
Phishing Attacks: The Most Dangerous Vulnerability

Phishing attacks have become a major concern for individuals and organizations alike. These malicious attempts aim to trick users into revealing sensitive information, such as login credentials or financial details. Phishing emails often masquerade as legitimate messages from trusted sources, making them difficult to detect. Understanding how these online scams work and implementing effective preventive measures are crucial for safeguarding your data and privacy.
What are Phishing Attacks?
Phishing attacks are a type of social engineering technique that relies on deception to steal user information. Attackers create fake emails, messages, or texts that look like they’re from trusted sources like banks, social media, or coworkers.
These messages create a sense of urgency, prompting people to act quickly or seek more information. As a result, they may click on a harmful link or download a virus. If someone falls for the trap, they could unintentionally share their private information. They may also give the attacker permission to access their computer.
Phishing attacks can take various forms, each designed to exploit different human emotions and behaviors. Some common types of phishing include:
- Spear Phishing: This targeted approach involves researching specific individuals or organizations to create highly personalized and convincing messages. Attackers can gather information from social media, company websites, or public records. They use this information to create emails that deceive people. These emails are more likely to trick individuals into taking actions that benefit the attackers.
- Whaling: Similar to spear phishing, whaling targets high-profile individuals, such as executives or senior management, within an organization. These attacks often involve urgent requests for sensitive information or wire transfers, exploiting the authority and trust associated with the targeted individual’s position.
- Clone Phishing is when attackers make a fake email that looks just like a real one the recipient got before. They replace any harmful links or attachments in the email. They send the email from a fake address. This makes it appear as though the original sender is resending the message.
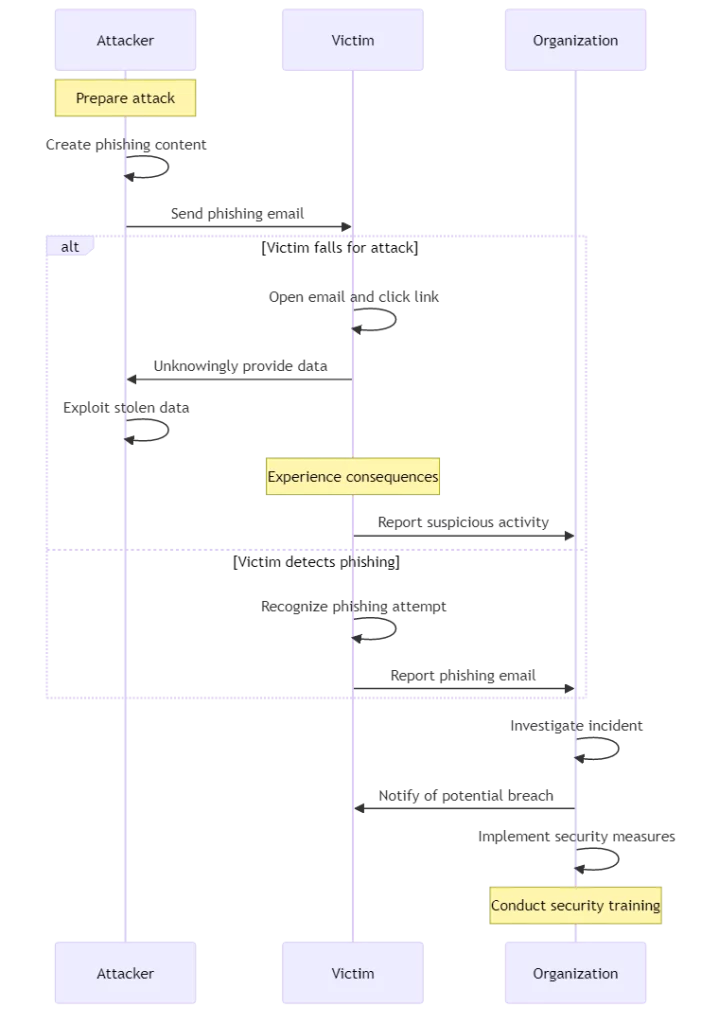
Phishing attack lifecycle
Common Phishing Email Tactics
Phishing emails employ various tactics to lure unsuspecting users into their traps. One common approach is to create a sense of urgency or fear.
A hacker might send you an email. The email may state that your account will be suspended. It might ask you to update your login details immediately.
Scammers trick people by offering rewards or discounts to get them to click on a link. This link takes them to a fake website where the scammers steal their information. Phishing emails may also mimic the branding and design of legitimate companies, making them appear authentic at first glance.
Attackers often exploit current events or popular topics to make their phishing emails more convincing. During tax season, scammers may send emails pretending to be from the IRS. They ask for personal information or threaten legal action.
On days with many sales, such as Black Friday and Cyber Monday, people may receive emails that offer great deals. These emails are actually trying to trick people into clicking on dangerous links.
Identifying Phishing Emails
To protect yourself from falling victim to email phishing, it’s essential to learn how to spot suspicious messages. Be wary of emails that contain generic greetings, such as “Dear valued customer,” instead of addressing you by name. Check the sender’s email address carefully, as attackers often use slightly altered domain names to deceive recipients.
Look out for spelling and grammatical errors, as legitimate organizations typically ensure their communications are error-free. Also, hover over links in the email to check for any unexpected or suspicious URLs.
Other red flags to watch out for include:
- Unsolicited Attachments: Be careful with emails from people you don’t know that have attachments. Don’t enable macros or give permissions. These attachments may contain malware that can infect your system.
- Inconsistent Messaging: If an email’s subject line, content, and linked URL seem inconsistent or unrelated, it may be a phishing attempt. Legitimate companies ensure that their communications are coherent and relevant.
- Pressure Tactics: Phishing emails often try to pressure you into acting quickly by creating a false sense of urgency. Be suspicious of messages that demand immediate action or threaten consequences for not complying.
- Unusual Requests: If an email asks for private information like your social security number or bank details, it could be a scam. Be cautious and avoid sharing sensitive information over email. Legitimate organizations have secure channels for handling such information.
The Consequences of Falling for Phishing Attacks
Falling for a phishing attack can have severe consequences for both individuals and organizations. Personally, you could lose access to your online accounts, have your identity stolen, or experience financial losses.
Attackers may use your compromised credentials to make unauthorized purchases or transfer funds from your bank accounts. Someone may use your personal information to open new accounts or lines of credit in your name. This can negatively impact your credit score and financial reputation.
Phishing attacks can harm businesses by exposing customer data and hurting their reputation. The financial impact of such incidents can be substantial, including costs associated with investigation, remediation, and potential legal liabilities. In addition, a data breach can erode customer trust and loyalty, leading to lost business and reduced market share.
Preventive Measures against Phishing Attacks
To avoid falling for phishing scams, it’s important to use multiple security measures. Begin by learning about the signs of phishing emails and reminding your employees to be careful with suspicious messages. Conduct regular training sessions to keep everyone informed about the latest phishing techniques and best practices for avoiding them.
Implement strong password policies, requiring the use of unique, complex passwords for each account. Encourage the use of password managers to help generate and securely store strong passwords. Enable two-factor authentication (2FA) whenever possible, adding an extra layer of security beyond just passwords.
2FA stands for two-factor authentication. This means you must provide a second form of identity verification. This could be a code sent to your phone. This is in addition to entering your password.
Regularly update your software and operating systems to patch any known vulnerabilities that attackers might exploit. Install reliable antivirus software and keep it up to date to detect and block potential threats. Consider implementing email filters that can identify and quarantine suspicious messages before they reach your inbox.
Responding to a Phishing Attack
If you suspect that you’ve fallen for a phishing attack, swift action is essential to minimize the damage. Change the passwords for any accounts that hackers have accessed. Notify the appropriate authorities, such as your bank or the IT department at work.
Make sure to use the latest antivirus software to scan your system for malware and remove any threats. If you have shared sensitive financial information, contact your bank and credit card companies immediately. Inform them about the potential fraud and request new cards if necessary.
If your organization is attacked by phishing, it’s crucial to have a plan in place to respond effectively. This plan outlines steps to take in case of a security breach. It includes determining the extent of the attack, minimizing the impact, and communicating with those impacted. A thorough investigation can help determine the cause of the attack.
Conclusion
Phishing attacks pose a significant threat to individuals and organizations in the digital age. To avoid online scams, learn how they work and take steps to prevent them. This will help lower your chances of becoming a victim.
Stay vigilant, educate yourself and others, and maintain a proactive approach to cybersecurity. Remember, prevention is always better than cure when safeguarding your sensitive information from phishing attempts.
To prevent phishing attacks, ensure you have strong security measures in place. This includes regular training, strong authentication, and timely updates. Stay informed about the latest threats and best practices, and foster a culture of security awareness within your organization. Together, we can work towards a safer digital environment where phishing attacks are less likely to succeed.
