
PBAC in SQL Server: Implementation & Benefits of Usage

Policy-Based Access Control (PBAC) is a robust security model that allows organizations to enforce fine-grained access control based on policies defined in SQL Server. PBAC helps administrators create and manage access control policies to determine who can access data and perform actions. This article explores the concept of PBAC and provides a step-by-step guide on how to implement it in SQL Server.
Policy-Based Access Control in Details
PBAC is an access control model that relies on policies to govern access to data and resources. In SQL Server, administrators define policies using the built-in Policy-Based Management feature. Policies are rules that decide if a user or app can access or change data.
PBAC offers a flexible and centralized approach to access control. PBAC allows you to create rules that apply to multiple objects and databases. Instead of managing permissions for each table or view separately. Policies are based on various factors, such as user roles, application context, or data sensitivity.
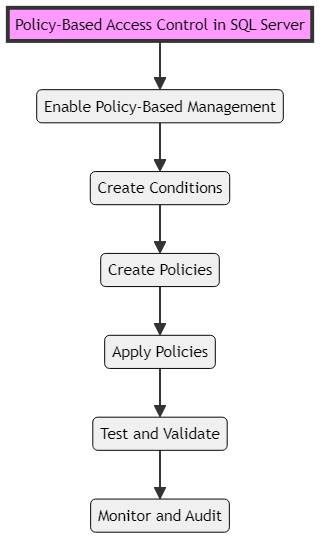
PBAC implementation order
Benefits of PBAC in SQL Server
Implementing PBAC in SQL Server provides several benefits for organizations looking to enhance their data security. PBAC allows administrators to set detailed rules for who can access certain data and do specific actions. This level of control helps prevent unauthorized access and ensures that users can only access the data they need to perform their tasks.
PBAC simplifies access control management by providing a centralized framework for defining and managing policies. Instead of managing permissions on individual objects, administrators can create policies that apply across multiple objects and databases. This centralized approach reduces administrative overhead and makes it easier to maintain a consistent security posture.
PBAC also promotes compliance with security regulations and standards. Organizations should create policies that meet legal and industry standards to ensure their data access practices comply with regulations. PBAC provides an auditable trail of access control decisions, making it easier to demonstrate compliance during audits.
Implementing PBAC in SQL Server
To implement PBAC in SQL Server, follow these steps:
Step 1: Enable Policy-Based Management
To use PBAC, you need to enable the Policy-Based Management feature in SQL Server. This feature is available in SQL Server Enterprise, Developer, and Evaluation editions. You can enable it by running the following command:
sp_configure 'show advanced options', 1; GO RECONFIGURE; GO sp_configure 'policy based management', 1; GO RECONFIGURE; GO
Step 2: Create Conditions
Conditions are the building blocks of policies in PBAC. They establish the criteria that policies must meet to be applicable. Conditions may be based on various factors, such as user roles, application context, or data sensitivity.
To create a condition, use the `CREATE CONDITION` statement. For example, to create a condition that checks if the current user is a member of the “SalesAdmin” role, you can use the following code:
CREATE CONDITION SalesAdminCondition AS @UserRole = 'SalesAdmin';
Step 3: Create Policies
Policies are the core components of PBAC. They define the access control rules that govern who can access specific data and perform certain actions. Policies have one or more conditions and outline the actions to take when those conditions are met. To create a policy, use the `CREATE POLICY` statement. For example, to create a policy that allows members of the “SalesAdmin” role to select data from the “Sales” table, you can use the following code:
CREATE POLICY SalesAdminPolicy AS GRANT SELECT ON Sales TO SalesAdminCondition;
Step 4: Apply Policies
Once you have created conditions and policies, you need to apply them to the relevant objects in your database. To apply a policy, use the `sp_syspolicy_add_object` stored procedure. For example, to apply the “SalesAdminPolicy” to the “Sales” table, you can use the following code:
EXEC sp_syspolicy_add_object 'SalesAdminPolicy', 'AdventureWorks2019.Sales.SalesOrderHeader';
Step 5: Test and Validate
After applying policies, it’s crucial to test and validate that the access control rules are working as intended. Test different scenarios and user roles to ensure that users can access the data they are authorized to access and are restricted from accessing data they shouldn’t.
You can verify that the policies are enforced correctly using SQL queries. For example, to test if a user with the “SalesAdmin” role can select data from the “Sales” table, you can execute a SELECT query while impersonating that user.
Step 6: Monitor and Audit
Regularly monitor and audit access control decisions to detect any unauthorized access attempts or policy violations. SQL Server provides auditing capabilities that allow you to track and log access control events.
You can configure SQL Server Audit to capture policy-related events, such as successful and failed access attempts. By analyzing the audit logs, you can identify potential security breaches and take appropriate actions.
Example of PBAC in SQL Server
Let’s consider an example to illustrate the implementation of PBAC in SQL Server. Suppose you have a database that contains sensitive customer information. You want to ensure that only authorized users from the “CustomerService” department can access and modify customer data.
First, create a condition that checks if the current user belongs to the “CustomerService” department:
CREATE CONDITION CustomerServiceCondition AS @Department = 'CustomerService';
Next, create a policy that grants SELECT, INSERT, UPDATE, and DELETE permissions on the “Customers” table to users who meet the “CustomerServiceCondition”:
CREATE POLICY CustomerServicePolicy AS GRANT SELECT, INSERT, UPDATE, DELETE ON Customers TO CustomerServiceCondition;
Apply the policy to the “Customers” table:
EXEC sp_syspolicy_add_object 'CustomerServicePolicy', 'AdventureWorks2019.Sales.Customer';
Now, only users from the “CustomerService” department will be able to access and modify data in the “Customers” table. Other users will be restricted based on the defined policy.
Conclusion
Policy-Based Access Control is a strong security model that helps organizations enforce detailed access control in SQL Server. By defining policies based on conditions and actions, administrators can centrally manage and control access to sensitive data.
To use PBAC in SQL Server, you need to first turn on Policy-Based Management. Then, create rules and apply them to objects. Next, test and check access rules to ensure they are working correctly. Finally, monitor access decisions to see if they are being enforced properly.
By adopting PBAC, organizations can enhance their data security posture, simplify access control management, and ensure compliance with security regulations and standards. PBAC provides a flexible and scalable approach to access control, making it suitable for organizations of various sizes and industries.
Remember to regularly review and update your PBAC policies to align with changing business requirements and security best practices. Continuously monitor and audit access control events to detect and respond to any potential security breaches.
With PBAC in place, you can have confidence in the security of your SQL Server environment, knowing that sensitive data is protected and accessible only to authorized users.
