
PostgreSQL Data Audit Trail

Introduction
PostgreSQL, a powerful open-source relational database management system, is widely used across various industries. However, with great power comes great responsibility. Organizations need to create strong data audit trails. These trails help track user activities and monitor data access. They also ensure compliance with regulations like HIPAA and GDPR.
Remarkably, over two-thirds (68%) of data breaches worldwide stem from non-malicious human actions. The high percentage of breaches caused by non-malicious human actions emphasizes the need for comprehensive audit trails. By maintaining detailed logs of user activities, organizations can identify patterns of unintentional misuse or errors that lead to security incidents. This information is crucial for improving training programs and security protocols.
Understanding PostgreSQL Data Audit Trails
What is a PostgreSQL Data Audit Trail?
A PostgreSQL data audit trail is a chronological record of database activities. It captures user logins, queries, modifications, and even errors. This trail serves as a crucial tool for security monitoring, compliance, and forensic analysis.
Why are Audit Trails Important?
Audit trails play a vital role in:
- Detecting unauthorized access
- Tracking data changes
- Investigating security incidents
- Ensuring regulatory compliance
- Optimizing database performance
Privacy Risks in PostgreSQL
When users connect to PostgreSQL, they face several privacy risks that can compromise data security and integrity. These risks stem from various sources, including internal misuse, external attacks, and system vulnerabilities.
Understanding these risks is crucial for implementing effective security measures and maintaining a robust audit trail. Let’s explore some of the most significant privacy risks in PostgreSQL environments.
Unauthorized Data Access
Without proper auditing, malicious actors might access sensitive data undetected, potentially leading to severe data breaches. This risk is particularly high when user privileges are not regularly reviewed and updated. Unauthorized access can occur through various means, such as exploiting system vulnerabilities, using stolen credentials, or taking advantage of misconfigured permissions. Implementing comprehensive audit trails helps detect and deter such unauthorized access attempts.
Data Manipulation
Users with high-level access could change or remove important information without a trace if proper checks are not in place. This risk is especially concerning in environments where data integrity is crucial, such as financial or healthcare systems. Malicious data manipulation can lead to financial fraud, incorrect decision-making, or compliance violations. Regular auditing of data changes and strict version control can help mitigate this risk.
Credential Theft
Weak authentication mechanisms may lead to compromised user accounts, exposing the entire database to potential breaches. Attackers can exploit weak passwords, reused credentials, or social engineering tactics to gain unauthorized access.
Once someone compromises a user account, the attacker can potentially escalate privileges and access sensitive data. Using strong authentication methods, like multi-factor authentication and regular password changes, can greatly lower this risk. Regularly checking login attempts is also important.
SQL Injection Attacks
Poorly constructed queries can expose the database to malicious code injection, potentially allowing attackers to execute unauthorized commands. SQL injection attacks can lead to data theft, unauthorized data modifications, or even complete system compromise. These attacks often exploit inadequate input validation in application code or stored procedures. Implementing proper input sanitization, using parameterized queries, and regularly auditing database queries can help detect and prevent SQL injection attempts.
Native PostgreSQL Audit Tools
PostgreSQL offers several built-in features for creating audit trails:
PGAudit Extension
PGAudit is a powerful extension that provides detailed logging of database activities. It can record:
- Session start and stop times
- SQL statements executed
- Object access and modifications
To enable PGAudit, install the extension and configure it in postgresql.conf:
shared_preload_libraries = 'pgaudit' pgaudit.log = 'write, function, role, ddl'
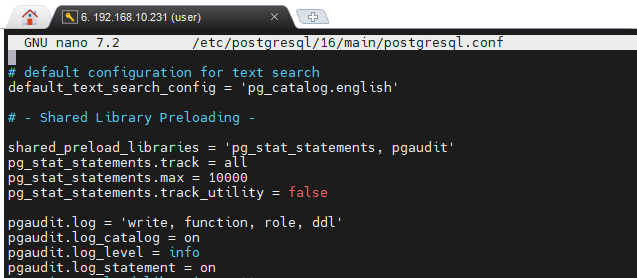
The image above shows two PostgreSQL extensions that have been configured: pgAudit and pg_stat_statements. These extensions enhance the database’s auditing capabilities and query performance analysis, respectively.
Cumulative Statistics
PostgreSQL’s statistics collector gathers valuable information about database activities. Enable it by setting:
track_activities = on track_counts = on
This feature helps in monitoring overall database performance and usage patterns.
Error Logging
Configure PostgreSQL to log errors and warnings:
log_min_messages = warning log_min_error_statement = error
These settings ensure that critical issues are recorded for further investigation.
Auditing Sessions by Applications
To enhance security, consider implementing application-level auditing:
Connection Pooling
Use connection pooling tools like PgBouncer to manage and monitor database connections efficiently.
Middleware Logging
Implement logging mechanisms in your application’s middleware to capture user actions before they reach the database.
Stored Procedures
Utilize stored procedures to encapsulate and log complex database operations.
Third-Party Audit Solutions
While native tools are valuable, dedicated third-party software can provide more comprehensive auditing capabilities:
Enhanced Security Features
Third-party solutions often offer advanced encryption, access controls, and real-time alerting.
Compliance Reporting
Generate pre-configured reports to meet HIPAA, GDPR, and other regulatory requirements.
Centralized Management
Manage audit trails across multiple databases from a single interface.
Performance Optimization
Advanced auditing tools minimize the performance impact on your production databases.
Best Practices for PostgreSQL Audit Trails
To maximize the effectiveness of your audit strategy:
- Define clear audit policies
- Regularly review and analyze audit logs
- Implement least privilege access
- Encrypt sensitive audit data
- Establish retention policies for audit trails
- Conduct periodic security assessments
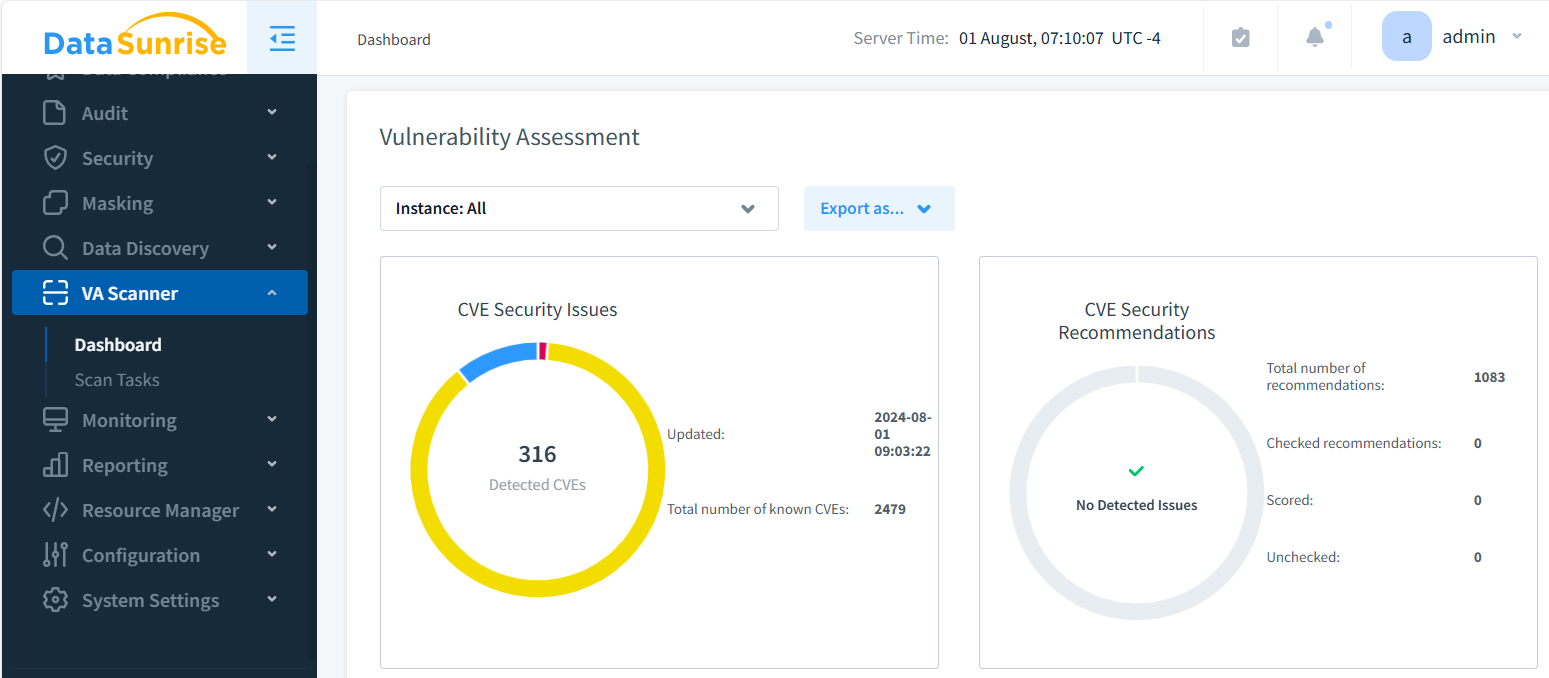
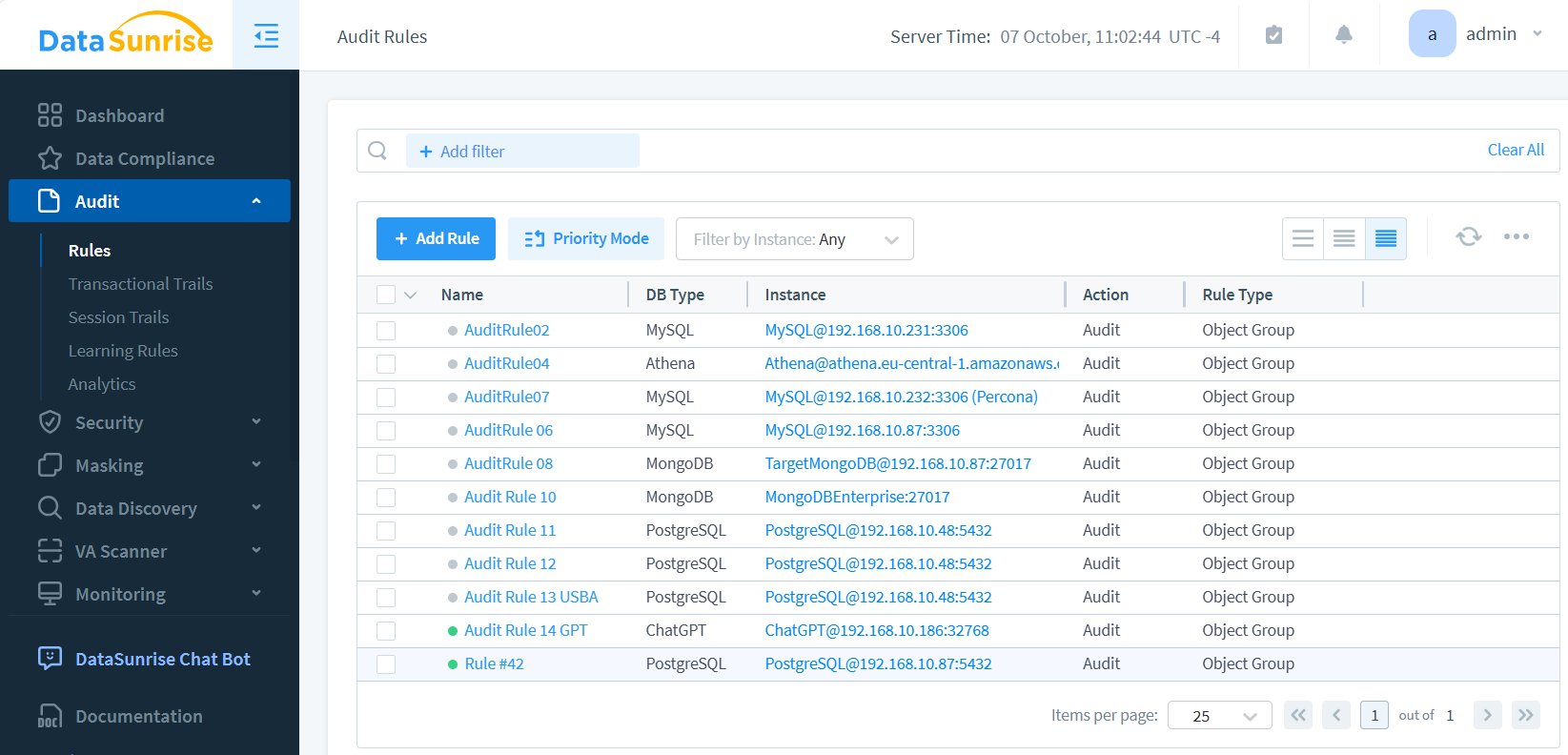
DataSunrise offers powerful audit functionality for PostgreSQL, allowing users to quickly set up and implement audit rules. The process is straightforward:
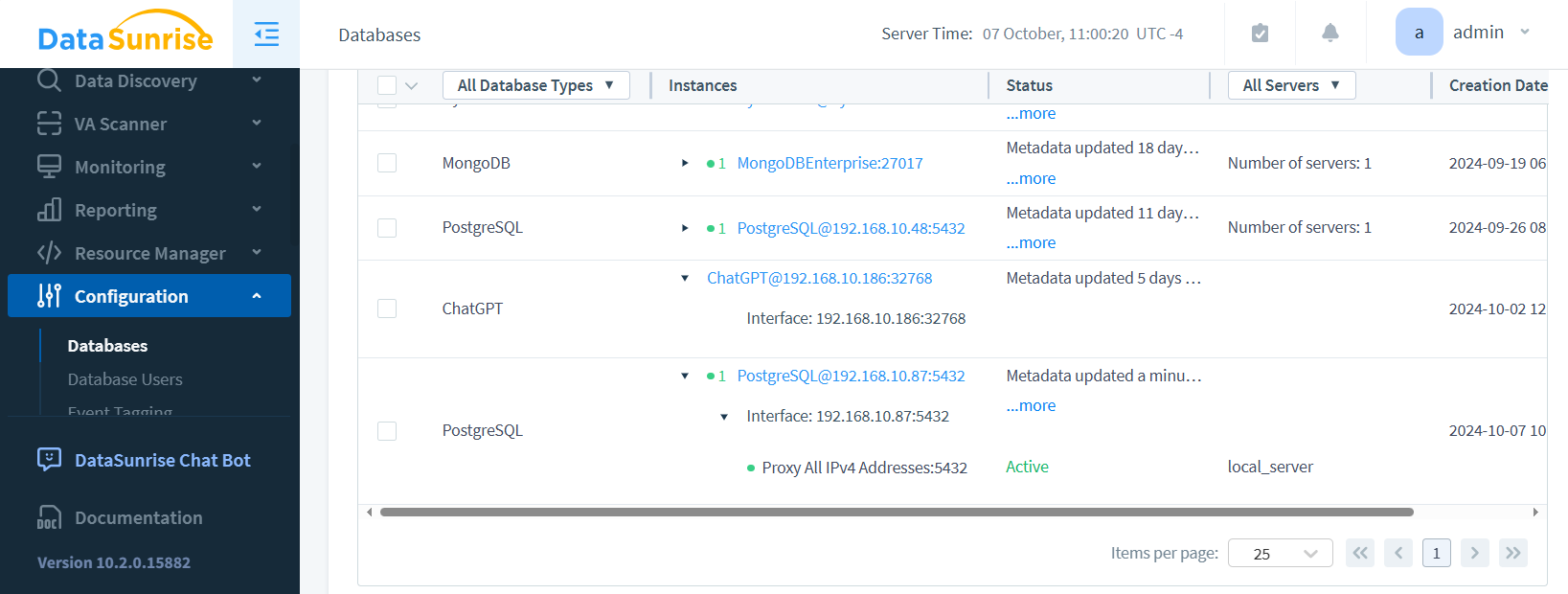
Create an Instance: Set up your PostgreSQL database connection in DataSunrise.
Configure Audit Rules: Easily create audit rules and select specific database objects to monitor.
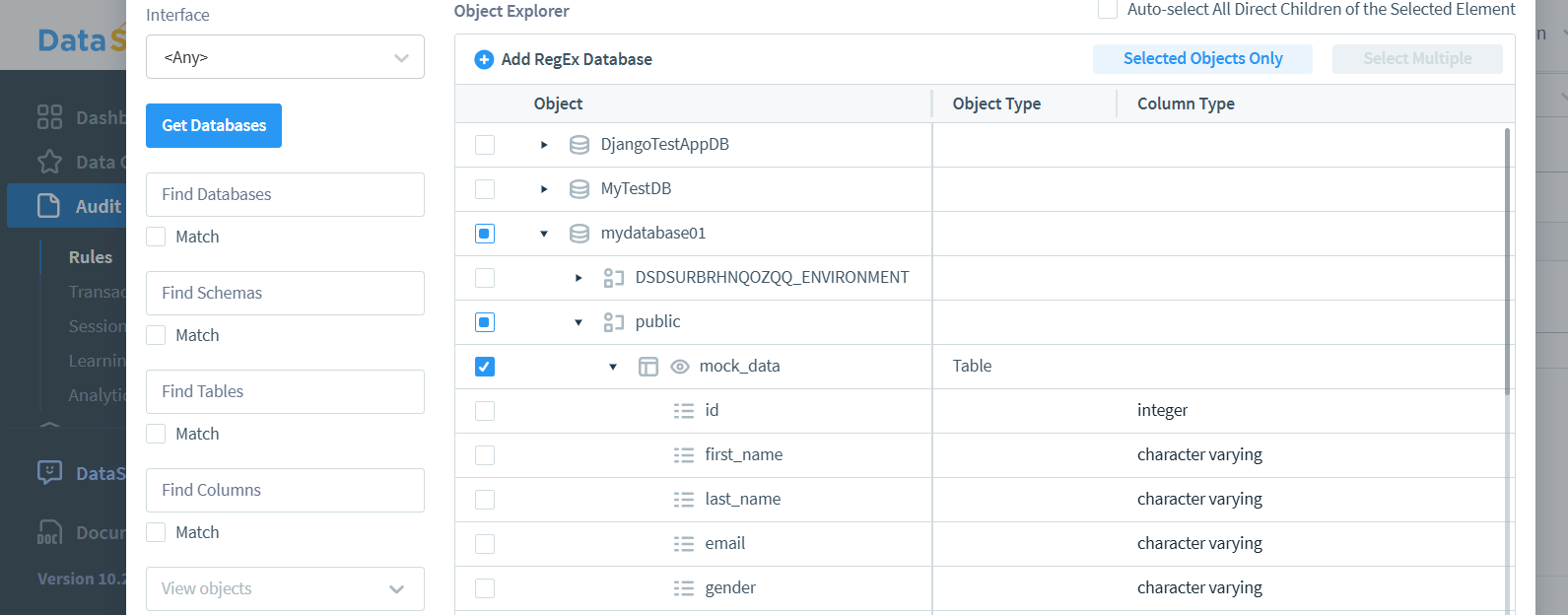
Generate Audit Trails: Simply make requests through the DataSunrise proxy to automatically produce detailed database transactional trails.
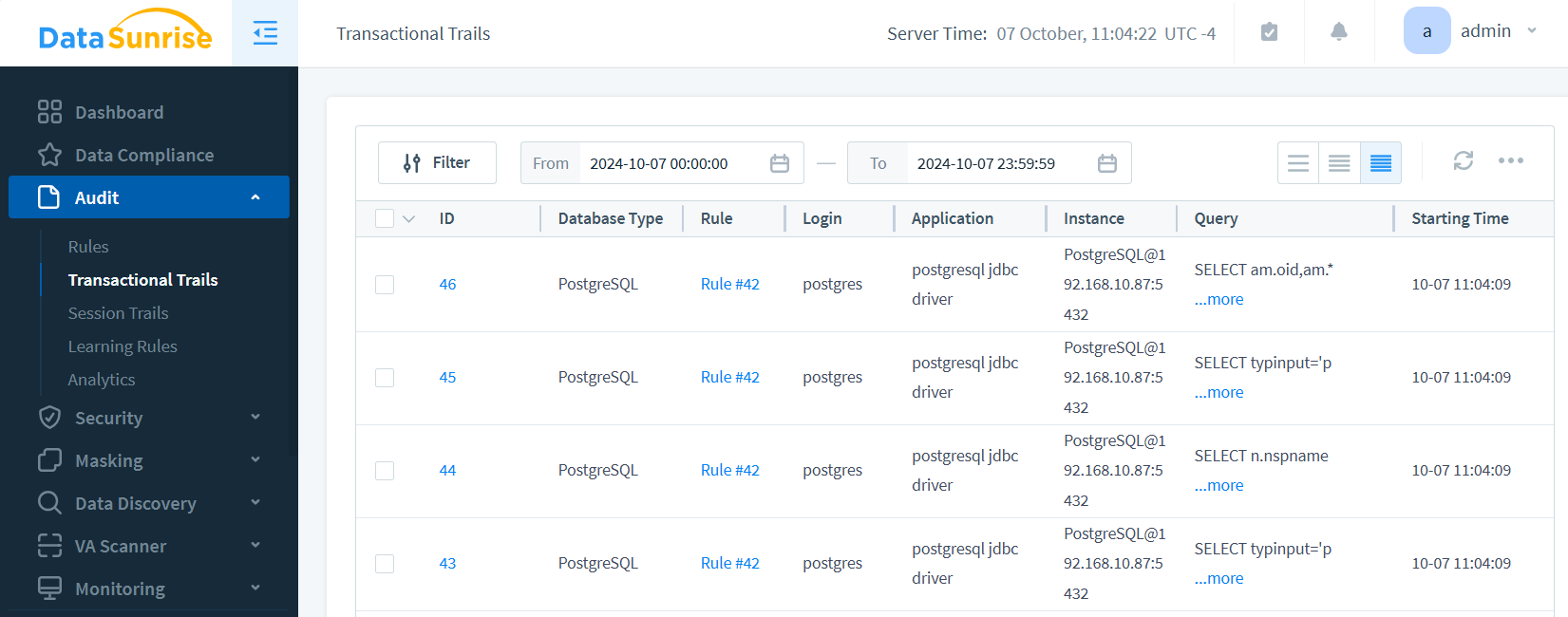
This user-friendly approach ensures that organizations can rapidly deploy robust auditing measures, enhancing their PostgreSQL database security with minimal effort. By leveraging DataSunrise’s intuitive interface and powerful features, businesses can effortlessly comply with regulations and maintain comprehensive visibility into their database activities.
Compliance with HIPAA and GDPR
Maintaining a robust PostgreSQL data audit trail is crucial for compliance with regulations like HIPAA and GDPR:
HIPAA Compliance
HIPAA requires healthcare organizations to:
- Track access to protected health information (PHI)
- Detect unauthorized data modifications
- Maintain audit logs for at least six years
GDPR Compliance
GDPR mandates that organizations:
- Demonstrate data processing accountability
- Provide audit trails for data subject access requests
- Implement appropriate security measures
Conclusion
Implementing a comprehensive PostgreSQL data audit trail is essential for maintaining database security, ensuring regulatory compliance, and protecting sensitive information. By using native PostgreSQL tools, application-level auditing, and third-party solutions, organizations can build strong defenses. This helps protect against internal and external threats.
A good audit trail helps find and stop security breaches. It also gives useful information about how the database is used and ways to improve its performance.
DataSunrise: Advanced PostgreSQL Auditing Solution
DataSunrise offers cutting-edge PostgreSQL audit capabilities that go beyond native tools. Using proxy technology, DataSunrise provides comprehensive session auditing with its advanced components. This powerful solution enables organizations to:
- Monitor real-time database activity
- Generate detailed compliance reports
- Detect and prevent SQL injection attacks
- Mask sensitive data in audit logs
DataSunrise’s flexible and innovative tools for database security include activity monitoring and vulnerability assessment, among other features. To see the full potential of DataSunrise’s PostgreSQL auditing features, visit our website. You can watch an online demo and learn how we can improve your database security.
