
Enhancing Data Security with Redshift Encryption

Amazon Redshift is a powerful data warehouse solution offered by AWS. As businesses store sensitive information in Redshift, ensuring data security becomes crucial. Redshift encryption plays a vital role in protecting your valuable data from unauthorized access. This article will discuss Redshift encryption, explaining how to protect your data and follow security rules.
What is Redshift Encryption?
Redshift encryption is a security feature that protects your data both at rest and in transit. It uses advanced encryption algorithms to scramble your information, making it unreadable to anyone without the proper decryption keys. Redshift offers two main types of encryption: server-side and client-side. Each type has its own benefits and use cases, allowing you to choose the best option for your security needs.
Server-Side Encryption in Redshift
Server-side encryption happens automatically on the AWS side. When you enable this feature, Redshift encrypts your data before saving it to disk in their data centers.
The data remains encrypted until you request to access it. Redshift decrypts the information and sends it to you. This process happens seamlessly, requiring minimal effort from your end.
For example, imagine you’re storing customer purchase history in Redshift. When you enable server-side encryption, AWS data centers store this sensitive data encrypted. Redshift decrypts data as you analyze it, ensuring secure access to information for your work.
Client-Side Encryption for Redshift
Client-side encryption puts you in control of the encryption process. You encrypt your data before uploading it to Redshift. This approach requires more effort on your part, as you need to manage the encryption process, keys, and any related tools. It provides an extra layer of security by encrypting your data before it even leaves your systems.
Consider a scenario where you’re handling highly sensitive financial data. You might choose to encrypt this data using your own encryption tools before sending it to Redshift. This ensures that even if someone intercepts the data during transmission, they won’t be able to read it without your encryption keys.
Redshift Cluster Encryption
Redshift organizes data into clusters, which are groups of computing resources. Enabling encryption for entire clusters ensures that it protects all databases within that cluster. When you enable cluster encryption, Redshift uses a four-tier key architecture to secure your data.
This architecture includes:
- Data encryption keys for each data block
- Database keys that encrypt the block encryption keys
- Cluster keys that encrypt the database keys
- A master key that oversees the entire process
For instance, if you have a cluster containing customer data, product information, and sales records, enabling cluster encryption would protect all of this data under the same encryption umbrella.
Redshift Database Encryption
Within a cluster, you can have multiple databases. Redshift allows you to enable encryption on individual databases when creating a new cluster. This process uses keys provided by Amazon Key Management Service (KMS). You can choose between customer-managed keys (CMK) or AWS-managed keys.
Let’s say you’re setting up a new Redshift cluster for your e-commerce platform. You might create separate databases for user profiles, product catalogs, and order history. Enabling database encryption ensures that each of these databases is individually protected, even within the same cluster.
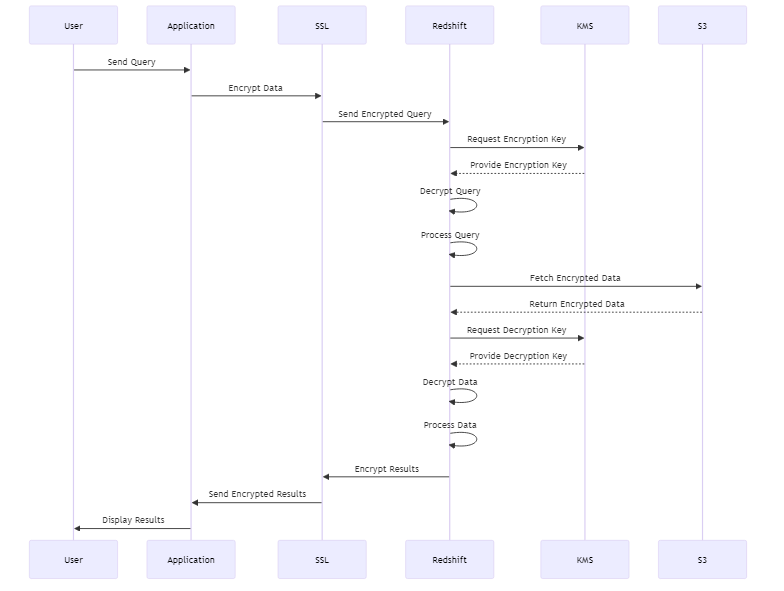
Encryption for Data in Transit
Redshift actively protects your data while storing it. It also ensures the safety of your data when transferring it between your applications and the Redshift servers. This is called encryption in transit. Redshift enables SSL (Secure Sockets Layer) connections for JDBC and ODBC, ensuring that it encrypts data during transmission.
When your analytics team looks at data in Redshift, the request and data encrypt as they move through the network. This prevents eavesdroppers from intercepting and reading the information.
Changing Encryption Settings
As your security needs evolve, you might need to change your Redshift encryption settings. AWS allows you to modify encryption settings for existing clusters. You can add encryption to unencrypted clusters or change the type of encryption key you’re using.
Imagine you started with an unencrypted Redshift cluster for a small project. As the project grows and begins handling more sensitive data, you decide to enable encryption. You can do this through the AWS console or command-line interface, and Redshift will migrate your data to a new, encrypted cluster.
Examples for Redshift Encryption
To better understand how Redshift encryption works in practice, let’s look at some SQL code examples:
Creating an encrypted table:
CREATE TABLE sensitive_customer_data ( customer_id INT, name VARCHAR(100), email VARCHAR(100), credit_card VARCHAR(255) ) ENCRYPTED;
Inserting encrypted data using AES encryption:
INSERT INTO sensitive_customer_data (customer_id, name, email, credit_card)
VALUES (
1,
'John Doe',
'john@example.com',
AES_ENCRYPT('1234-5678-9012-3456', 'my_encryption_key')
);
Creating a view with column-level encryption:
CREATE VIEW secure_customer_view AS SELECT customer_id, name, email, AES_ENCRYPT(credit_card, 'view_encryption_key') AS encrypted_credit_card FROM sensitive_customer_data;
Querying encrypted data:
SELECT customer_id, name, email, AES_DECRYPT(encrypted_credit_card, 'view_encryption_key') AS decrypted_credit_card FROM secure_customer_view;
Enabling cluster encryption:
ALTER CLUSTER my_redshift_cluster ENCRYPTED WITH KMS_KEY_ID 'arn:aws:kms:region:account-id:key/key-id';
Creating an encrypted database:
CREATE DATABASE encrypted_db ENCRYPTED WITH KMS_KEY_ID 'arn:aws:kms:region:account-id:key/key-id';
Rotating encryption keys:
ALTER TABLE sensitive_customer_data ROTATE ENCRYPTION KEY;
These examples demonstrate various aspects of Redshift encryption, including table-level encryption, column-level encryption using AES functions, cluster and database encryption, and key rotation.
Remember that in a real-world scenario, you would use more secure methods for managing encryption keys, such as AWS Key Management Service, rather than hardcoding them in SQL statements.
By incorporating these encryption techniques into your Redshift data management practices, you can significantly enhance the security of your sensitive data, protecting it from unauthorized access both at rest and in transit.
Best Practices for Redshift Encryption
To make the most of Redshift encryption, consider these best practices:
- Always encrypt sensitive data, both at rest and in transit.
- Use strong, unique keys for each cluster or database.
- Regularly rotate your encryption keys to enhance security.
- Monitor and audit your encryption settings and key usage.
- Train your team on proper encryption practices and key management.
For instance, you might set up a quarterly key rotation schedule for your Redshift clusters. This ensures that even if a key is compromised, it limits the window of vulnerability.
Conclusion
Redshift encryption is a powerful tool for protecting your valuable data. By understanding and implementing the various encryption options available, you can significantly enhance your data security posture.
Select encryption and security measures for your Redshift environment. You can implement these measures on the server-side or client-side. You can also apply them at the cluster-level or database-level. This will help ensure consistent protection for your data.
Remember, data security is an ongoing process. Regularly review and update your encryption strategies to stay ahead of potential threats. You can use Redshift encryption to securely store and analyze your data. Strong security measures will give you confidence in protecting your data.
