Regulatory Compliance for MySQL: Enhanced Database Security
Introduction
Regulatory compliance is essential for businesses handling sensitive data. MySQL, as a widely used database management system, offers various native tools to help organizations meet compliance requirements. Auditing, data masking, and access controls are crucial elements in ensuring MySQL native regulatory compliance.
This article explores how MySQL’s SQL language features, views, and stored procedures help maintain compliance, along with an introduction to DataSunrise for centralized data control. For additional MySQL documentation, visit the official MySQL documentation.
Native Data Auditing in MySQL
MySQL Audit Capabilities
MySQL Community Edition does not include built-in auditing or masking capabilities. However, organizations can still implement basic auditing and static data masking techniques using SQL features like triggers, stored procedures, and manual data obfuscation.
Setting Up MySQL Using Docker
To set up a MySQL Community Edition 8.4 instance using Docker, follow these steps:
Step 1: Pull the MySQL Community Edition Image
docker login container-registry.oracle.com
After logging in, pull the MySQL 8.4 image:
docker pull container-registry.oracle.com/mysql/community-server:8.4
Step 2: Run a MySQL Container
docker run --name mysql_container -e MYSQL_ROOT_PASSWORD=rootpass -d -p 3306:3306 container-registry.oracle.com/mysql/community-server:8.4
Step 3: Connect to the MySQL Instance
Once the container is running, connect to MySQL:
docker exec -it mysql_container mysql -u root -p
Enter the root password when prompted.
Implementing Basic Auditing in MySQL
Since MySQL Community Edition lacks built-in auditing, we can create a simple audit log using a custom table.
Step 1: Creating an Audit Log Table
CREATE TABLE audit_log (
audit_id INT AUTO_INCREMENT PRIMARY KEY,
action_type VARCHAR(50),
table_name VARCHAR(50),
affected_row_id INT,
changed_data TEXT,
timestamp TIMESTAMP DEFAULT CURRENT_TIMESTAMP
);
Step 2: Implementing an Audit Trigger
DELIMITER $$
CREATE TRIGGER log_customer_updates
BEFORE UPDATE ON customers
FOR EACH ROW
BEGIN
INSERT INTO audit_log (action_type, table_name, affected_row_id, changed_data)
VALUES ('UPDATE', 'customers', OLD.id, CONCAT('Old Email: ', OLD.email, ', New Email: ', NEW.email));
END$$
DELIMITER ;Implementing Static Data Masking in MySQL
Since MySQL Community Edition does not provide dynamic data masking, organizations can implement static masking by creating a masked version of sensitive data.
Step 1: Creating a Masked Copy of Sensitive Data
CREATE TABLE customers_masked AS
SELECT id,
name,
CONCAT(LEFT(email, 3), '***@***.com') AS masked_email,
phone,
'XXXX-XXXX-XXXX' AS masked_credit_card
FROM customers;Step 2: Enforcing Access Control to the Masked Table
REVOKE SELECT ON customers FROM public;
GRANT SELECT ON customers_masked TO reporting_role;By revoking access to the original table and granting access only to the masked version, unauthorized users can only see obfuscated data.
Here’s the snippet of masked data users will see:
| id | name | masked_email | phone | masked_credit_card |
|---|---|---|---|---|
| 1 | Alice Johnson | ali***@***.com | 123-456-7890 | XXXX-XXXX-XXXX |
| 2 | Bob Smith | bob***@***.com | 234-567-8901 | XXXX-XXXX-XXXX |
| 3 | Charlie Brown | cha***@***.com | 345-678-9012 | XXXX-XXXX-XXXX |
| 4 | Diana Prince | dia***@***.com | 456-789-0123 | XXXX-XXXX-XXXX |
Regularly backing up data ensures traceability and compliance with regulatory policies.
Using DataSunrise for MySQL Compliance
DataSunrise offers an advanced security suite that includes data masking, access control, and audit logging. It provides an extra layer of compliance beyond MySQL’s native capabilities.
Setting Up a DataSunrise Instance
Assuming DataSunrise is installed, follow these steps to create an instance:
1. Log into DataSunrise’s web interface.
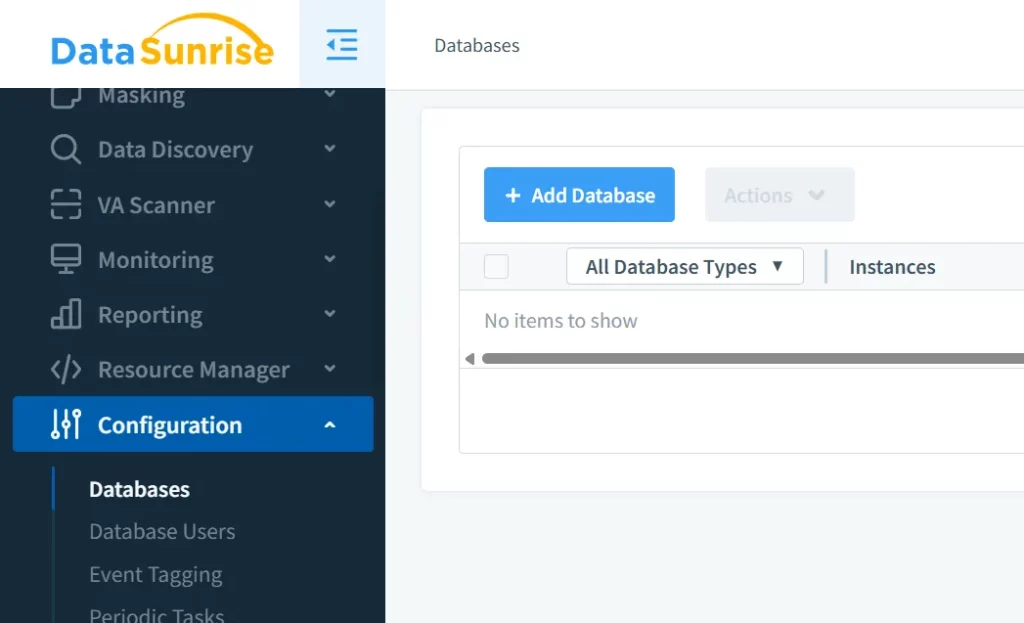
2. Navigate to Configuration, then Databases, and click Add Database.
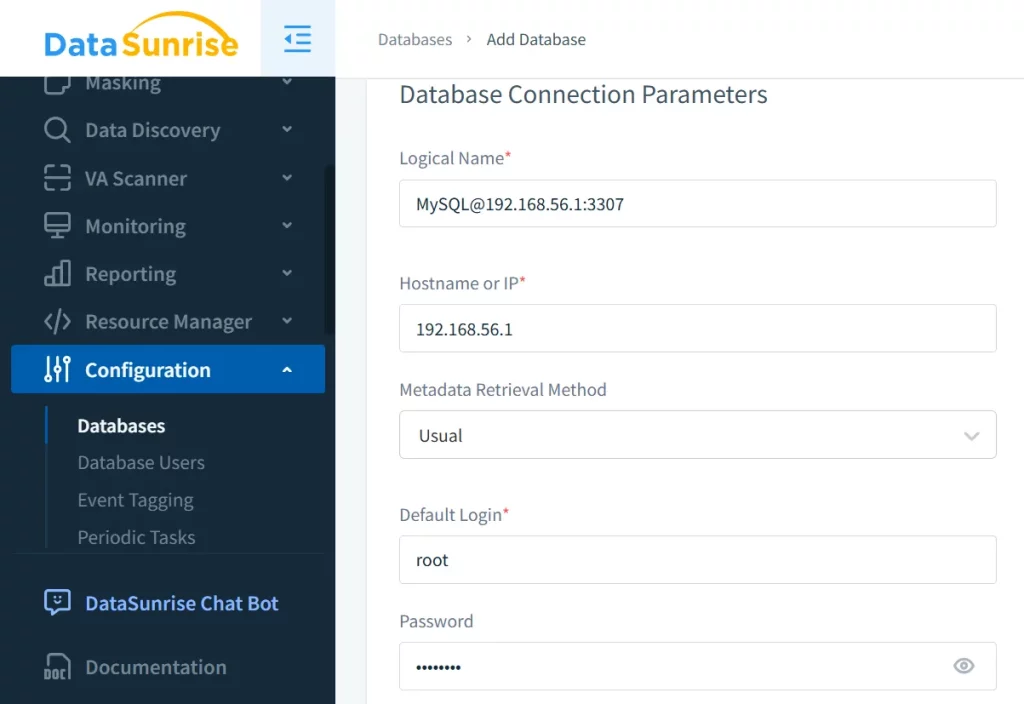
3. Configure the MySQL connection settings and save.
Viewing Dynamically Masked Data
Once configured, you can apply dynamic masking to sensitive data. For instance, a masking rule can hide customer emails:
This ensures that only authorized users can see the full data, helping with data governance for MySQL.
Benefits of DataSunrise’s Security Suite
DataSunrise offers centralized control over data security policies, ensuring:
- Uniform enforcement of masking rules.
- Real-time monitoring and audit logs.
- Compliance with regulatory frameworks like GDPR and HIPAA.
Conclusion
MySQL provides native tools for regulatory compliance, including audit trails and triggers. However, for enhanced security and centralized control, DataSunrise is an excellent choice. It simplifies MySQL native regulatory compliance with its advanced audit trail and masking features.
Experience DataSunrise’s powerful capabilities directly. Book a personalized demo to see how it transforms your data security workflow, or download a trial to explore the platform hands-on.
