
Information Security
Nowadays database security is as relevant as ever. Internal operating information of a company, personal employee and customer data, financial information, intellectual property, market researches, analysis of the competitors’ activities – those are the most important data for cybercrooks. This information is usually keeping in a corporate database. So that is why it’s important to take care of database security in advance.
Database security – is a set of collective measures to protect and secure a database or database management software of a company from tampering or unauthorized acts. Of course, to fully understand the definition, let us have a look at various information systems and information security concepts.
An information system is known as an integrated set of components of data that is collected, stored and processed or transformed and working together to produce and generate accurate information.
The information system consists of the following components:
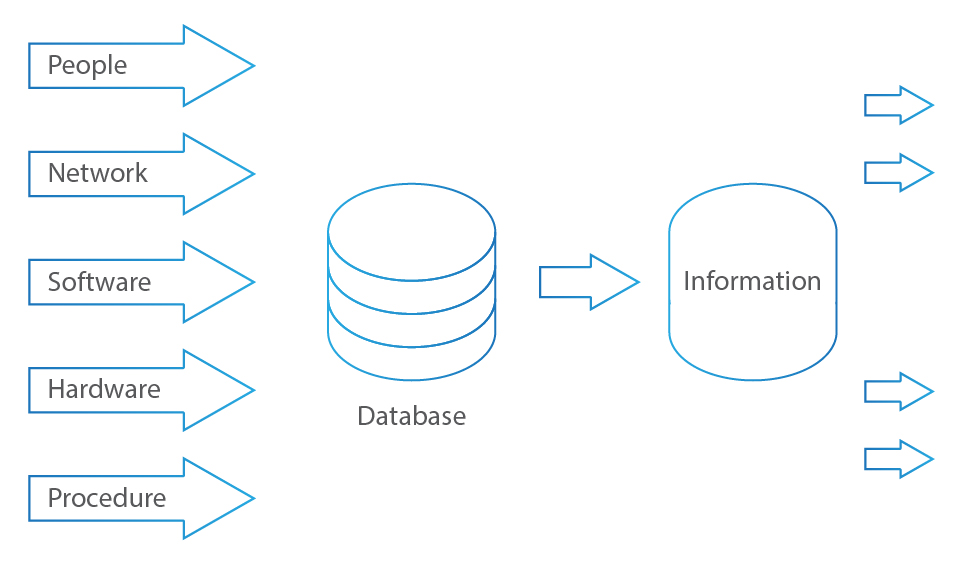
- Data – Facts and statistics collected together for future reference, processing or analyzing
- Procedures and Functions – Includes set of procedures and policies, guidelines, business rules, adopted in a system or used as a part of a system to influence and determine all major decisions and actions
- Hardware – Tools, computer systems or devices, a physical part of a computer system or electronic device
- Software – Application code, languages used to develop code, the programs and other operating information used by a computer, database management system, operating system used, any other utilities or tools
- Network – A communication infrastructure to connect client processes to the system
- People – Users, managers, business analysts, programmers, system analysts, database administrators, and system administrators
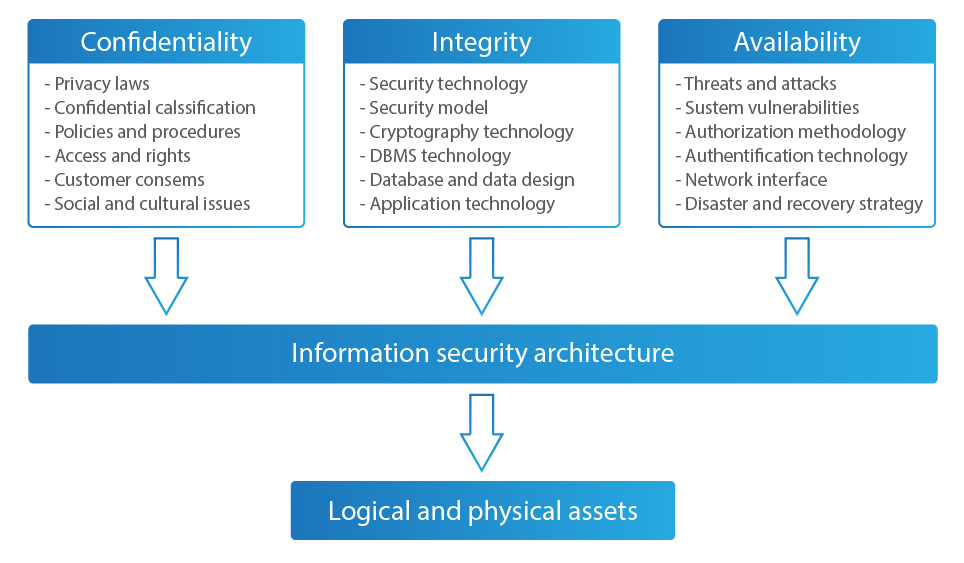
Information security consists of the procedures and measures protecting each element of the information system involved in producing an information system. The concept of information security is based on the C.I.A. triangle, where “C” stands for Confidentiality, “I” for Integrity, and “A” for Availability, is designed to guide policies for information security in a company.
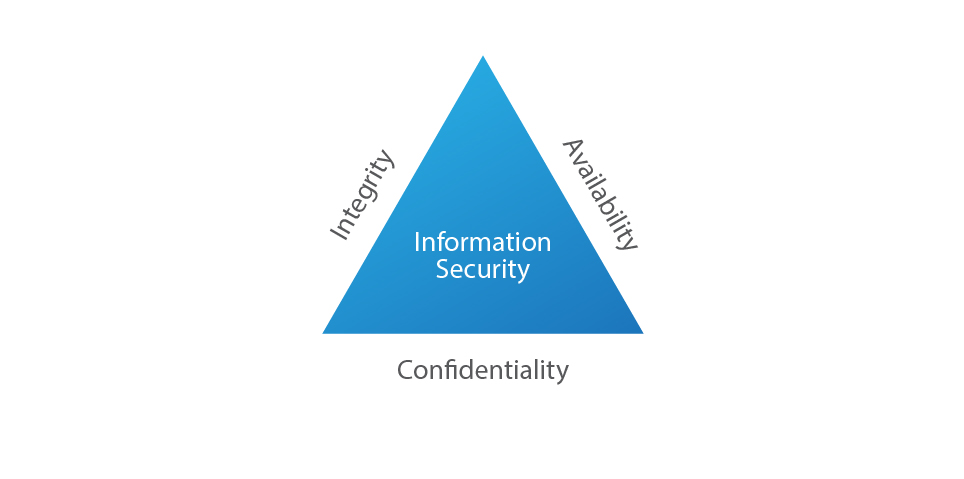
This C.I.A. triangle is a framework for protecting information.
Confidentiality refers to prevent unauthorized individuals from knowing or accessing secret information. Also, it’s the process of protecting confidential information and revealing secret information only to authorized users by means of classifying information.
The integrity aspect of information security is very important because it pays your attention to the most valuable asset, data, which in turn becomes information.
The availability principle refers to the ability of individuals who are authorized to access the information, and the system should determine what an individual can do with that information in a correct format in a specified location.
Mainly information systems are classified into three distinct categories in organizations:
- Transaction-processing systems – for lower-level management
- Decision support systems – for middle-level management
- Expert system – for upper-level management
Depending on the user’s rights, to what level of the database he has access, he can get requested information.
As you can see, implementing proper access control is a vital part of database security, because to protect a valuable data kept in the database you need to know various security access points that can make your database vulnerable.
There are seven security access points:
- People – who have permissions and privileges to access data files, databases, servers, networks, applications, networks, and data.
- Applications – Including design and implementation, applications have privileges and permissions provided to people. Providing security privileges, it’s necessary to be extremely cautious.
- Network – It’s necessary to protect your network and make it available only to applications, databases, and operating systems.
- Operating system – It is an authentication to the system, kind of entrance to data. User needs to log on and must be verified to access the data. Bad protection or poor security measures at this point can be the cause of most security violations.
- Database Management System.
- Data files – It is very important to protect data files using permissions and encryption from being accessed by unauthorized individuals.
- Data.
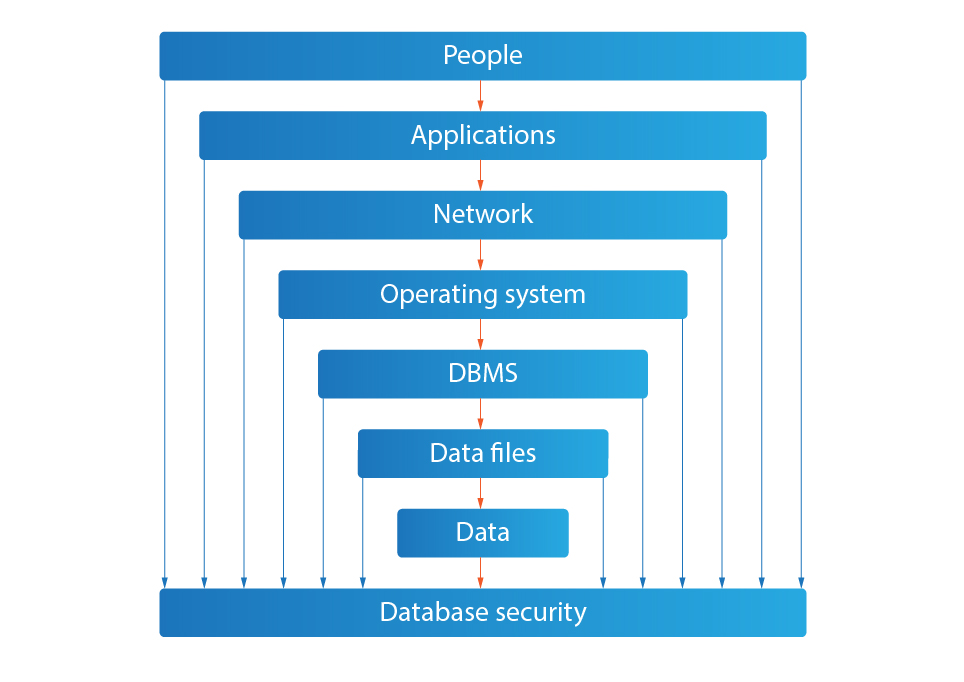
The people element is the biggest part. There is a huge community of individuals who access data – visitors, clients, users, managers, developers. That is why security efforts should be sent to decreasing the risks at the people access points because all these people increase the possibility of endangering the security data.
Database security plays an essential role in automatization of control over users’ actions, who work with data, on protection against internal and external threats, and increasing reliability of database performing.
