
Protecting Sensitive Information with Static Data Masking in SQL Server

SQL Server databases contain valuable information for businesses. However, this data often includes sensitive details that need protection. Static data masking in SQL Server offers a robust solution to safeguard confidential information while maintaining database functionality. This article explores static data masking, its importance for SQL Server, and how to implement it effectively.
What is Static Data Masking?
Static data masking is a technique that permanently replaces sensitive information with fictitious yet realistic data. It creates a sanitized copy of the database, preserving its structure and usefulness while protecting confidential details. In SQL Server, static data masking ensures that unauthorized users cannot access or view sensitive information, even if they gain access to the masked database copy.
SQL Server databases often store personal information, financial records, and other sensitive data. Without proper protection, this information becomes vulnerable to breaches and unauthorized access. Static data masking in SQL Server addresses these security concerns by permanently obscuring sensitive details in the copied database.
Many industries face strict regulations regarding data protection. SQL Server static data masking helps organizations comply with laws like GDPR, HIPAA, and PCI DSS. By implementing masking techniques, companies demonstrate their commitment to data privacy and avoid potential legal issues.
Software development and testing require realistic data. However, using production data in these environments poses significant risks. Static data masking for SQL Server allows teams to work with safe, masked versions of databases. This approach maintains data integrity while eliminating the danger of exposing sensitive information during development and testing processes.
Implementing Static Data Masking in SQL Server
SQL Server offers various masking techniques to suit different data types and security requirements. Some popular methods include substitution (replace sensitive values with realistic alternatives), shuffling (rearrange existing data within a column), encryption (convert sensitive data into an unreadable format), and nulling (replace sensitive values with NULL).
Once you’ve identified sensitive data and chosen appropriate techniques, it’s time to create masking rules. In SQL Server, you can use built-in functions or custom scripts to apply these rules. For example, to mask a Social Security number column:
UPDATE Employees
SET SSN = CONCAT(
REPLICATE('X', 3),
'-',
REPLICATE('X', 2),
'-',
RIGHT(SSN, 4)
)
This rule would change SSNs from “123-45-6789” to “XXX-XX-6789,” revealing only the last four digits.
After defining masking rules, create a copy of the source database and apply the rules to this new copy. This step ensures that the original data remains intact while creating a fully masked version for use in non-production environments.
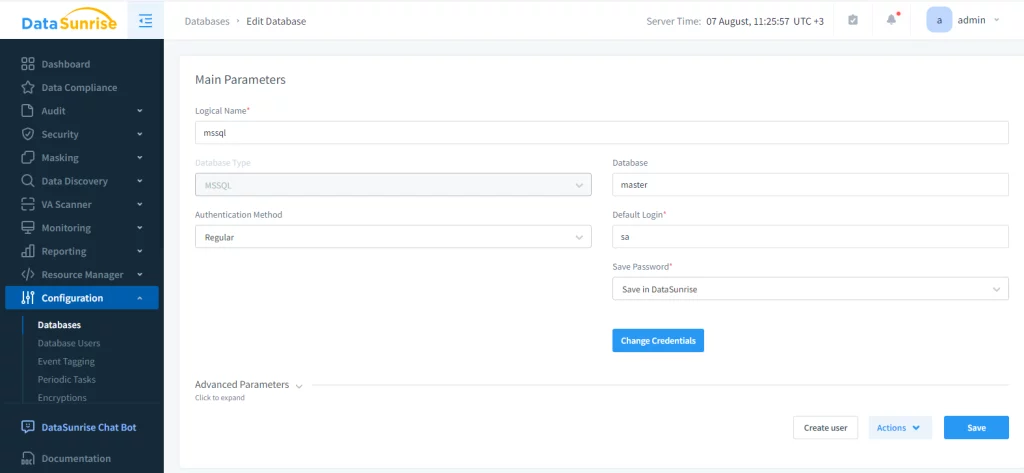
Using such methods may be tedious for an inexperienced user and might be extremely time-consuming for large databases. DataSunrise greatly simplifies the process of static masking. Firstly, a user must create an instance of MSSQL database to create rules and tasks for it.
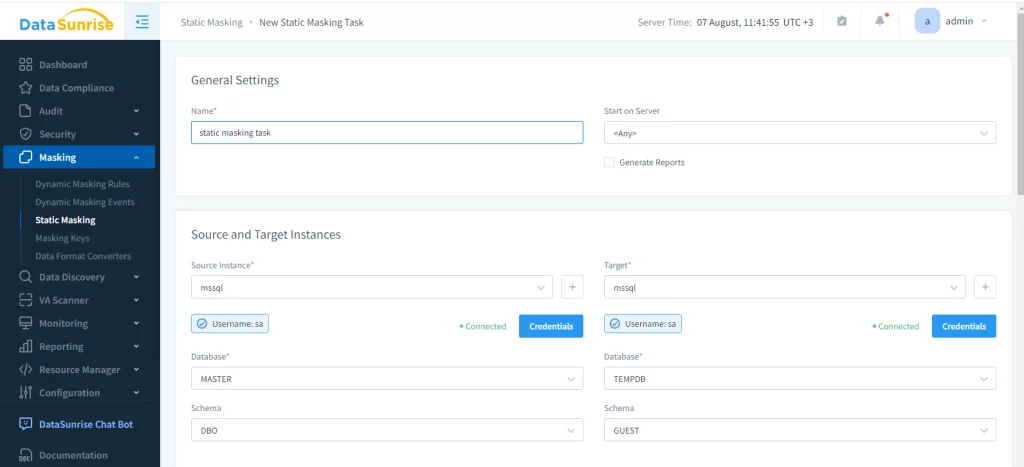
Next, a static masking task must be created. First, select the source database and schema to be masked, then specify the target database. The target, obviously, must be MSSQL too. Before masking, all data in the target schema will be truncated, therefore a user must be careful before proceeding.
Finally, the masking rules are to be set up. Just like in dynamic masking, a user selects tables to be masked and masking algorithm.
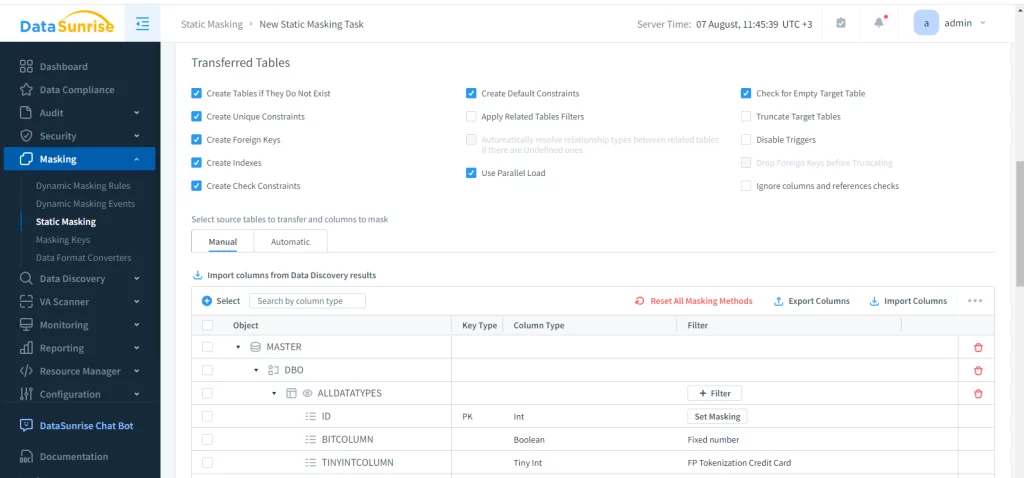
All that’s left is to configure the masking rules and run the task. This will create a fully functional dummy-storage will relations intact, but necessary data hidden.
Best Practices and Challenges
When implementing static data masking, it’s important to follow best practices. Ensure that related data is masked consistently across different tables to maintain referential integrity. Strive to preserve the original data format to help applications continue functioning correctly. Choose masking values that resemble real data for more accurate testing and analysis.
Document your SQL Server static data masking procedures clearly. This practice ensures consistency and helps with auditing and compliance efforts. Regularly review and update your masking rules, especially when database structures change or new types of sensitive data are introduced.
However, static data masking also comes with challenges. Complex data relationships can make it difficult to ensure consistent masking across related tables. Finding the right balance between data protection and usability is crucial, as overly aggressive masking might render the data useless for certain purposes. For very large databases, the process of creating a masked copy might require significant storage and processing resources.
Tools and Solutions
While custom scripts can handle static data masking, several tools can streamline the process. SQL Server Data Tools (SSDT) includes data masking capabilities that integrate with SQL Server projects. Various third-party solutions provide advanced features for static data masking in SQL Server. For organizations with specific requirements, custom PowerShell scripts can automate the static data masking process.
As data protection needs continue to evolve, we can expect advancements in static data masking capabilities. Potential developments include AI-driven masking algorithms, improved integration with cloud-based SQL Server instances, and enhanced performance for masking large-scale databases.
Don’t forget to visit DataSunrise website and schedule a demo session to learn everything our team has to offer.
Conclusion
Static data masking in SQL Server provides a powerful tool to protect sensitive information while maintaining database functionality in non-production environments. By understanding different masking techniques, implementing best practices, and addressing potential challenges, organizations can significantly enhance their data security posture. As threats to data privacy continue to evolve, SQL Server static data masking remains an essential component of a comprehensive security strategy for database management.
