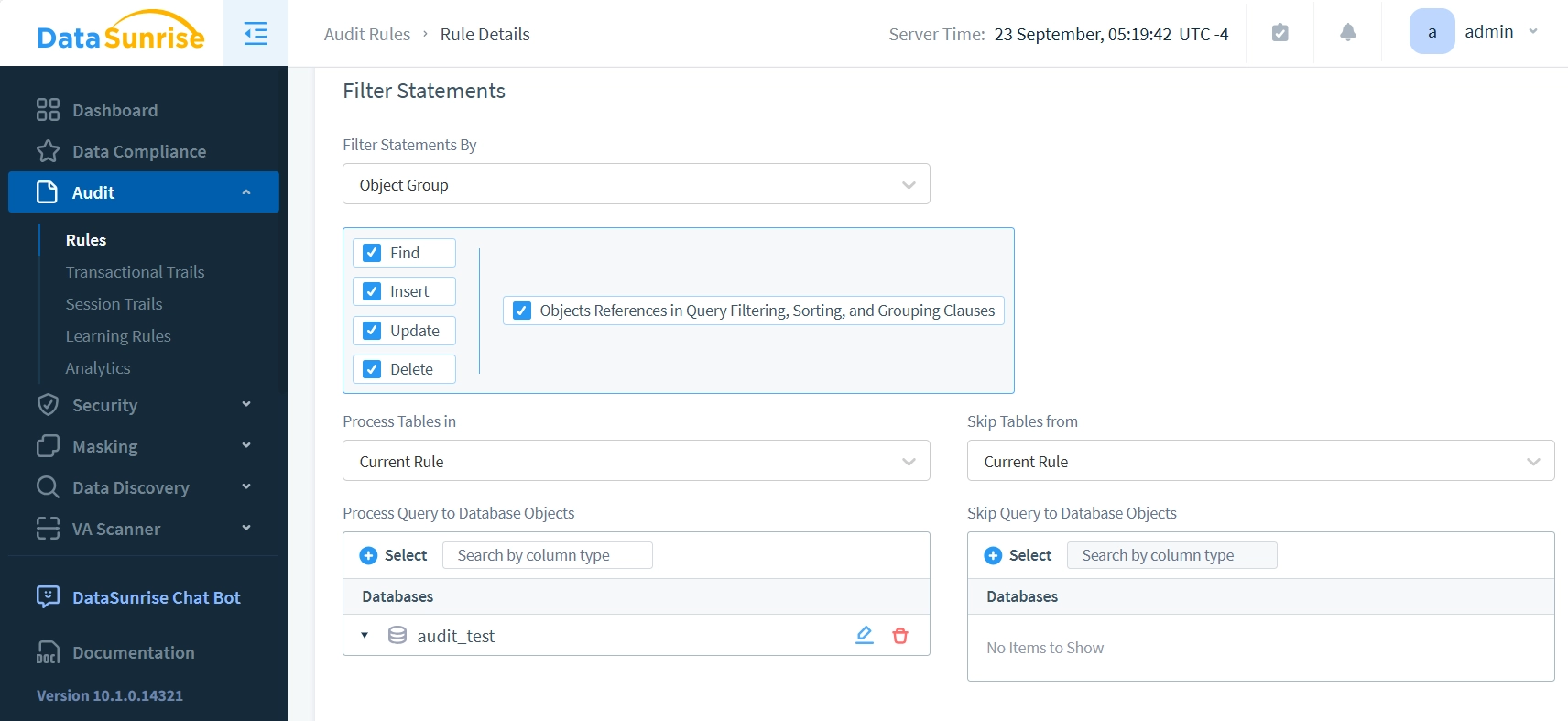
The image demonstrates the configuration of a comprehensive Audit Rule, designed to capture all major query types: Find, Insert, Update, and Delete operations.
- Establish retention policies
- Regularly review and analyze audit logs
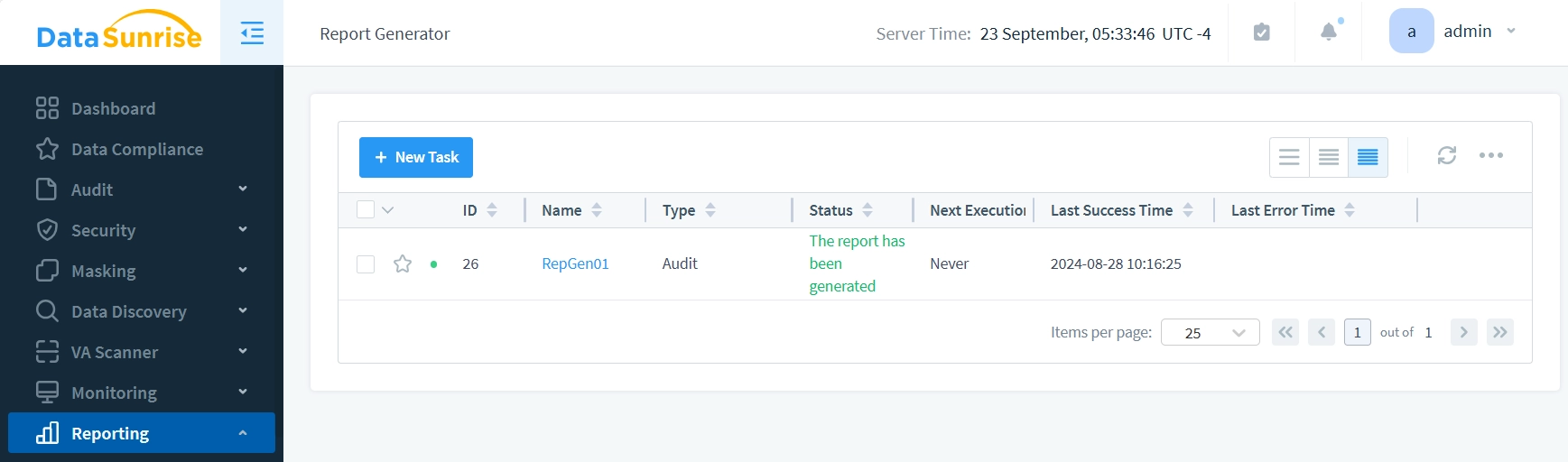
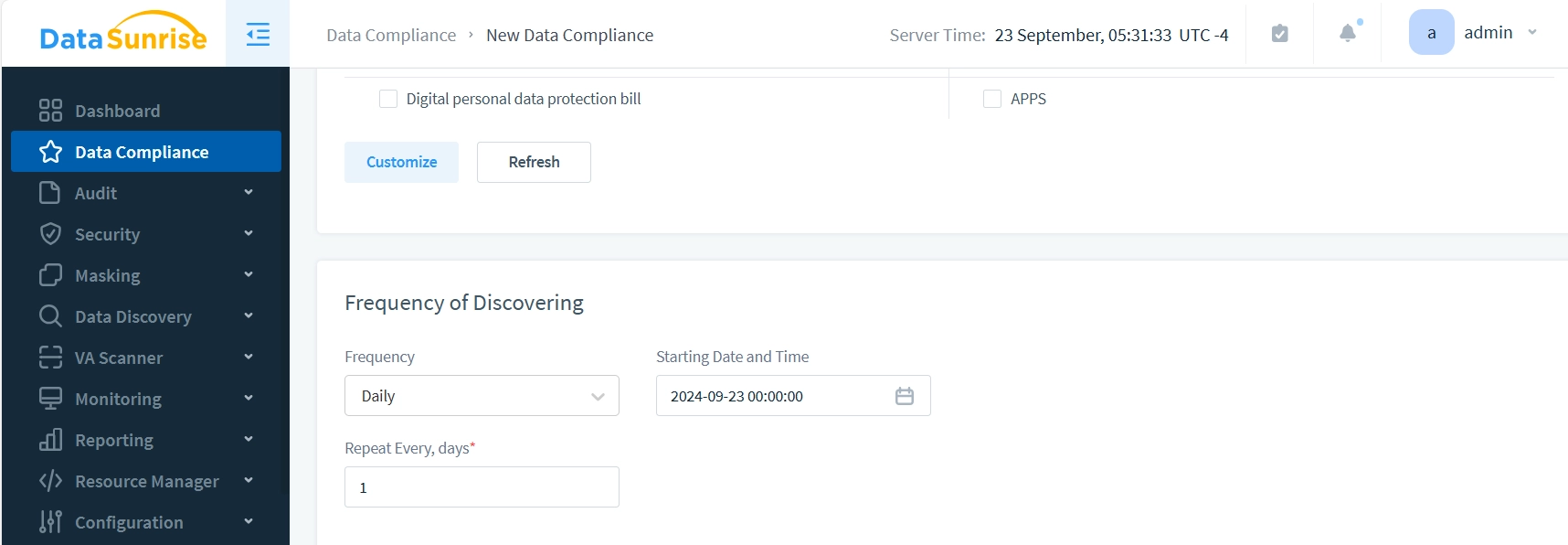
DataSunrise’s Compliance feature streamlines the process by automatically configuring scheduled operations, as illustrated in the following image:
- Implement secure storage for audit data.
Challenges in MongoDB Auditing
- Performance impact on database operations
- Storage requirements for audit logs
- Analyzing large volumes of audit data
- Maintaining data privacy in audit trails
The Future of MongoDB Data Audit Trails
As data volumes grow and regulatory landscapes evolve, MongoDB audit capabilities will continue to advance. We can expect to see:
- AI-powered anomaly detection in audit logs
- Enhanced integration with security information and event management (SIEM) systems
- More granular control over audit data collection
Conclusion
MongoDB data audit trails are essential for maintaining the security and compliance of document-oriented databases. While native tools provide basic functionality, third-party solutions like DataSunrise offer advanced features for comprehensive auditing and security management.
By implementing robust audit trails, organizations can protect their data, meet regulatory requirements, and gain valuable insights into database activities. Data security is becoming more important. Investing in good audit solutions is essential, not just a best practice.
DataSunrise offers a suite of flexible and user-friendly tools for database security, including data-aware security and masking features for both cloud and on-premise storages. Our solutions include AI-based features and AI-governance tools. These can hide sensitive data in or out of LLMs. For a firsthand experience of how DataSunrise can enhance your MongoDB security, we invite you to visit our website and schedule our online demo today.
