
OpenSearch RBAC
Introduction
According to IDC, the global datasphere is projected to grow from 33 zettabytes in 2018 to 175 zettabytes by 2025, indicating the explosive growth in data generation and usage. In today’s data-driven world, protecting sensitive information is paramount. As organizations increasingly rely on powerful search and analytics tools, the need for robust security measures becomes critical. Introducing OpenSearch RBAC, a new way to handle data security in distributed search systems.
This article delves into the world of OpenSearch and its implementation of Role-Based Access Control (RBAC). We’ll explore how this powerful combination enhances data security, simplifies access management, and ensures compliance with various regulatory requirements.
What is OpenSearch?
Before we dive into the specifics of RBAC, let’s briefly explore OpenSearch itself.
A Nutshell Overview
OpenSearch is an open-source, distributed search and analytics engine derived from Elasticsearch. We use OpenSearch to quickly ingest, search, and analyze vast amounts of data in near real-time. OpenSearch offers a wide range of features, including following:
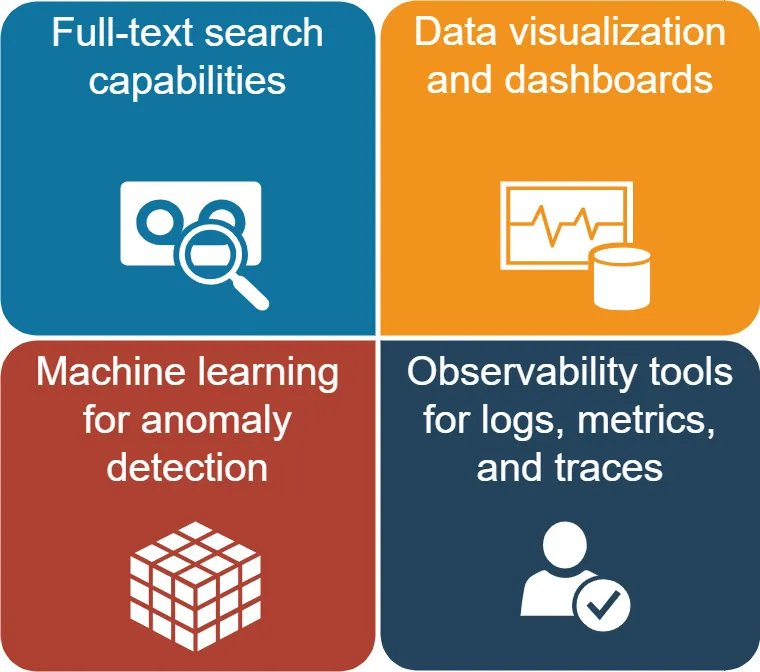
One of OpenSearch’s key strengths is its scalability and flexibility, making it suitable for a variety of use cases across different industries.
Understanding RBAC in OpenSearch
Role-Based Access Control (RBAC) determines which users can access specific resources on a computer or network. This concept concerns the user roles you assign to users within an organization. RBAC helps organizations manage and control access to sensitive information with different security roles.
It ensures that only authorized individuals can access certain data or systems. RBAC is a crucial security measure for protecting valuable assets within an organization. RBAC is a powerful tool for managing user permissions and securing data in OpenSearch.
Key Concepts of OpenSearch RBAC
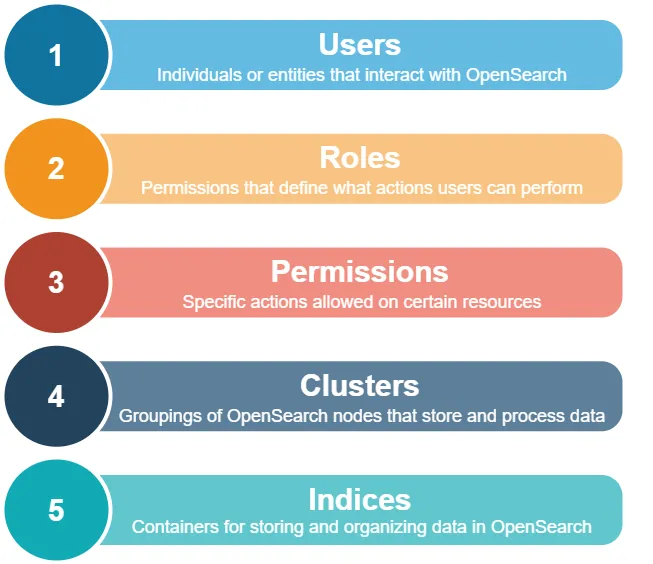
By combining these elements, OpenSearch RBAC allows administrators to create granular access policies that align with organizational needs and security requirements.
Implementing OpenSearch RBAC: A Step-by-Step Guide
Let’s walk through the process of setting up RBAC in OpenSearch, complete with examples and expected results.
Step 1: Enable Security Plugin
First, ensure that the OpenSearch Security plugin is installed and enabled. This plugin provides the foundation for RBAC functionality.
plugins.security.enabled: true
After enabling the plugin, restart your OpenSearch cluster to apply the changes.
Step 2: Define Roles
Create roles that align with your organization’s access requirements. Here’s an example of defining a “read_only” role:
PUT _plugins/_security/api/roles/read_only
{
"cluster_permissions": ["cluster:monitor/*"],
"index_permissions": [
{
"index_patterns": ["*"],
"allowed_actions": ["read"]
}
]
}This role grants cluster monitoring permissions and read-only access to all indices.
Step 3: Create Opensearch Users
Next, create users and assign them to appropriate roles. Here’s an example:
PUT _plugins/_security/api/internalusers/john_doe
{
"password": "secret_password",
"backend_roles": ["read_only"],
"attributes": {
"department": "IT"
}
}This command creates a user named “john_doe” with the “read_only” role.
Step 4: Map Roles to Users
To finalize the RBAC setup, map roles to users:
PUT _plugins/_security/api/rolesmapping/read_only
{
"backend_roles": ["read_only"],
"hosts": [],
"users": ["john_doe"]
}This mapping ensures that the “john_doe” user is associated with the “read_only” role.
Advanced OpenSearch RBAC Techniques
As your OpenSearch deployment grows, you may need more sophisticated access control strategies. Let’s explore some advanced RBAC techniques.
Multi-Tenant Data Isolation
In multi-tenant environments, it’s crucial to isolate data between different clients or departments. OpenSearch RBAC allows you to achieve this through index-level permissions.
Example:
PUT _plugins/_security/api/roles/finance_dept
{
"cluster_permissions": ["cluster:monitor/*"],
"index_permissions": [
{
"index_patterns": ["finance-*"],
"allowed_actions": ["crud"]
}
]
}This role grants full CRUD access to indices prefixed with “finance-“, effectively isolating finance department data.
Temporary Access Grants
For scenarios where temporary access is required, OpenSearch RBAC supports time-based restrictions.
Example:
PUT _plugins/_security/api/roles/temp_admin
{
"cluster_permissions": ["*"],
"index_permissions": [
{
"index_patterns": ["*"],
"allowed_actions": ["*"]
}
],
"expiry_date": "2023-12-31T23:59:59Z"
}This role grants full admin access but expires on December 31, 2023.
Best Practices for OpenSearch Access Control
To maximize the effectiveness of your OpenSearch RBAC implementation, consider these best practices:
- Least Privilege Principle: Grant users the minimum permissions necessary to perform their tasks.
- Regular Audits: Periodically review and update role assignments to ensure they remain appropriate.
- Use Groups: Leverage user groups to simplify role management for large organizations.
- Document Your Policies: Maintain clear documentation of your RBAC structure for easy reference and auditing.
- Encrypt Communications: Enable SSL/TLS encryption for all cluster communications to prevent eavesdropping.
Monitoring and Troubleshooting OpenSearch RBAC
Effective RBAC management requires ongoing monitoring and troubleshooting. OpenSearch provides several tools to help with this:
Audit Logging
Enable audit logging to track user actions and access attempts:
plugins.security.audit.type: internal_opensearch
plugins.security.audit.config.enabled: true
Security Analytics
Utilize OpenSearch Dashboards to visualize security events and identify potential issues:
- Create an index pattern for your audit logs
- Build dashboards to monitor login attempts, permission denials, and other security events
Compliance and OpenSearch RBAC
For many organizations, regulatory compliance is a critical concern. OpenSearch RBAC can help meet various compliance requirements:
- GDPR: Implement fine-grained access control to protect personal data
- HIPAA: Ensure that only authorized personnel can access protected health information
- PCI DSS: Restrict access to cardholder data and maintain audit trails
By leveraging OpenSearch RBAC, you can create a compliant environment that satisfies auditors and protects sensitive information. Note that DataSunrise can also help make this task much easier.
Future Trends in OpenSearch Security
As the data landscape evolves, so too will OpenSearch security features. Keep an eye on these emerging trends:
- AI-Powered Access Control: Machine learning algorithms may soon assist in identifying anomalous access patterns
- Blockchain Integration: Immutable audit trails could enhance security and compliance efforts
- Zero Trust Architecture: Expect tighter integration with zero trust security models
Conclusion
OpenSearch RBAC offers a powerful and flexible approach to securing your data and managing access control. By implementing role-based policies, organizations can protect sensitive information, simplify administration, and ensure compliance with regulatory requirements.
As data continues to grow in volume and importance, robust security measures like OpenSearch RBAC will become increasingly critical. By mastering these tools and staying informed about emerging trends, you can keep your data safe and your organization secure in an ever-changing digital landscape.
Note: For user-friendly and flexible tools designed to enhance database security and ensure compliance, consider exploring DataSunrise’s offerings. Visit our website at DataSunrise for an online demo and discover how we can help safeguard your valuable data assets.
